
Privacy and security should be a part of all organizations day-to-day activity and company culture. But how do you know how mature your privacy and security program really is? By using one of the many maturity models. Today, we are discussing the new DoD Cybersecurity Maturity Model Certification (CMMC) that breaks controls into levels so you can see what implementation level or maturity level your program is at any given moment.
In this episode:
Maturity Model Matters – Ep 308
Today’s Episode is brought to you by:
Kardon
and
HIPAA for MSPs with Security First IT
Subscribe on Apple Podcast. Share us on Social Media. Rate us wherever you find the opportunity.
The HIPAA Boot Camp
Virtual Edition Aug 17-19, 2021
Great idea! Share Help Me With HIPAA with one person this week!
Thanks to our donors. We appreciate your support!
If you would like to donate to the cause you can do that at HelpMeWithHIPAA.com
Like us and leave a review on our Facebook page: www.Facebook.com/HelpMeWithHIPAA
If you see a couple of numbers on the left side you can click that and go directly to that part of the audio. Get the best of both worlds from the show notes to the audio and back!
Listener message:
Hi Double Ds,
Lol. Your “I told you so phrase,” should be “DD done told y’all!”
Love your show!
Best Regards,
Andrea
Thanks for your message, Andrea. We appreciate it.
HIPAA Say What!?!
[08:40] Today ,we are going to cover a few different HIPAA points in our HIPAA Say What!?! segment:Follow up on status of Scripps attack.
Scripps Health Attackers Stole PHI of 147,000 Patients
Notifications have begun. Good news is they say the patients being notified were included in documents exfiltrated from outside the EHR itself. This whole case is a reminder for everyone to think about more than your backup when it comes to planning for these incidents.
- Create a communications plan… for staff, partners, patients and external contacts like law enforcement and the news stations.
- Plan to treat patients without access to systems for at least 10 days, but note that number keeps growing.
- Do not assume all PHI is in your EHR. Documents are a treasure trove of information about your business AND your patients. The minute you think you don’t have PHI somewhere is the minute you make a plan to confirm that with regular audits.
- Prepare to notify patients as soon as possible. These patient messages on FB made it clear they thought they should be notified during the attack. Communicate that to patients, but don’t drag it out when you are in the news. They are watching the clock.
- Know that recovery will take weeks and even months based on the number of days you are down – Scripps is learning that one right now.
We will continue to watch this. But, I am interested to see how long it takes for them to have their feet back under them fully. At least as much as we can learn about it. This is a huge system so there were bound to be issues when it happened. So far, it seems they are hanging in there very well. Best of luck to them as they take on this major challenge of recovery and repair.
We got news yesterday that another hospital system is dealing with an attack that apparently started on Monday. Talk about a tough way to start a new job, check out what is happening in Central Florida: New COO takes over at The Villages hospital as ransomware attack freezes computers.
Another right of access agreement
[24:56] The Diabetes, Endocrinology & Lipidology Center, Inc. has the honor of being the 19th group to make this list. The issue started with a patient complaint in August 2019 and ended with an OCR resolution agreement in June 2021. The investigation started in Oct 2019 and found that the West Virginia practice had, indeed, not provided the information to a woman asking for records about her son’s care.From the press release:
“It should not take a federal investigation before a HIPAA covered entity provides a parent with access to their child’s medical records,” said Acting OCR Director Robinsue Frohboese. “Covered entities owe it to their patients to provide timely access to medical records.”OCR Press Release DELC
The $5,000 payment and 2 year CAP are pretty standard. We don’t get to learn much more about the details. I really do wish we could learn more about why the practice hadn’t provided the records in these cases. I specifically want to know if this was because someone didn’t know they were violating the law or because they actually believed they were doing the right thing.
It’s HIPPPPAAA again!
[29:36] Just one more thing. It is so hard to read news stories without having a moment. As I was trying to read the news about the new SCOTUS ruling on the Computer Fraud and Abuse Act ( Supreme Court Votes to Limit Computer Fraud and Abuse Act) it didn’t take long before someone thought about HIPAA. If you think you would say “I just can’t keep reading” you can relate to how I was feeling at that point.
Maturity Model Matters
[32:30] We have discussed maturity assessments more than once on our show. Both of the main ones happened in 2019, which we know was a whole different world than what we live in today. In case you missed them, here are links to those podcasts:Maturity Assessments – Ep 206 and 6 Signs Of HIPAA Program Maturity – Ep 222
But this year, and each of the coming years, we will all be discussing something called the CMMC more and more as time goes on. The use of this model is being discussed all over the cybersecurity world because it breaks controls into levels so you can see what implementation level or maturity level your program is at any given moment. There are several articles out there that try to explain what the whole thing is about. My favorite one is done by CSO Online – CMMC explained: What defense contractors need to know.
As the title suggests right away, this maturity model is published by the DoD and required for all defense contractors to begin implementing. Yes, we are all about HIPAA. However, this is the direction we know things need to go towards in healthcare as well as any industry that takes cybersecurity seriously.
The CMMC defines varying requirements that relate to different maturity levels for your program. To have any kind of contract in this industry, you will eventually need to be certified with at least a Level 1 CMMC. Eventually, to have access to classified information of any sort, you will need to reach Level 3 and the major folks will have to reach all the way to Level 5 to stay in the game.
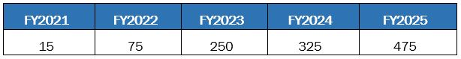
The program is being rolled out starting this year with a certain number of contractors selected to meet the Level 1 requirements. Each year they will add more contractors and higher levels. Until all contracts will start requiring some level of certification.
They haven’t finalized how the certifications will happen yet. You can’t even take the course to become a certified assessor until this fall. But, don’t doubt that this will be discussed in all corners of the industry as the roll out continues.
What are CMMC levels?
[36:17] The levels assume you are doing something because there isn’t a zero level. It says if you have everything required for Basic Cyber Hygiene, you are Level 1. Intermediate is Level 2, Good Cyber Hygiene is Level 3.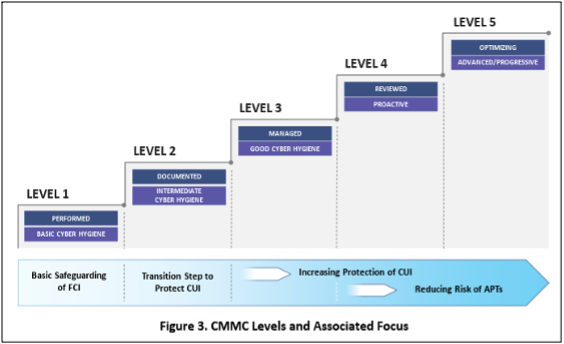
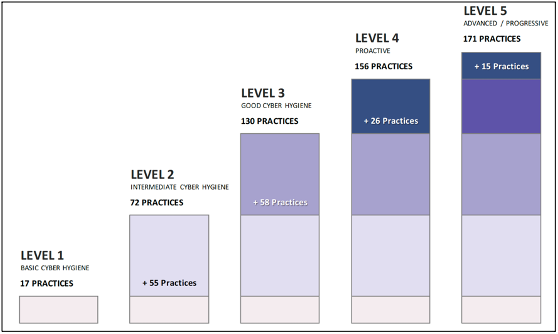
Didn’t we just talk about cyber hygiene and how there are several layers of it? In this case there are 17 Cybersecurity Practices considered to be Basic Cyber Hygiene. Level 2 jumps to 72 practices. By the time you’ve hit Levels 3 – 5, you can prove you follow 130, 156 and 171 practices respectively.
A very specific note to point out from the Assessment guide:
What about healthcare maturity models?
[42:23] Last fall, HC3 did a presentation on using some version of a maturity model for healthcare. There is no doubt it would make sense to do some sort of implementation along these lines in healthcare. Maybe that is what we end up doing in 405d but who knows at this point. It just makes sense. Granted the NIST CSF has their implementation tiers that are something in this ballpark, but the CMMC is much more specific.We have been doing this for years but using my own formula. We look at the threat and vulnerability to ask what is your plan first. Then, how well have you done getting the documentation, training, and incident response plans in place to make that happen.
I am definitely looking into how we can apply the CMMC concepts to our HIPAA assessments. Our model expects that you must be at least at what would be Level 3 here to be following HIPAA in the most basic sense. I found it very interesting that you must reach that level to get a contract with access to confidential information. Sounds like there is a lot in sync from that perspective. Honestly, the goal to be at Level 4 is what all companies should desire today, but if we can get them all at a Level 3 everything would be so much better in our cybersecurity world.
In a future episode, we will discuss what it takes in more detail to get to those CMMC levels. For now, we just need to get the terms out there so you can be prepared for conversations about it. We don’t want our listeners to be out of the loop when these conversations start happening!
Remember to follow us and share us on your favorite social media site. Rate us on your podcasting apps, we need your help to keep spreading the word. As always, send in your questions and ideas!
HIPAA is not about compliance,
it’s about patient care.TM
Special thanks to our sponsors Security First IT and Kardon.


