
Cybercrime has officially entered its “hold my beer” era. In this episode, we break down the FBI’s annual Internet Crime Complaint Center report and the numbers are equal parts fascinating and horrifying. We’re talking over $20 billion in reported losses, exploding ransomware attacks, AI-powered scams, fake charities, romance cons, business email compromises, and criminals who apparently work harder than some middle managers. It’s a practical, eye-opening look at how modern scams actually work — and why staying skeptical online may now qualify as a survival skill.
In this episode:
Same Hacks, Bigger Losses, Smarter Scams – Ep 560
Today’s Episode is brought to you by:
Kardon
and
HIPAA for MSPs with Security First IT
Subscribe on Apple Podcast. Share us on Social Media. Rate us wherever you find the opportunity.
Great idea! Share Help Me With HIPAA with one person this week!
Learn about offerings from the Kardon Club
and HIPAA for MSPs!
Thanks to our donors. We appreciate your support!
If you would like to donate to the cause you can do that at HelpMeWithHIPAA.com
Like us and leave a review on our Facebook page: www.Facebook.com/HelpMeWithHIPAA
When you see a couple of numbers on the left side of the text below click that and go directly to that part of the audio. Get the best of both worlds from the show notes to the audio and back!
Same Hacks, Bigger Losses, Smarter Scams
[00:42]Update from last week – the two cybersecurity professionals caught in the scam to play both sides of the negotiation for ransomware payments were sentenced just after we recorded. They could get up to 20 years in jail but they got 4 years. The ring leader doesn’t get sentenced until July.
In the circles I know of cybersecurity people there aren’t many that would do well with 4 years of jail time. This could be a deterrent but the ring leader should get at least 8 years if not more, IMHO.
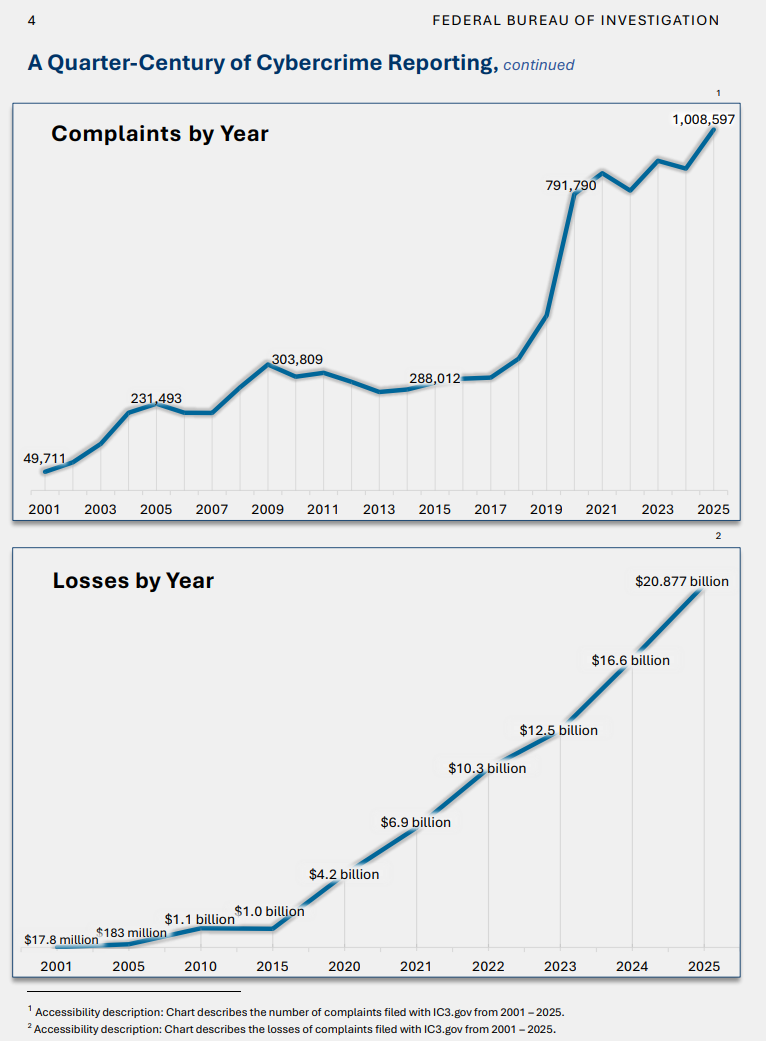
[03:17]Speaking of crimes….. The annual IC3 Report that is the FBI Internet Crime Complaint Center actually. Their 25th annual report and the trends they had to show for those years look very painful.
Let’s first take a look at the number of complaints by year and amount of losses by year. It’s pretty staggering.
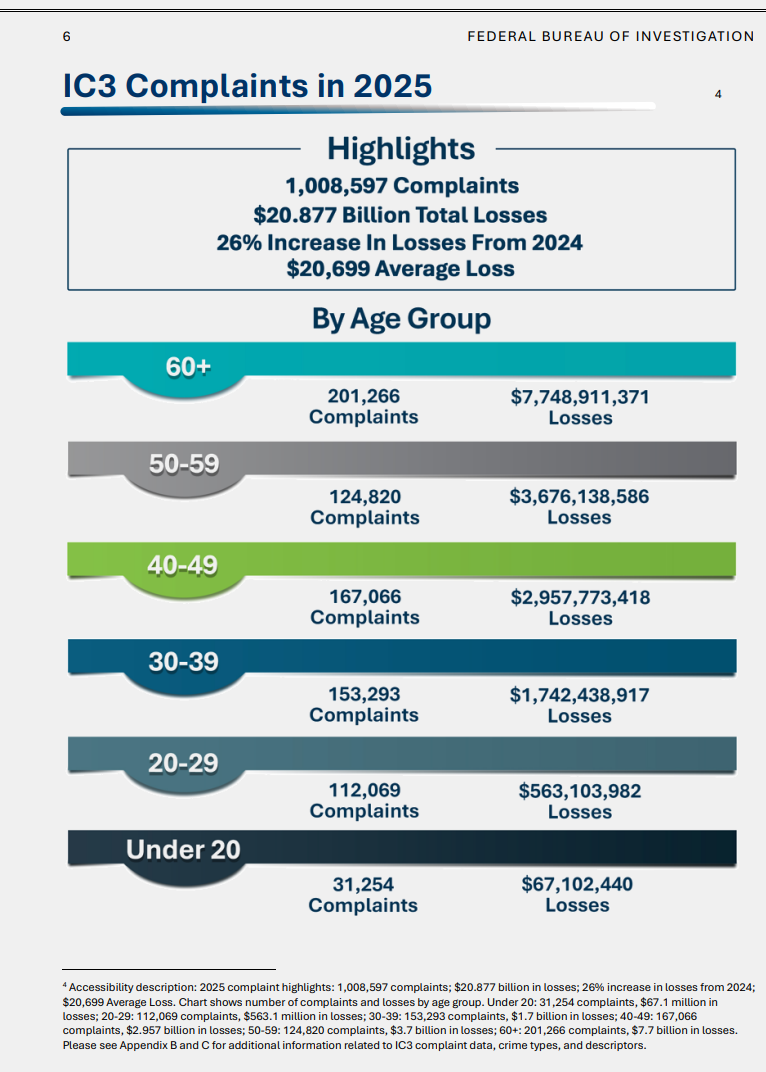
Now let’s break down the previous two charts by age group – how many complaints were filed by age groups and the dollar amount losses for each.
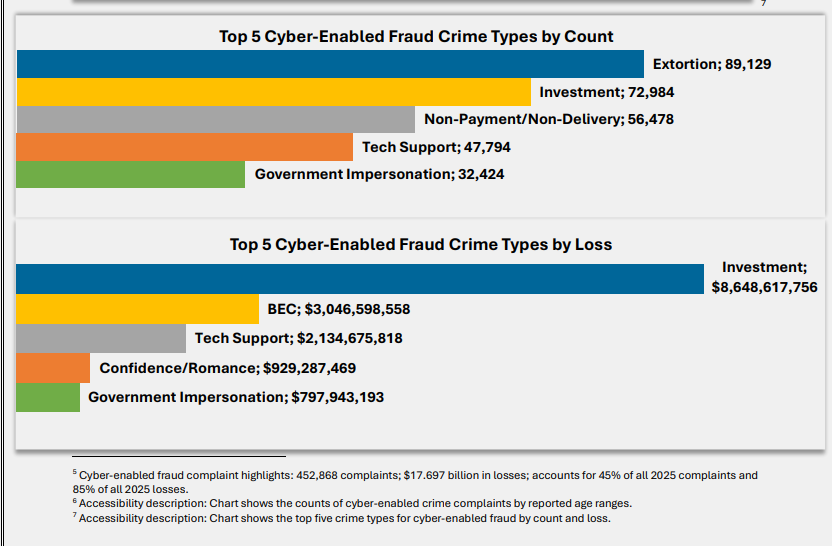
Cyber Enabled Fraud Crime
[14:11]The top 5 types of cyber-enabled fraud crime by number of complaints and the associated losses are incredible.
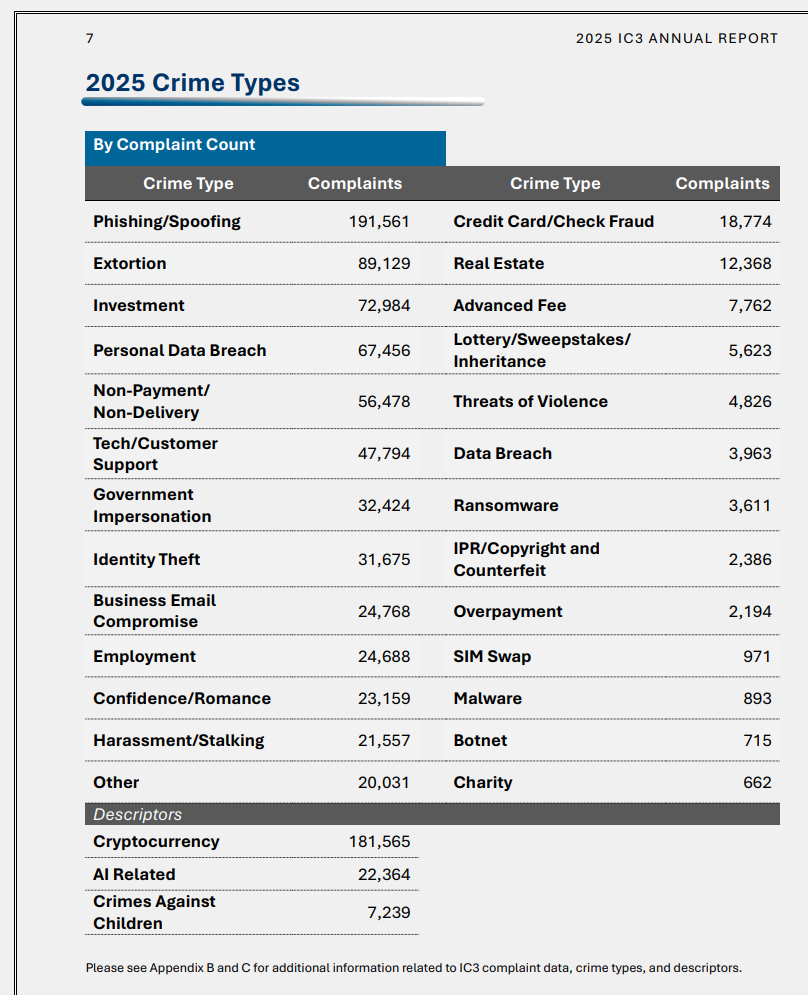
2025 Types of Crime
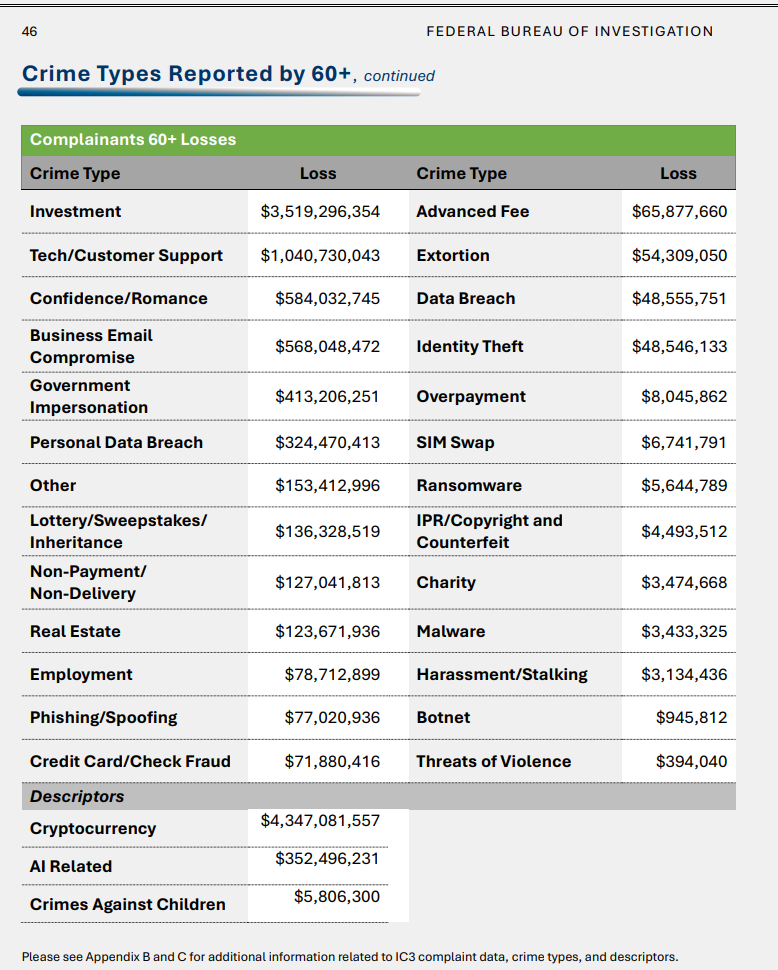
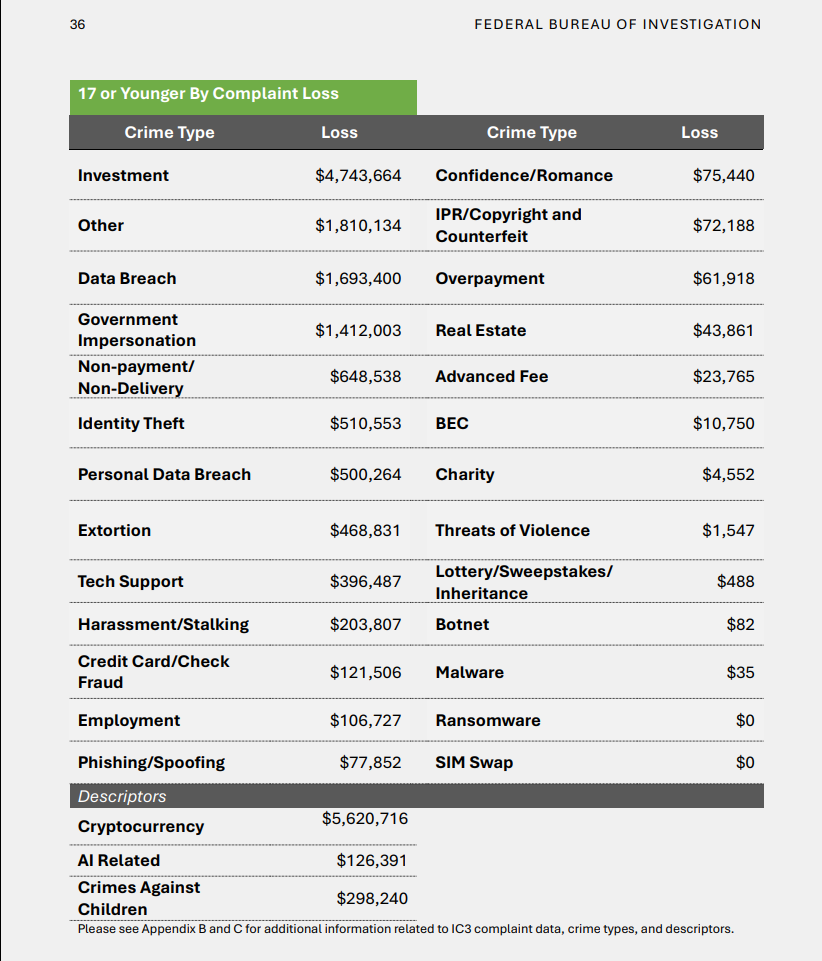
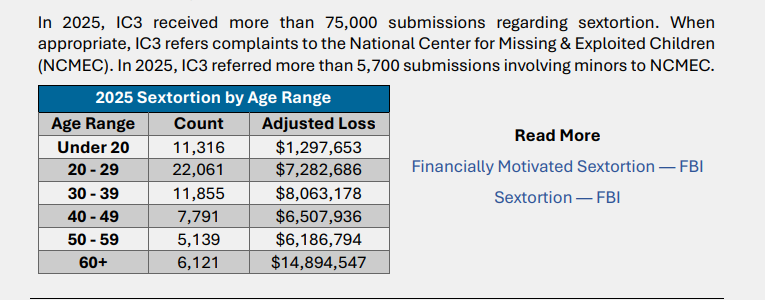
[23:51]Again we’ll look at the number of complaints vs the amount of losses overall and then by age groups.
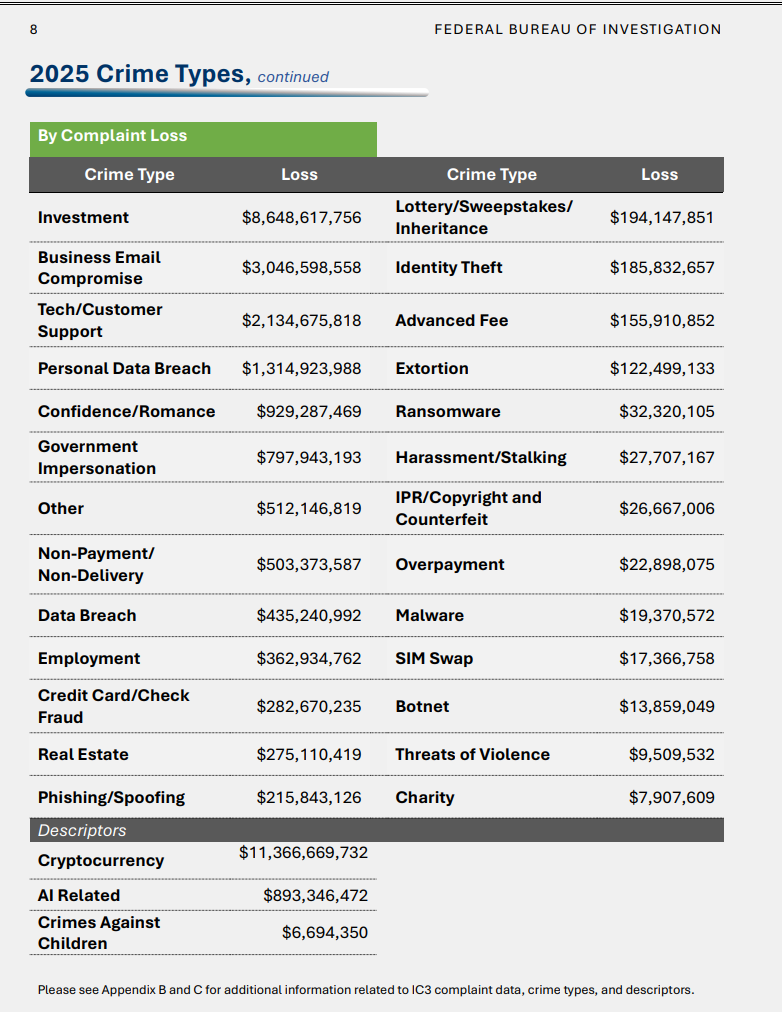
Here are the charts of losses by the 60+ and 17 and under age groups.
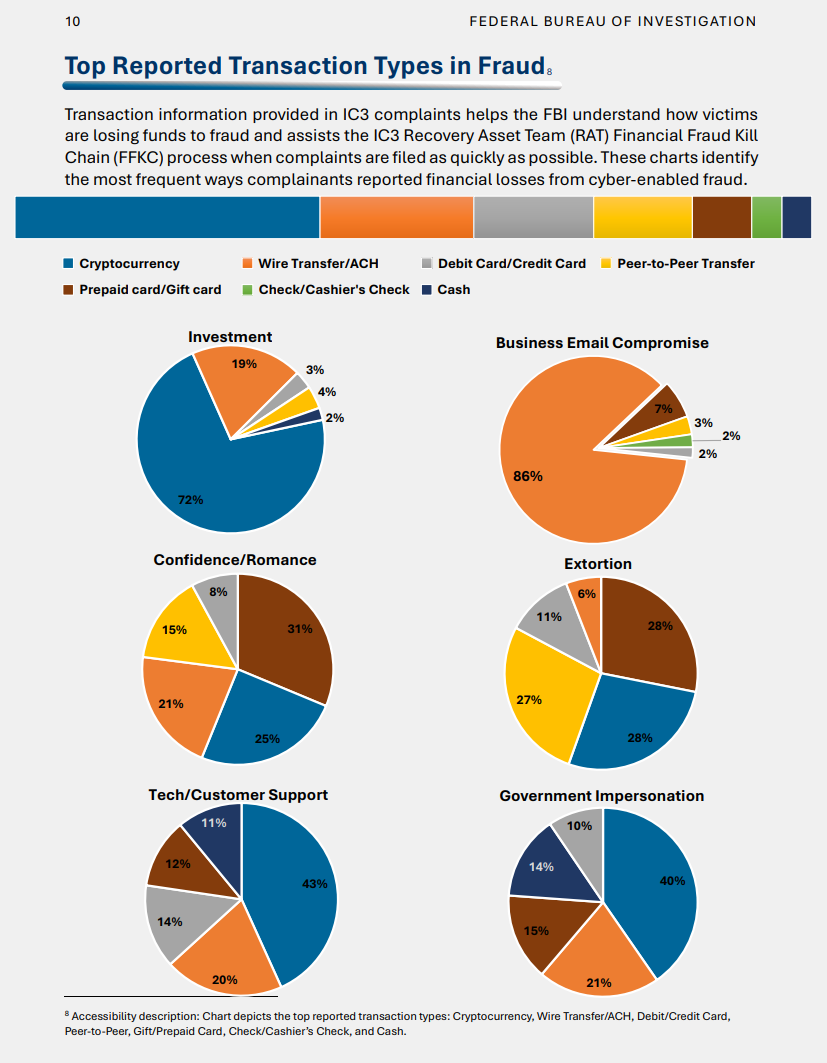
Top Reports Transaction Types by Fraud
[34:27]This tells us how people are losing money to fraud.
Ransomware
[42:26]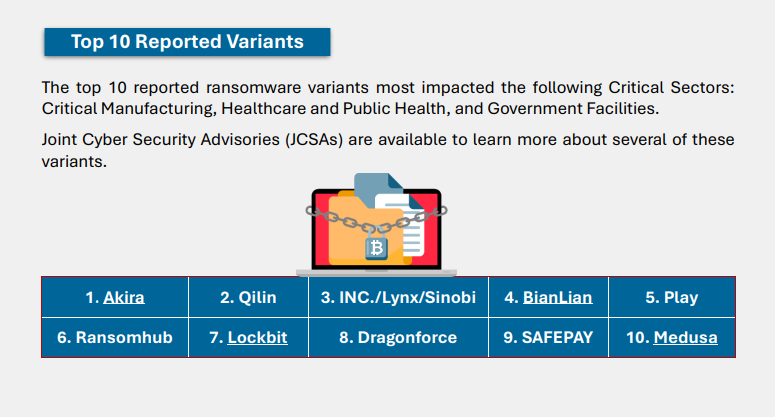
“Attackers aren’t using new techniques – they’re exploiting known weaknesses, and healthcare is paying”
The problem is getting worse for a simple reason: attackers are succeeding – and once inside, the cost of disruption often forces difficult decisions. Ransom payment rates range from 68% to 72%, making the sector one of the most reliable and profitable targets for cybercriminals.
This isn’t about sophisticated, never-before-seen threats. Every vulnerability exploited in these attacks is already listed in the U.S. government’s Known Exploited Vulnerabilities (KEV) catalog.
Attackers are repeatedly exploiting unfixed, well-documented weaknesses, allowing them to scale attacks quickly using proven, repeatable methods.
The report analyzed 592 incidents across 94 ransomware groups between January 2025 and February 2026:
59% of attacks involved ransomware
56% targeted U.S.- based organizations
Securin identified 29 actively exploited vulnerabilities, with a clear pattern:
- Authentication bypass is the most common entry point
- VPN and remote access systems account for roughly one-third of initial access
- Attackers often exploit vulnerabilities long after they are disclosed and patchable
In many cases, access to healthcare systems is purchased for as little as $2,000 to $50,000, lowering the barrier to entry.
Cyber Threats to Critical Infrastructure in 2025
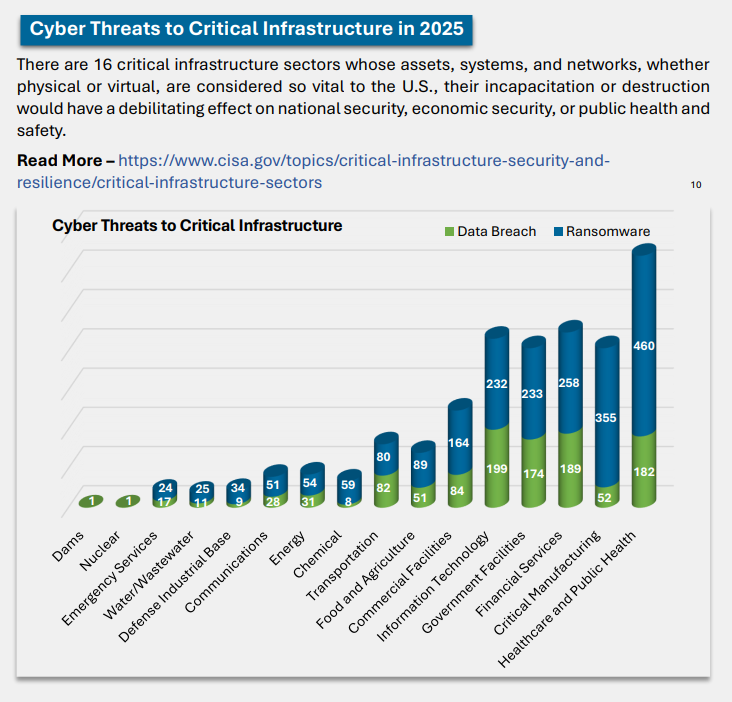
IC3 Recovery Asset Team or IC3 RAT – has worked to recover assets in many incidents including freezing funds for the victims then track the transactions.
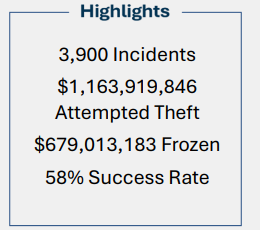
When people ask why you should contact the FBI when these things happen – this is why.
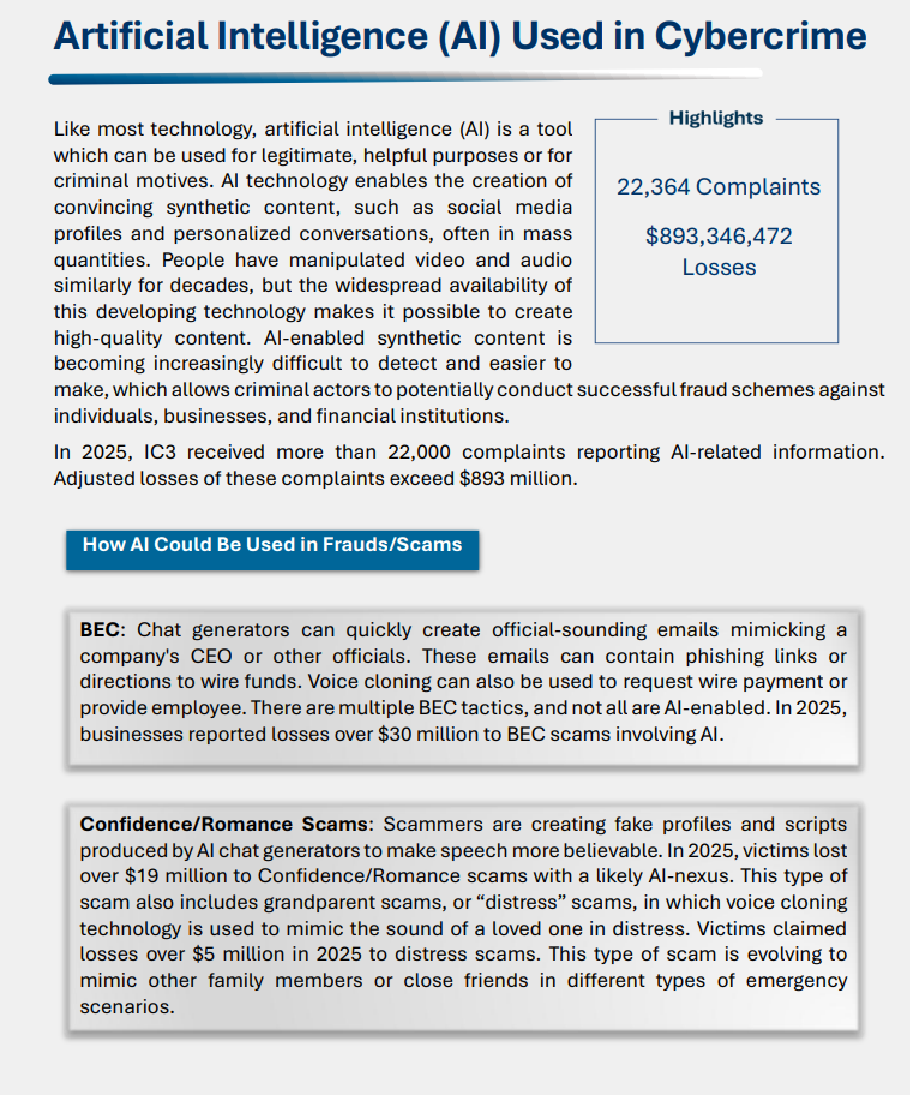
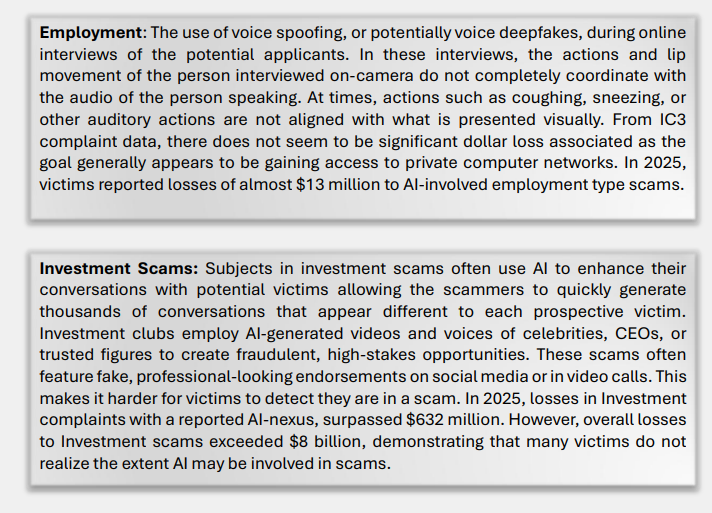
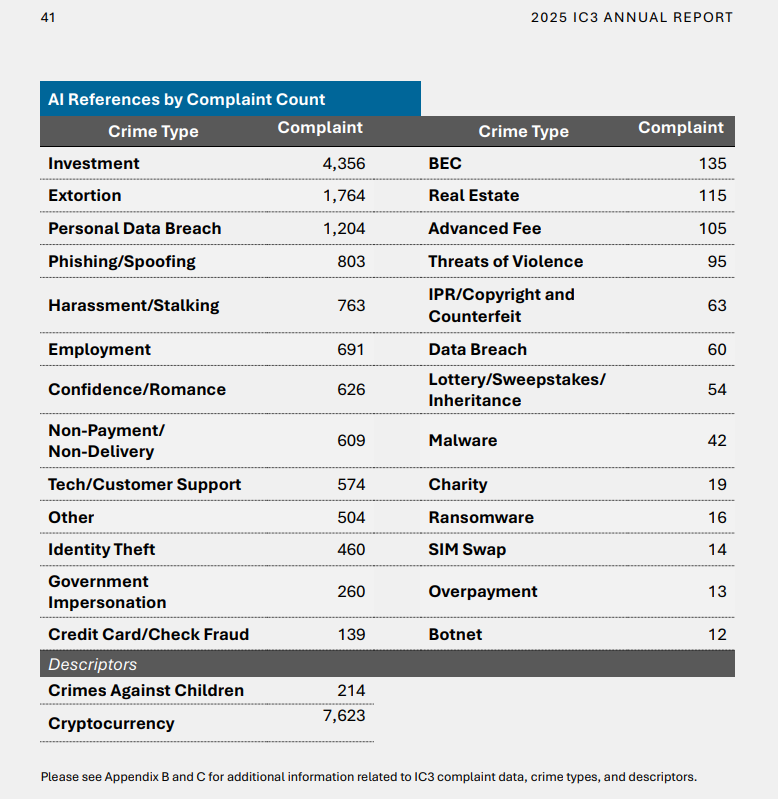
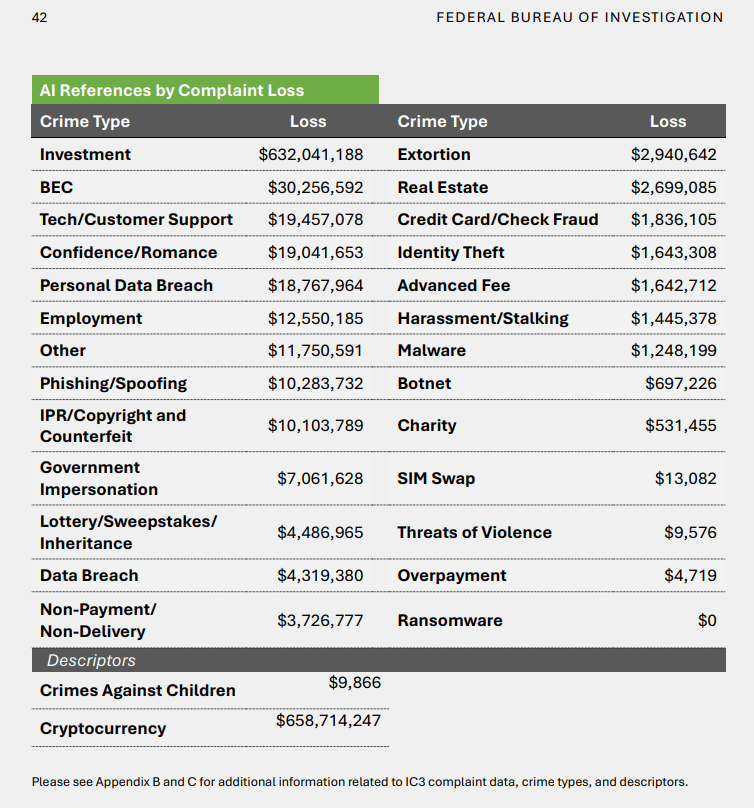
AI used in Cybercrime
[48:01]And we must end on AI – of course…
If this episode proves anything, it’s that cybercrime is no longer a niche IT problem — it’s a full-contact life problem. The attacks are smarter, faster, more personal, and increasingly powered by AI, but the goal is always the same: get your money, your data, or both. Whether it’s ransomware hitting hospitals every few hours or scammers convincing people to wire life savings to fake investments, staying alert has never mattered more. So maybe the real modern superpower is learning to pause before you click, pay, reply, or panic.
Remember to follow us and share us on your favorite social media site. Rate us on your podcasting apps, we need your help to keep spreading the word. As always, send in your questions and ideas!
HIPAA is not about compliance,
it’s about patient care.TM<;/span>
Special thanks to our sponsors Security First IT and Kardon.


