
Cybersecurity is a big challenge for all businesses these days. Regardless of the size of the business or industry it’s in, hackers are continuously trying to exploit weaknesses to gain access to networks and data. NIST and CISA have some new resources and guides that can help small and medium size businesses face the growing cyber threat.
In this episode:
SMB Cyber Resources – Ep 410
Today’s Episode is brought to you by:
Kardon
and
HIPAA for MSPs with Security First IT
Subscribe on Apple Podcast. Share us on Social Media. Rate us wherever you find the opportunity.
Great idea! Share Help Me With HIPAA with one person this week!
Learn about offerings from the Kardon Club
and HIPAA for MSPs!
Thanks to our donors. We appreciate your support!
If you would like to donate to the cause you can do that at HelpMeWithHIPAA.com
Like us and leave a review on our Facebook page: www.Facebook.com/HelpMeWithHIPAA
If you see a couple of numbers on the left side you can click that and go directly to that part of the audio. Get the best of both worlds from the show notes to the audio and back!
Thanks to our donors.
HIPAA Say What!?!
[02:36] AHA Letter to OCR on HIPAA Privacy Rule, Online Tracking GuidanceFederal Register :: HIPAA Privacy Rule To Support Reproductive Health Care Privacy
The article states that Aria patients were notified of the data breach 18 Months after a breach was discovered. The article also states that, under the HIPAA Breach Rule, covered entities are required to report a breach to affected individuals without unreasonable delay and no later than 60 calendar days from discovery when the breach affects 500 or more individuals. This is wrong.
So, let’s clear this up. You have to always notify patients of a breach of their data within 60 days. Period. Full stop. When notifications are required to be done to the media and HHS are the ones that vary based on the number of people affected. If it’s less than 500, the media doesn’t need to be notified and HHS can be notified within 60 days after the end of the calendar year.
NY AG Settlement
[19:26] NY AG Recoups $550,000 from Erie County Medical Management Company for Failing to Protect Patients’ DataIn this case, Practice First is the business associate who had the data breach and then had to notify their covered entities. They had a firewall provider that released a new version of the software which patched a critical vulnerability. They never installed the software patch. The firewall was vulnerable for over a year and in November 2020 hackers exploited it.
Notification to 1.2 million individuals, including over 428,000 New York residents.
Yet again, this case is proof that it’s not just OCR that can come after entities that have a breach. The state’s attorney general office has the option under HITECH to be able to enforce HIPAA on behalf of their constituents. Not only did Practice First have to pay the state of New York $550,00 they also are required to “adopt measures to better protect personal information”.
Among other things, the NY settlement agreement states:
Listener questions
[32:55] Craig says: First of THANK YOU for your podcast. It helps me approach HIPAA in a non fear based manner. Is there a checklist product that I can purchase to guide my compliance efforts?Craig…. We don’t like checklists but if we were to make a list of things you should have:
- Make sure your SRA meets requirements outlined in OCR resolution agreements.
- Once it meets that, make sure you have a RM Plan that addresses everything in your SRA.
- Do a Gap Analysis to make sure you are meeting your HIPAA requirements and documenting them properly.
SMB Cyber Resources
[39:08] State-Aligned Actors Targeting SMBs Globally – HealthcareInfoSecurityThis article goes through some pretty interesting information on how the APTs (advanced persistent threats) are being done and why the small and medium businesses are the ones they’re attacking. They’re doing it to get to the bigger ones because you are now the number one weakness. That’s why we say over and over that you are not “too small” or “don’t have anything of value” for hackers to attack you. You do and they can use you to get to bigger fish. These are just the kinds of reasons why NIST has a new cybersecurity initiative.
NIST Launches Cybersecurity Initiative for Small Businesses.
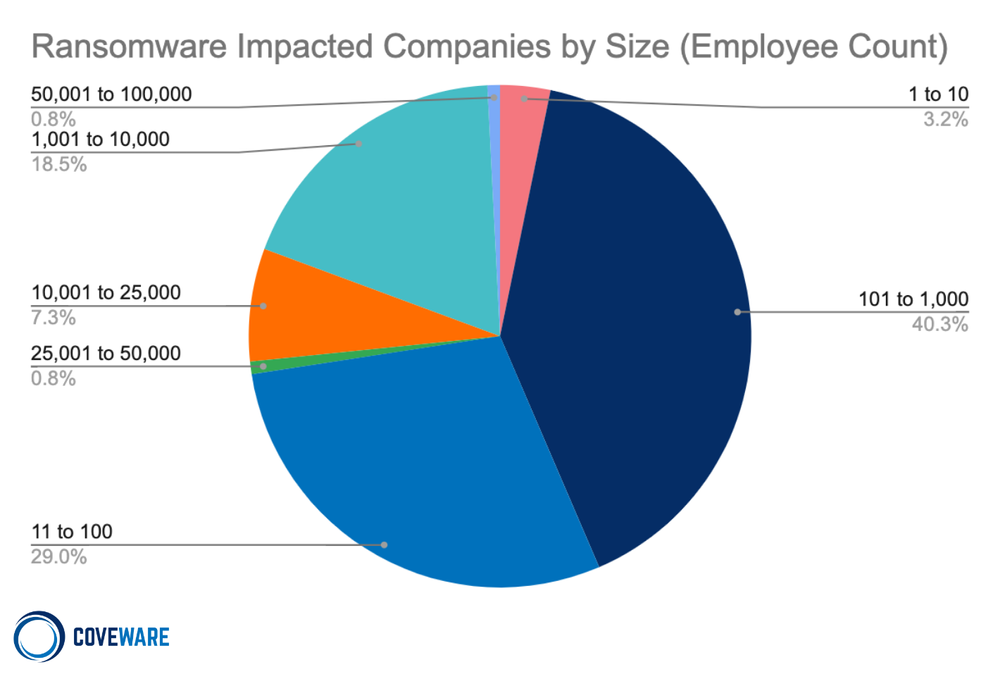
Take a look at the chart below. Around 70% of the ransomware impacted companies had less than 1,000 employees. NIST has created its Small Business Cybersecurity Community of Interest (COI) to help smaller organizations face the growing cyber threat. NIST has provided some good resources and tips for small businesses.
The NIST and CISA resources are great and we definitely need them, but I think that sometimes with guides like these they are difficult for the small and medium size business leaders to understand and execute. We’ve got to find a way to streamline all this information that is coming at us at this fast pace. It’s not only hard to keep up with all the changes, but also the breadth and depth of everything that is involved in protecting a business from cyber attacks is immense. Business leaders cannot do it properly and effectively without having a dedicated IT / MSP company.
Small and medium size businesses face a lot of cybersecurity challenges and often find it difficult to protect their networks and data from cyber threats, especially if they don’t have a dedicated IT/MSP company helping them. The NIST, CISA and 405d (which we’ve talked about in a recent episode or two) resources and guides are a good place to start.
HIPAA is not about compliance,
it’s about patient care.TM
Special thanks to our sponsors Security First IT and Kardon.


