Over the last couple years, we’ve had some high-profile cybersecurity compromises and data breaches. And this trend is not slowing down. Today, we review a recent study of the top cyber threats to healthcare organizations. The results reinforce that PriSec teams require everyone to participate.
In this episode:
PriSec Teams Require Everyone – Ep 354
Today’s Episode is brought to you by:
Kardon
and
HIPAA for MSPs with Security First IT
Subscribe on Apple Podcast. Share us on Social Media. Rate us wherever you find the opportunity.
The Privacy and Security Boot Camp
3.5 day In Person Event
Sep 12, 13, 14 and 15
PriSecBootCamp.com
Great idea! Share Help Me With HIPAA with one person this week!
Learn about offerings from the Kardon Club
and HIPAA for MSPs!
Thanks to our donors. We appreciate your support!
If you would like to donate to the cause you can do that at HelpMeWithHIPAA.com
Like us and leave a review on our Facebook page: www.Facebook.com/HelpMeWithHIPAA
If you see a couple of numbers on the left side you can click that and go directly to that part of the audio. Get the best of both worlds from the show notes to the audio and back!
HIPAA Say What!?!
[05:16] We know the same old statement: We take privacy and security seriously. Most people think that means keeping your information confidential. Yes, HIPAA Privacy and Security requires us to protect the confidentiality of patient records, but it doesn’t stop there.We have to protect the CIA of all of the PHI that we CReMaT.
That is the confidentiality, integrity and availability for all data that we create, receive, maintain, and transmit.
There are so many cases that come up when there is an assumption that all you have to do is worry about the confidentiality part. Think of it this way when it comes to PHI and what you should always worry about:
- What happens if someone who should not have this information gets ahold of it?
- What happens if we can no longer trust that the information in the records is valid and accurate?
- What happens if we can never get access to this information again?
Any actions you may take that cause you to provide a stressful answer to these questions are actions that you should not take.
405(d) Tip of the Week
[11:14] Best Practice #3 – Access Managementhttps://405d.hhs.gov/Documents/Access-Management-Poster-R.pdf
Health care organizations of all sizes need to clearly identify all users and maintain audit trails that monitor each user’s access to data, applications, systems, and endpoints. Just as you may use a name badge to identify yourself in the physical work environment, cybersecurity access management practices can help ensure that users are properly identified in the digital environment, as well.
Treatment Plan:
Small Organizations
- Establish a unique account for each user. Also it is important to train and regularly remind users that they must never share their passwords.
- Limit the use of shared or generic accounts. If shared accounts are required, train and regularly remind users that they must sign out upon completion of activity or whenever they leave the device, even for a moment.
- Implement Multi-Factor Authentication for the cloud-based systems that your organization uses to store or process sensitive data, such as EHRs. MFA mitigates the risk of access by unauthorized users.
Med/Large Organizations
Make sure you have the items for the small group covered plus
- Instill proper Identity Management. Use a “one-person, one-identity, multiple contexts” solution to all access.
- Always ensure the consistent application of attributes, which in turn enables automated authentication and authorization by utilizing automated provisioning and deprovisioning
- Establish Federated Identity Management. Federated identity management enables identity information to be shared between organizations in a trusted manner.
PriSec Teams Require Everyone
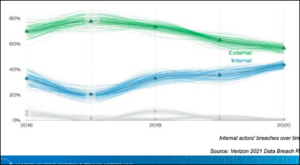
[16:48] Current & Emerging Healthcare Cyber Threat Landscape is a survey done by the Health-ISAC survey that includes a broad spectrum of leaders, cyber and non-cyber, all over the industry and a wide variety of size and types of organizations. This year’s report came out in March.The survey results showed the same top 5 threats concerning everyone for 2022 as they found for 2021.
Top Five Threats for 2021 and 2022:
- Ransomware Deployment
- Phishing/Spear-Phishing Attacks
- Third-Party/Partner Breach
- Data Breach
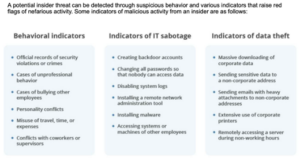
- Insider Threats
Anyone that doesn’t think they have a high risk of a ransomware attack is not paying attention. There is a reason it is on every single list of cyber concerns no matter what list you review. But, the rest of them aren’t taking us down a different road either. Again, it is clear that people are the core issue we must address. I believe a major reason for that is the baked in beliefs about HIPAA are as follows:
- Privacy means confidentiality
- Security is IT’s problem.
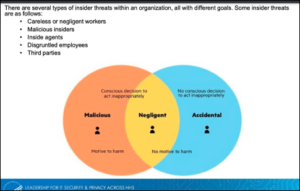
In this report, they look at Ponemon’s 2020 Insider Threats Report that shows “61% of data breaches involving an insider are primarily unintentional, but are caused by negligent insiders.” They state that it is mainly caused by these things:
- Lack of awareness about security policies and a failure to provide security awareness training
- 27% of employees saw security policies less than once a year; 39% received security awareness training less than once a year.
- Unintentional insider threats pose a major risk to the health sector
- Alexa on while sensitive meetings are going on (i.e., working remote) could cause sensitive data to be leaked
Disgruntled employees can be a significant threat because of their access to systems. They are considered emotional threat actors with an intent to cause harm to their company, and in some cases feel as if they are owed something.
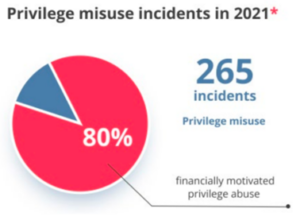
According to CERT, an employee normally becomes disgruntled due to an unmet expectation or an unfortunate event. In Verizon’s 2021 Data Breach Report, 80% of privilege misuse was financially motivated.
[43:10]CISA is promoting their free cybersecurity services and tools that they have available. And there was, in fact, a 405d spotlight webinar on those tools in April. Here is a link to the recording on YouTube.
It takes people, processes and technology to properly secure your networks, protect your critical data and to catch external and insider threats to your business. Bottom line, you’ve got to educate people. You’ve got to have everybody involved or you don’t have a fighting chance.
Remember to follow us and share us on your favorite social media site. Rate us on your podcasting apps, we need your help to keep spreading the word. As always, send in your questions and ideas!
HIPAA is not about compliance,
it’s about patient care.TM
Special thanks to our sponsors Security First IT and Kardon.