 Today we tackle the trifecta of cybersecurity headaches: Microsoft’s awkwardly ambitious recall feature, the looming HISAA regulations (because HIPAA wasn’t enough), and a juicy enforcement action following a ransomware attack. We’ll break down how Microsoft’s recall reboot went from intrusive default to opt-in relief, why HISAA could mean mandatory stress tests for healthcare providers, and what lessons we can learn from a ransomware attack that left 291,000 patient records exposed—and a corrective action plan no one wants. If you’ve ever wondered how healthcare security, government fines, and tech mishaps collide, this one’s for you.
Today we tackle the trifecta of cybersecurity headaches: Microsoft’s awkwardly ambitious recall feature, the looming HISAA regulations (because HIPAA wasn’t enough), and a juicy enforcement action following a ransomware attack. We’ll break down how Microsoft’s recall reboot went from intrusive default to opt-in relief, why HISAA could mean mandatory stress tests for healthcare providers, and what lessons we can learn from a ransomware attack that left 291,000 patient records exposed—and a corrective action plan no one wants. If you’ve ever wondered how healthcare security, government fines, and tech mishaps collide, this one’s for you.
In this episode:
Ransomware, Recall, and Regulations – Ep 480
Today’s Episode is brought to you by:
Kardon
and
HIPAA for MSPs with Security First IT
Subscribe on Apple Podcast. Share us on Social Media. Rate us wherever you find the opportunity.
Great idea! Share Help Me With HIPAA with one person this week!
Learn about offerings from the Kardon Club
and HIPAA for MSPs!
Thanks to our donors. We appreciate your support!
If you would like to donate to the cause you can do that at HelpMeWithHIPAA.com
Like us and leave a review on our Facebook page: www.Facebook.com/HelpMeWithHIPAA
If you see a couple of numbers on the left side you can click that and go directly to that part of the audio. Get the best of both worlds from the show notes to the audio and back!
Thanks to our donors.
HIPAA Say What!?!
[03:51]
Listener question from survey
- What happens when all the vendors that offer the same service (document shredding) refuse to sign a BAA? We have no other options for a vendor?
- Do we just document that we cannot find a vendor that will sign a BAA or …?
- Follow up… what are the general recommendations on checking with BAs on what they are doing to meet their obligations?
Vendors Surprised By Vetting – Ep 451 – Help Me With HIPAA
6 Steps for Vendor Management – Ep 317 – Help Me With HIPAA
Another question about our stuff
[08:51] Would you consider including graphics created from the podcast that I can include in my company compliance newsletter?Advice from our friend George
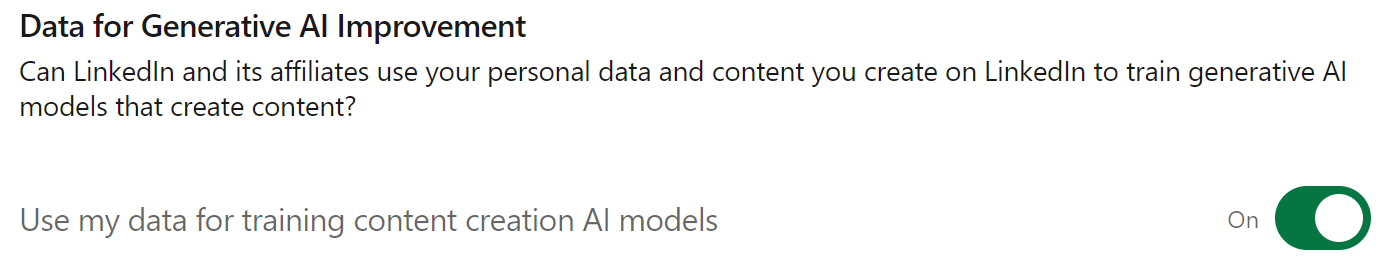
[10:57]Good morning. If you have LinkedIn, check your Settings –> Data Privacy and look for “AI”. Data sharing is on by default in the US.
Ransomware, Recall, and Regulations – Ep 480
[12:50]Geez, ya take a couple of weeks off from recording and get slammed!
The Recall Reboot
Something we have been watching:
Summary of Windows Recall:
Windows Recall is a feature designed to help users retrace their digital activities by capturing and organizing snapshots of their interactions. It allows users to search for past moments using natural language, like searching for a specific product they viewed online. While it offers convenience for users looking to quickly find their past activities, security experts flagged concerns about potential privacy risks since the feature captures everything, even sensitive information.
Key Security Improvements:
Microsoft introduced three major changes to make the Recall feature more secure and address privacy concerns:
- Opt-in Experience:
- No Default Activation: Recall is no longer enabled by default on Copilot+ PCs (such as the Surface Laptop 7 and Surface Pro 11).
- User Prompt: Users will be asked whether they want to opt into Recall before using the feature, giving them full control over its activation.
- Option to Delete Recall:
- Full Uninstall Available: Microsoft now offers users the ability to completely remove the Recall feature from their devices. Previously, there were reports that users would not be able to uninstall it, but this has been addressed.
- Enhanced Data Security:
- Encryption: All data captured by Recall is encrypted using advanced security measures, including the TPM (Trusted Platform Module) chip.
- Windows Hello Integration: Access to Recall data is protected by biometric authentication through Windows Hello (fingerprint, facial recognition), ensuring only authorized users can access it.
- VBS Enclave: Recall data is stored and processed in an isolated secure environment known as a Virtualization-Based Security (VBS) enclave, which separates sensitive data from the main operating system.
Additional Features:
- User Control: Users can customize Recall to limit tracking, excluding specific apps and websites from being recorded. They can also delete snapshots, pause tracking, or turn off Recall at any time.
- No Data Sharing: Microsoft emphasized that it does not share Recall snapshots with third parties or other users on the same device.
This combination of opt-in use, robust encryption, and enhanced user controls are aimed at easing the privacy concerns while still offering the convenience of Recall’s features. That is great but we still don’t think it is a good idea in the world of healthcare and PHI. Maybe after some brave folks have tested it out we can see if it feels safe enough.
Health Infrastructure Security and Accountability Act (HISAA???)
[21:00]New bill introduced: Health Infrastructure Security and Accountability Act One-Pager
Summary of the Bill:
The HISAA was introduced to address the growing threat of cyberattacks on healthcare systems. In 2023 alone, there were 725 data breaches affecting over 120 million Americans, making healthcare the #1 target for ransomware attacks. The bill aims to overhaul the lax cybersecurity practices across healthcare organizations by setting mandatory minimum cybersecurity standards, increasing auditing requirements, and holding executives accountable.
Key Highlights of the Bill:
- Mandatory Cybersecurity Standards: Establishes minimum security requirements for healthcare providers, health plans, clearinghouses, and business associates, with enhanced standards for critical entities.
- Annual Audits and Stress Tests: Requires organizations to undergo annual independent cybersecurity audits and conduct stress tests to ensure they can promptly recover after cyber incidents.
- Executive Accountability: Top executives must certify compliance with cybersecurity requirements, with severe penalties for falsifying this information (similar to Sarbanes-Oxley).
- Funding Support:
- $800 million for rural and urban safety net hospitals for upfront cybersecurity investments.
- $500 million for all hospitals to adopt stronger cybersecurity measures.
- Increased HHS Oversight: The Department of Health and Human Services (HHS) will audit at least 20 high-priority entities annually and have the power to levy larger fines, removing current caps on penalties.
- User Fees: Supports the HHS enforcement efforts through a user fee on regulated entities.
User fees?
The user fee in the Health Infrastructure Security and Accountability Act (HISAA) applies to covered entities (like healthcare providers and health plans) and their business associates (third-party vendors handling protected health information). The fee is calculated based on each entity’s pro rata share of national health expenditures. The total fees collected will support HHS’s oversight and enforcement activities and are capped at $40 million in 2026, $50 million in 2027, with adjustments for inflation in future years.
This means healthcare organizations and their partners will share the costs of improved cybersecurity oversight, with fees based on their size and industry involvement.
The national health expenditures referenced in the Health Infrastructure Security and Accountability Act (HISAA) include the total spending on healthcare services, insurance, and related activities within the U.S. economy. This encompasses all healthcare-related expenses, from hospitals and medical services to health insurance administration.
For small businesses, especially those with minimal annual expenditures, their share of the user fee is proportional to their impact on these expenditures. However, the document does not provide a specific formula for calculating individual fees, nor does it clarify whether small businesses would receive exemptions or reduced rates.
The estimated national health expenditures for the U.S. in 2022 were approximately $4.4 trillion, according to data from the Centers for Medicare & Medicaid Services (CMS). This amount typically includes spending on hospital care, physician services, prescription drugs, and health insurance. Projections for 2023 are expected to follow a similar upward trend, likely surpassing this figure slightly as healthcare costs continue to rise annually.
Cascade Eye & Skin Centers Enforcement Action
[36:52]New Resolution Agreement: Cascade Eye and Skin Centers, P.C. Resolution Agreement and Corrective Action Plan | HHS.gov
Summary of Cascade Eye & Skin Centers Enforcement Action:
In March 2017, Cascade Eye & Skin Centers experienced a ransomware attack impacting the electronic protected health information (ePHI) of 291,000 individuals. The OCR investigation found Cascade failed to conduct an accurate risk analysis and review of system activity. A settlement of $250,000 was reached with a Corrective Action Plan (CAP).
Corrective Action Plan Highlights:
- Duration: 2 years (effective June 17, 2024).
- Key Requirements:
- Conduct a thorough risk analysis.
- Implement a risk management plan.
- Regular audits and system reviews.
- Annual workforce training.
In their announcement OCR included some points, as usual. We always say it is important to note them.
“Cybercriminals continue to target the heath care sector with ransomware attacks. Health care entities that do not thoroughly assess the risks to electronic protected health information and regularly review the activity within their electronic health record system leave themselves vulnerable to attack, and expose their patients to unnecessary risks of harm,” said OCR Director Melanie Fontes Rainer. “Ensuring the confidentiality of electronic protected health information is critical to protect health information privacy and integral to our national security in the health care sector. OCR urges all health care entities to take the essential precautions and stay vigilant to safeguard their systems from cyberattacks.”
OCR will monitor the corrective action plan for two years. These actions include:
- Conduct an accurate and thorough risk analysis to determine the potential risks and vulnerabilities to the confidentiality, integrity, and availability of its ePHI;
- Implement a risk management plan to address and mitigate security risks and vulnerabilities identified in their risk analysis;
- Developing a written process to regularly review records of information system activity, such as audit logs, access reports, and security incident tracking reports;
- Developing policies and procedures for responding to an emergency or other occurrence that damages systems that contain ePHI;
- Developing written procedures to assign a unique name and/or number for identifying and tracking user identity in its systems that contain ePHI; and
- Reviewing and revising, if necessary, written policies and procedures to comply with the HIPAA Privacy and Security Rules.
OCR recommends health care providers, health plans, clearinghouses, and business associates that are covered by HIPAA take the following steps to mitigate or prevent cyber-threats:
- Review all vendor and contractor relationships to ensure business associate agreements are in place as appropriate and address breach/security incident obligations.
- Integrate risk analysis and risk management into business processes; conducted regularly and when new technologies and business operations are planned.
- Ensure audit controls are in place to record and examine information system activity. Implement regular review of information system activity.
- Utilize multi-factor authentication to ensure only authorized users are accessing ePHI.
- Encrypt ePHI to guard against unauthorized access to ePHI.
- Incorporate lessons learned from incidents into the overall security management process.
- Provide training specific to organization and job responsibilities and on a regular basis; reinforce workforce members’ critical role in protecting privacy and security.
Cyberattacks are evolving fast—if we don’t get ahead of them, healthcare security will be like patching a leaky boat while it’s sinking. The hard truth is: risk analysis might be the most critical tool for healthcare security, but it’s still the one no one seems to be doing right. Whether it’s AI stirring up new privacy headaches or Microsoft’s latest Windows features introducing unforeseen risks, it’s clear that evaluating these challenges isn’t optional—it’s essential. With cyberattacks on healthcare systems only becoming more frequent and damaging, the need for thoughtful, proactive strategies has never been more urgent. If the industry doesn’t get ahead of these threats, the consequences could be far more costly than any corrective action plan. As they say, the key to survival isn’t just reacting to the mess—it’s planning so you don’t end up there in the first place.
Remember to follow us and share us on your favorite social media site. Rate us on your podcasting apps, we need your help to keep spreading the word. As always, send in your questions and ideas!
HIPAA is not about compliance,
it’s about patient care.TM
Special thanks to our sponsors Security First IT and Kardon.


