 Verizon has released their 2023 Data Breach Investigations Report (DBIR). This year they focused more on an analysis of actual data breaches – the types of incidents causing the breaches, the motivations of bad actors, how they tend to carry out their attacks and what data they are grabbing. We always look forward to reading this report because it not only has a lot of great information, but also because it contains a good bit of humor. You know we like that.
Verizon has released their 2023 Data Breach Investigations Report (DBIR). This year they focused more on an analysis of actual data breaches – the types of incidents causing the breaches, the motivations of bad actors, how they tend to carry out their attacks and what data they are grabbing. We always look forward to reading this report because it not only has a lot of great information, but also because it contains a good bit of humor. You know we like that.
In this episode:
Our takeaways from the 2023 VDBIR- Ep 417
Today’s Episode is brought to you by:
Kardon
and
HIPAA for MSPs with Security First IT
Subscribe on Apple Podcast. Share us on Social Media. Rate us wherever you find the opportunity.
Great idea! Share Help Me With HIPAA with one person this week!
Learn about offerings from the Kardon Club
and HIPAA for MSPs!
Thanks to our donors. We appreciate your support!
If you would like to donate to the cause you can do that at HelpMeWithHIPAA.com
Like us and leave a review on our Facebook page: www.Facebook.com/HelpMeWithHIPAA
If you see a couple of numbers on the left side you can click that and go directly to that part of the audio. Get the best of both worlds from the show notes to the audio and back!
Thanks to our donors.
HIPAA Briefs
[04:11] What is an NPP, who needs them and where should you be able to find it?
The Notice of Privacy Practices (NPP) is a requirement under the HIPAA Privacy Rule for covered entities to disseminate to their patients. Most people think of the NPP as that HIPAA thing you sign at the doctor.
There is an NPRM out there with a proposal to get rid of having to have patients sign that they’ve seen the NPP if the CE makes sure that they have placed it prominently in their public areas like they’re supposed to. When you go to the doctor’s office and should see it easily available in the waiting room and you should be able to get a copy. Also, if the CE has an informational website, it should be posted there and easy to find.
HIPAA Say What!?!
[07:27] So, we’ve come up with a new acronym (that we are going to try to sneak by our internal FCC) that we will use to describe an incident or breach that was a “totally unnecessary royal disaster”… TURD.
So, this goes into the rest of our specific nomenclature with “stay out of my breaches”, “knock me down and steal my teeth”, and now we have “it’s a situation that is a turd”.
Our takeaways from the 2023 VDBIR
[10:16] The 2023 Verizon Data Breach Investigations Report (DBIR) is out. Get your copy at the link below.
We always love to read this report because not only is it packed full of a lot of great information on the status of cybercrime and what we’ve learned in the past year, but it is also well written and quite funny at times. You know we are always down with funny.
2023 Data Breach Investigations Report | Verizon
It is no surprise that social engineering is the most effective and extremely lucrative attack method by cyber criminals. In fact, Business Email Compromise (BEC) has almost doubled across all industries and all sizes of organizations. Social engineering is all about treating an individual like somebody you wanna trick. It goes beyond just phishing. All of social engineering involves the human element.
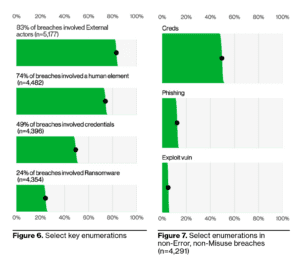
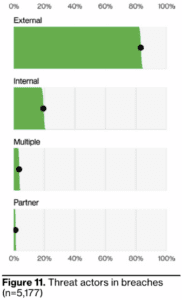
83% of breaches involved External actors, and the primary motivation for attacks continues to be overwhelmingly financially driven, at 95% of breaches. The three primary ways in which attackers access an organization are stolen credentials, phishing and exploitation of vulnerabilities.
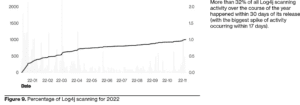
[16:18] Stolen credentials and phishing from social engineering attacks is nothing new. We’ve been talking about that for 10 years or so. The exploitation of vulnerabilities is not new either and we are seeing it a lot more now. Unlike even 5 years ago, smaller organizations can now actually afford to implement true vulnerability management. You’ve gotta to have good patching policies and although some IT companies wait to roll out newly released patches for a week or two so they can test them to make sure they aren’t going to break all of the machines they are deployed on, with the zero day vulnerabilities (like Log4j), patches have to be done much quicker to prevent those vulnerabilities from being exploited.
The actor analysis from the report shows that 83% of breaches were caused by external actors, while internal actors account for 19% of breaches. Not very surprising there, but the fact that “partners” make up an even small percentage of breaches is startling. They’re not talking about your supply chain vendor being hit by a bad actor and the blast filtered to your organization here. They’re talking about a business partner being the initiator of the attack themselves. That’s scary that a partner you have some level of trust with is attacking organizations itself.
Ransomware
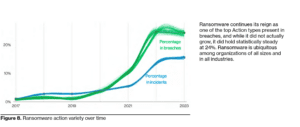
[27:28] Almost a quarter of breaches are caused by ransomware. It’s not going away folks.
You know how we say from time to time “it’s the CIA of the PHI you CReMaTe”? Here’s a quote from the report that reiterates that:
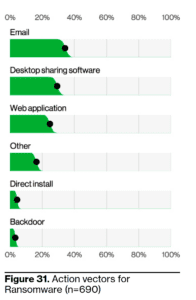
One more thing about ransomware, that again is not surprising, is that email tops the list of the #1 action vector that precipitated ransomware attacks. That’s the action someone took that triggered the ransomware attack. Desktop sharing software and web applications are up there too, but email… it’s the people, people.
Healthcare
[33:45] The headline under the healthcare section says it all:
A sector under siege
For several years, healthcare was the industry that had more attacks and more data breaches from insiders than any other industry. And I think that’s leveled out a little bit and has a lot to do with uptick in monitoring user logins and access, which wasn’t happening for a long time. But, the report did point out:
Where’s my gruntle?
Ah, the disgruntled employee The industry’s only defense for when someone loses their gruntle is fast detection of unusual data access patterns. This remains a challenge for any industry where internal actors are motivated to cause trouble.
See… humor.
You can just monitor for people who are using the front door with a key. You can’t just monitor for login attempt problems. You have to also monitor for things like what people are accessing and what times of day/night they are accessing data, is that typical behavior for that user, etc. You have to monitor for unusual data access and download patterns, too.
If you assume, just because somebody’s worked at your organization for 10 years or more, that they are not going to for some reason no longer be a gruntle. You’re not paying attention. So, please accept that not all employees are gruntle.
SMBs
[40:34] SMBs are no different than any other business.
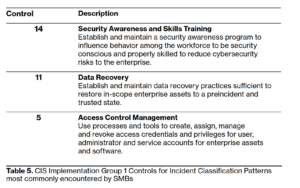
So, they recommend that if you are a SMB with limited resources for implementing security controls, start with the CIS control, control group 1, which consists of security awareness training, data recovery and access control management. The same things we talk about.
Finally, typically you will see that what motivates bad actors is financial gain or espionage purposes. But one of the things we found interesting in the report about actor motives was that 1% of the data breaches occur because People just said it was fun. That’s just disturbing.
Cybersecurity is a collective effort. Everyone is on the cybersecurity team. The responsibility to protect networks and data does not solely fall on IT. We must do our part in recognizing social engineering attacks and training ourselves to remain security conscious to reduce our cybersecurity risk.
Remember to follow us and share us on your favorite social media site. Rate us on your podcasting apps, we need your help to keep spreading the word. As always, send in your questions and ideas!
HIPAA is not about compliance,
it’s about patient care.TM
Special thanks to our sponsors Security First IT and Kardon.