Securing older, legacy technologies from cyber threats is extremely important in today’s interconnected digital world. Older devices often lack the robust security features of modern counterparts, making them vulnerable targets for hackers seeking to exploit weaknesses. Today, we review HSCC’s Health Industry Cybersecurity – Managing Legacy Technology Security (HIC-MaLTS) guide that provides recommendations to address the legacy technology challenges facing healthcare.
In this episode:
Securing Older Technologies Still In Use – Ep 424
Today’s Episode is brought to you by:
Kardon
and
HIPAA for MSPs with Security First IT
Subscribe on Apple Podcast. Share us on Social Media. Rate us wherever you find the opportunity.
Great idea! Share Help Me With HIPAA with one person this week!
Learn about offerings from the Kardon Club
and HIPAA for MSPs!
Thanks to our donors. We appreciate your support!
If you would like to donate to the cause you can do that at HelpMeWithHIPAA.com
Like us and leave a review on our Facebook page: www.Facebook.com/HelpMeWithHIPAA
If you see a couple of numbers on the left side you can click that and go directly to that part of the audio. Get the best of both worlds from the show notes to the audio and back!
Thanks to our donors.
HIPAA Briefs
[01:43] Does HIPAA apply to faxing?HIPAA does not mention faxing specifically, but many healthcare organizations still use faxing services, whether that is in the form of a physical stand alone fax machine or a fax server. Regardless, if you are sending or receiving faxes with PHI, it should be on your risk analysis and reasonable and appropriate controls should be in place to protect faxes that include PHI.
HIPAA Say What!?!
[03:36] Does HIPAA apply to all medical practices?No, it does not. If you don’t take insurance and file claims for services at all, technically, you’re not obligated to meet all the HIPAA requirements. HIPAA does not apply to concierge medical practices, for example, that never file any kind of insurance. However, we strongly recommend that these organizations meet HIPAA requirements as possible, even if HIPAA doesn’t apply. These providers do have some pretty important patient information and patient’s deserve to have it protected.
Another good option for healthcare organizations is to review and follow the HICP guides based on the size of the organization. The HICP standards will apply whether or not HIPAA does. If you are managing privacy and security properly, then you likely are meeting most of the compliance requirements.
405d Tip of the Week
[08:25] SBAR Rhysida Ransomware AttackNew 405(d) Situation, Background, Assessment, Recommendation (SBAR) released Aug 16, 2023. It discusses the ransomware-as-a-service group called Rhysida who attacked a health care system on Aug 3.
The SBAR references a previous HHS Health Sector Cybersecurity Coordination Center (HC3) Sector Alert Rhysida Ransomware Alert. The threat actors gain initial access to victims’ networks in several ways, including targeting public-facing applications with targeted phishing campaigns and then utilize a penetrating testing tool that has been reconfigured to exploit its post-exploitation capabilities.
The R of SBAR says:
Securing Older Technologies Still In Use
[13:27] Earlier this year the HSCC Legacy Technology Cybersecurity Task Group published a guide for everyone that must manage and secure all of those old devices we use in healthcare.Of course there is a HIC name for it:
Health Industry Cybersecurity – Managing Legacy Technology Security (HIC-MaLTS)
They bring up some very important points that we may have touched on before, but never as its own topic. The questions they were trying to answer is simply what do we do about these legacy technologies. Let’s talk about HIC-MaLTS.
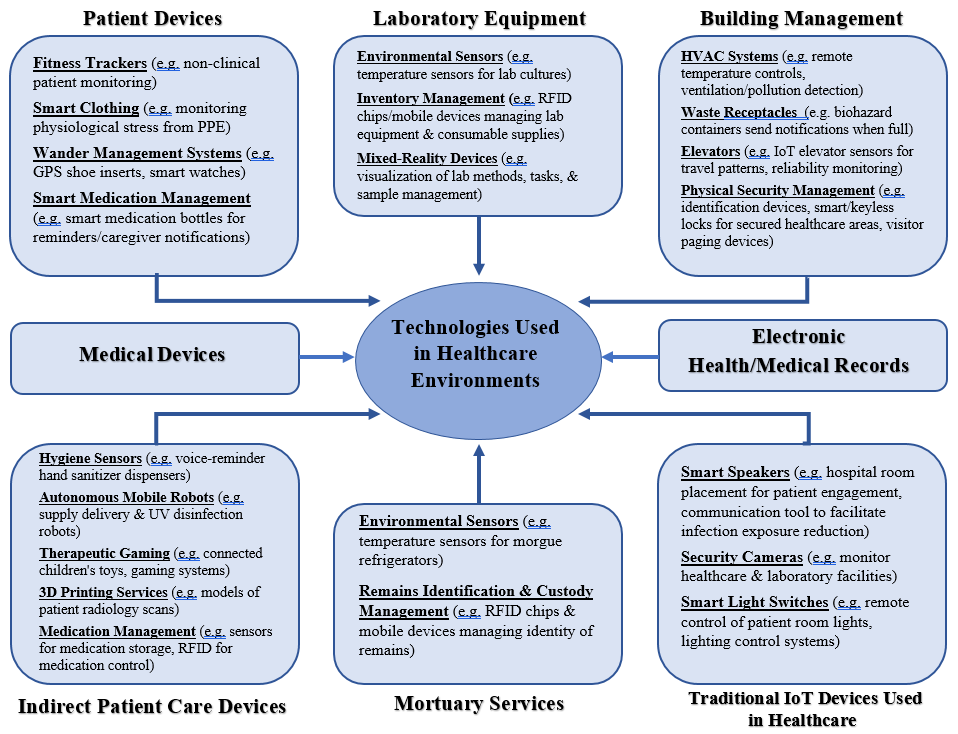
Why say technologies and not devices?
Because there is more to consider than just devices. Here is a great chart that shows the bigger picture we must address:
Why do you care about legacy technology and security?
These technologies often continue to perform essential critical functions on a daily basis in many facilities and organizations. Replacing or updating them is usually a complex and expensive process. The great news is they have stood the test of time for doing their job long term. However, not so much when it comes to requirements we need for security controls today.
Some issues include:
- Many are no longer supported by the original manufacturer or provider. Sometimes those companies don’t even exist anymore and whoever purchased them has no idea how to deal with them.
- We know they are loaded with a terrifying number of potentially exploitable vulnerabilities. Some say hundreds others may have thousands.
- They were created to operate in the olden days where you just assumed all network traffic was acceptable and friendly. There is little chance they could even be updated enough to survive in today’s threat environment.
Very few healthcare organizations today operate without a variety of connected technologies. The important question that every one of them must ask themselves is just how secure are those technologies both today and in the future.
How does HIC-MaLTS help?
[26:37] There are plenty of ways to look at these issues and the guide reviews the issues and then makes separate recommendations for Medical Device Manufacturers (MDMs) and Health Delivery Organizations (HDOs).The HIC-MaLTS guide includes a definition section with commonly known technology terms related to legacy the different stages of a technology’s lifecycle. It also helps those legacy devices and provides industry best practices, recommendations, and references for optimizing security and resiliency and patient safety. It also provides a cross reference to the International Medical Device Regulators Forum’s Principles and Practices for the Cybersecurity of Legacy Medical Devices which provides security best practices that span the product life cycle of medical devices. It is a risk management framework that also points back to HIC-MaLTS.
HIC-MaLTS provides guidance on legacy medical devices that are no longer in use, those that are currently in use (current legacy devices) and those that will one day be considered a legacy device (future legacy devices). Everything we use today will eventually need to be replaced or upgraded and it doesn’t matter what kind of technology it is.
[35:47] So, first we have to identify what are legacy devices, which ones are currently being used and what will become a legacy device later. Group every piece of technology into one of those categories and then you work out how to properly defend a current legacy device and what are you going to do when the other devices become legacy. This is not always an easy task, but you’ll have to figure it out. You have to look at everything to know where your vulnerabilities and risks are so you will know what needs to be secured. This guide provides specific help in this area.The HIC-MaLTS guide provides sections with a list of things to do when managing technologies, whether you are a health delivery organization, technology provider or medical device manufacturer. For instance, to help health delivery organizations, the guide recommends:
- Avoid acquiring legacy technology
- Protect the technologies already in place
- Comply with FDA SBOM (software bill of materials) requirements and take advantage of the SBOM benefits
- Manage non-legacy technologies to keep them non-legacy as long as possible
- Make a smart, risk informed decision about whether to replace a given legacy technology
- Support customers in managing technologies to keep them as non-legacy as possible
- Design, deploy and maintain secure and securable technologies
All of these are in the HIC-MaLTS guide, and you can reference back to the international framework on Principles and Practices for the Cybersecurity of Legacy Medical Devices,, but everything there for your reference or at least to have something to build off of when it has to do with identifying, managing, and planning for legacy technologies.
Neglecting to protect legacy technologies not only jeopardizes the integrity and confidentiality of sensitive data but also poses broader risks to network security. Legacy devices can serve as entry points for cyberattacks, enabling hackers to infiltrate entire systems or networks. Therefore, ensuring the security of these devices through updates, patches, and proper configuration is crucial to safeguarding both individual and organizational digital assets, ultimately preserving trust and privacy in the digital age.
Remember to follow us and share us on your favorite social media site. Rate us on your podcasting apps, we need your help to keep spreading the word. As always, send in your questions and ideas!
HIPAA is not about compliance,
it’s about patient care.TM
Special thanks to our sponsors Security First IT and Kardon.


