
If your small business still thinks that a dusty old firewall and a sprinkle of MFA is “good enough,” this episode is your cybersecurity reality check. Picture your company as a lemonade stand with a cash box—hackers are thirsty, and you’re wide open for business. We’re diving into why SMBs are now hacker playgrounds, how AI is helping cybercriminals get sneakier, and why your robot vacuum may be more security-conscious than your network gear. It’s everything you didn’t want to know about being a prime target—served up with a twist of humor, a splash of horror, and a tall glass of truth.
In this episode:
Small, Breached, and Broke – Why Hackers Love SMBs – Ep 528
Today’s Episode is brought to you by:
Kardon
and
HIPAA for MSPs with Security First IT
Subscribe on Apple Podcast. Share us on Social Media. Rate us wherever you find the opportunity.
Great idea! Share Help Me With HIPAA with one person this week!
Learn about offerings from the Kardon Club
and HIPAA for MSPs!
Thanks to our donors. We appreciate your support!
If you would like to donate to the cause you can do that at HelpMeWithHIPAA.com
Like us and leave a review on our Facebook page: www.Facebook.com/HelpMeWithHIPAA
When you see a couple of numbers on the left side of the text below click that and go directly to that part of the audio. Get the best of both worlds from the show notes to the audio and back!
Small, Breached, and Broke – Why Hackers Love SMBs
[05:17]Why SMBs Are Hacker Happy Playgrounds
1. Weaker Defenses = Easier Entry
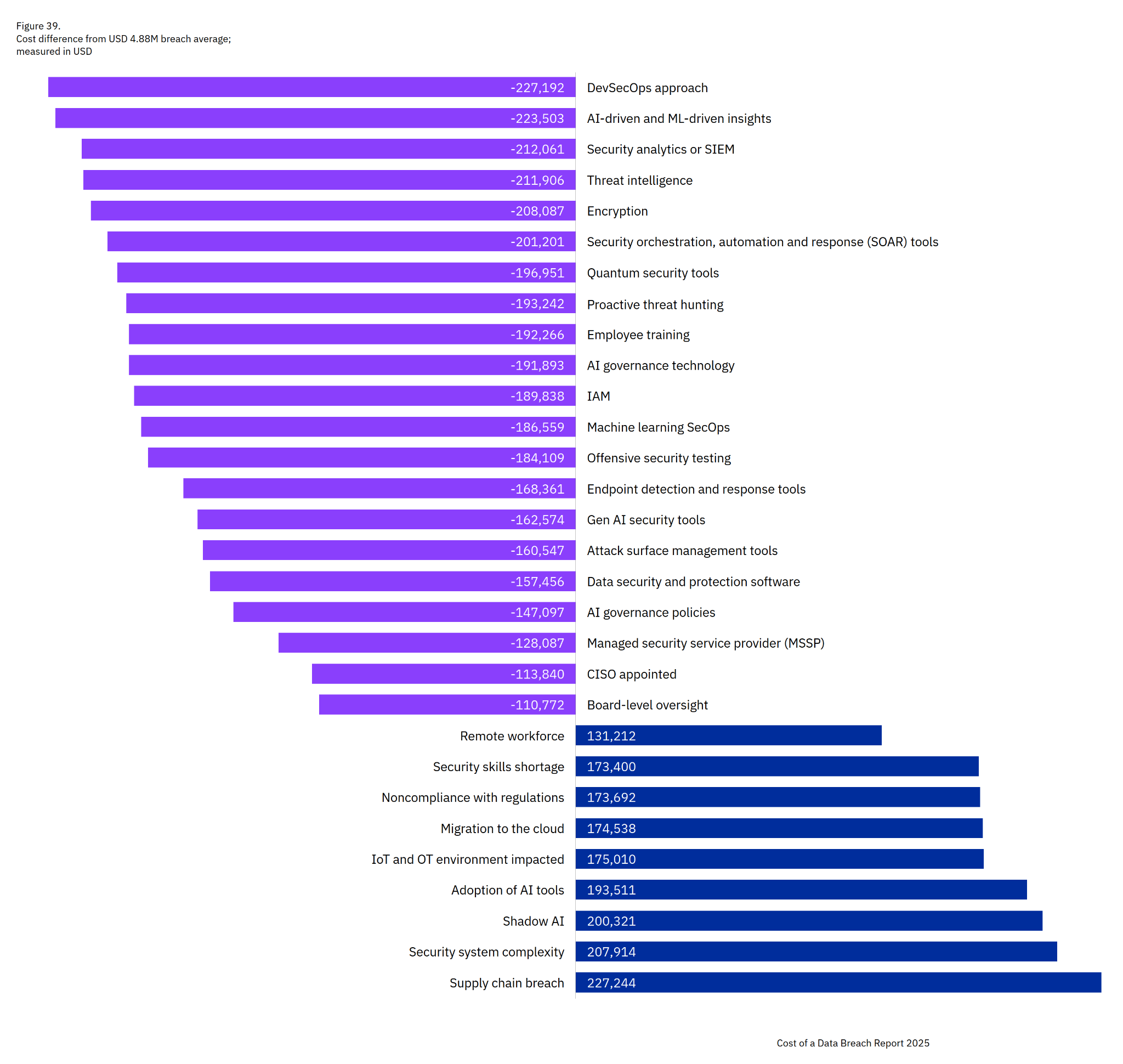
- SMBs often skip basics like MFA, patching, or logging because they don’t have the staff/budget.
- DBIR shows exploitation of vulnerabilities grew 34%, with edge devices/VPNs a prime target. SMBs often leave those exposed because they can’t patch fast enough.
2. Ransomware Pays Off (and Fast)
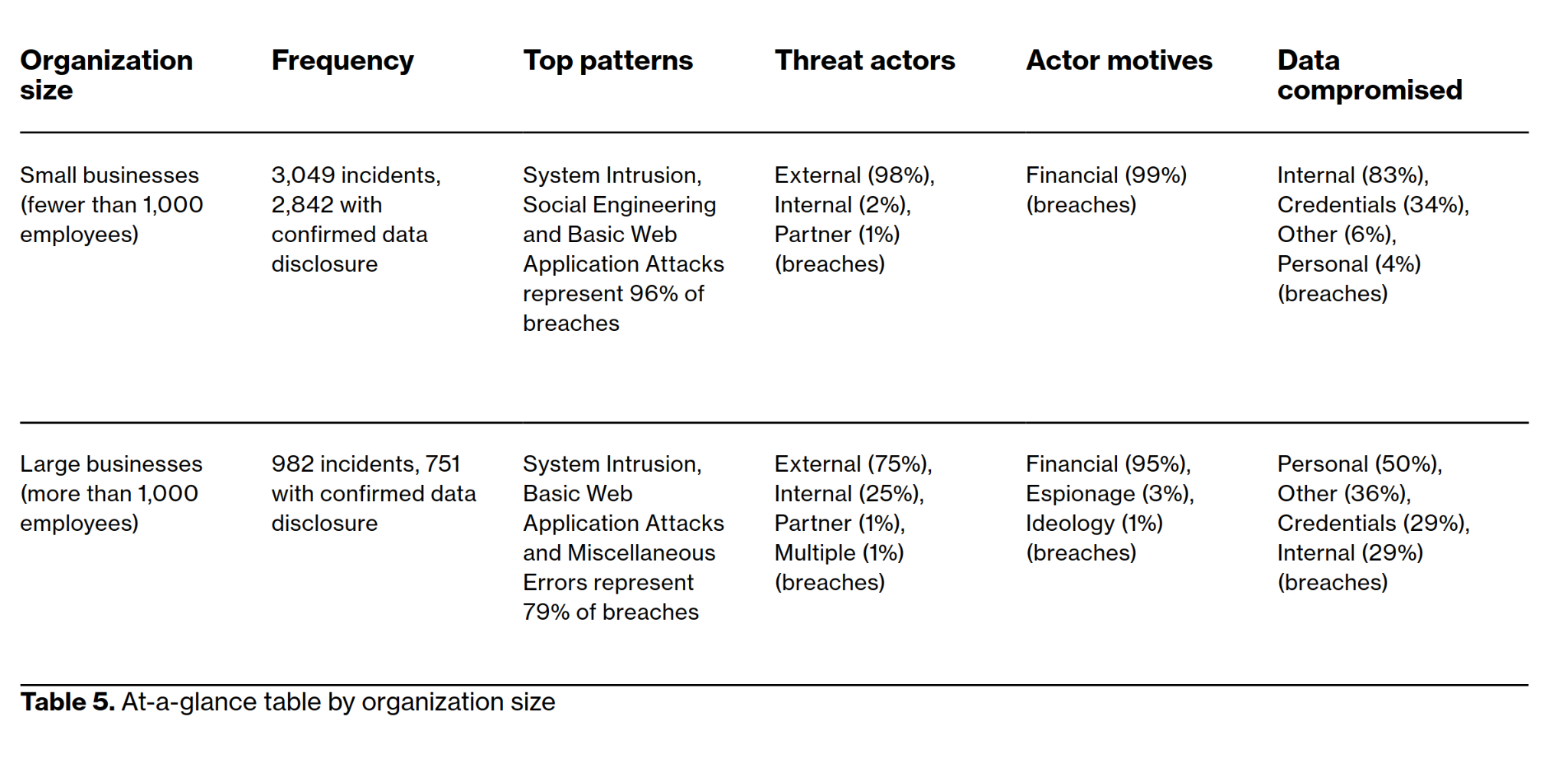
- DBIR: 88% of SMB breaches involve ransomware, versus 39% at large orgs.
- IBM: Average ransomware/extortion incident costs $5.08M, even when victims don’t pay.
3. Third-Party & Vendor Reliance
- DBIR: third-party involvement in breaches doubled to 30%.
- Small businesses outsource IT, billing, EHRs, payment systems — and attackers know compromising one vendor = dozens of SMB victims at once.
- Think: “Supply chain = hacker’s Costco.”
4. Human Element Weakness
- 60% of breaches involve the human element (clicking, misconfigurations, credential leaks).
- SMBs don’t always have security training, making phishing and social engineering more successful.
- IBM found phishing was the top initial attack vector (16%).
5. Less Oversight & Governance
- Shadow AI: 20% of orgs reported a breach tied to shadow AI, adding $670K per incident.
- SMBs often lack policies and controls to detect “rogue” tools.
- In other words: hackers exploit both the tech gaps and the culture gaps.
6. Big Impact, Small Resilience
- IBM: 65% of breached orgs are still recovering months (or years) later.
- Attackers know SMBs are more likely to fold, pay, or never fully recover — making them “soft targets.”
👉 In short:
Hackers love SMBs because they’re easier to break into, faster to monetize, and less likely to have strong defenses or recovery plans. Or, as you could frame it:
“Big companies are the Fort Knox of hacking. Small businesses? More like the lemonade stand with a cash box on the counter.”
Verizon 2025 Data Breach Investigations Report (DBIR)
If this episode has you eyeing your smart fridge suspiciously and wondering if your vacuum is spying on you—good. You’re paying attention. We’ve confirmed that SMBs are basically walking around with “hack me” signs taped to their backs. But hey, knowledge is power and encryption, MFA, and employee training are your new best friends. If you’re not actively securing your systems, you’re basically playing cybersecurity whack-a-mole with a blindfold on. How long do you think you’ll last? Now go forth, update your firmware, vet your vendors, and maybe stop using your cat’s name as a password.
Remember to follow us and share us on your favorite social media site. Rate us on your podcasting apps, we need your help to keep spreading the word. As always, send in your questions and ideas!
HIPAA is not about compliance,
it’s about patient care.TM
Special thanks to our sponsors Security First IT and Kardon.


