
Buckle up, folks! Today, Donna and David are here with Part 1 of their deep dive into the recent HHS OCR NIST healthcare security virtual conference, and they’re spilling all the cyber-tea. With experts from HHS, OCR, NIST, FTC, and FDA presenting, this conference covered a ton. From AI-powered hackers and QR code scams to unpatched medical devices and a spike in supply chain attacks, the discussions centered on what it takes to keep healthcare data and devices secure in a constantly evolving threat landscape. Wondering why healthcare data security feels like a game of whack-a-mole? Tune in to find out!
In this episode:
OCR NIST Conference Part 1
Today’s Episode is brought to you by:
Kardon
and
HIPAA for MSPs with Security First IT
Subscribe on Apple Podcast. Share us on Social Media. Rate us wherever you find the opportunity.
Great idea! Share Help Me With HIPAA with one person this week!
Learn about offerings from the Kardon Club
and HIPAA for MSPs!
Thanks to our donors. We appreciate your support!
If you would like to donate to the cause you can do that at HelpMeWithHIPAA.com
Like us and leave a review on our Facebook page: www.Facebook.com/HelpMeWithHIPAA
If you see a couple of numbers on the left side you can click that and go directly to that part of the audio. Get the best of both worlds from the show notes to the audio and back!
Thanks to our donors.
HIPAA Briefs
[03:16]On October 22, 2024, Change Healthcare notified the HHS Office for Civil Rights (OCR) that approximately 100 million individual notices have been sent regarding this breach. This massive cybersecurity incident, which occurred in February 2024, is now considered the largest healthcare data breach in U.S. history.
405(d) Tip of the Week
[06:16]This week, 405(d) dropped a new cyber hygiene poster focused on Security Operations and Incident Response!
In the fast-paced world of healthcare, where patient data security is paramount, establishing a robust Security Operations Center (SOC) and effective Incident Response (IR) can be the difference between a minor security event and a catastrophic data breach. SOCs help monitor, prevent, and respond to cybersecurity threats in real time, while incident response plans ensure swift action to limit damages and restore system integrity, ensuring continuous patient care and compliance with regulatory standards.
Use this information and resource to keep patient safety a priority and strengthen your organization’s cybersecurity posture. Be on the lookout for new posters and more information throughout the month of October as we celebrate National Cybersecurity Awareness Month!
And remember, Cyber Safety is Patient Safety!
Security Operation Center and Incident Response
OCR NIST Conference Part 1
[08:41]HHS Cyber SOC Intelligence Branch Chief, Threat Briefing
3 things happening:
- Increased sophistication of attackers
- Rising geopolitical tensions increasing actions by nation states, affiliates of nation states and those who want to gain favor of those nation states
- Evolution of threat actors making things more complex – AI making it a lot easier
Most of the groups are not formal organizations, more where a group gets together like going to a concert with friends they just conduct a number of attacks and then disassemble until the next time.
Majority are from Russia, North Korea, and Chinese groups not bothered by the Chinese government as long as they don’t cause the government trouble.
They want high value, lots of money without having to work hard. Their ill gotten gains go to the government for funding other things in the nation state cases plus they wreak havoc.
AI can hyper charge these threats – a case of Red Bull and a bunch of experts for free to any group that wants to use it. These tools are like free bodies where they can use Shodan to get a list and put it into AI for better details to use in their attacks that are found quickly and for free or cheap.
AI fixes all the bad grammar and other indicators of phishing. Example: Use Canva to make something by describing it and AI builds a coffee shop coupon – for free they have a legit looking attack ready to go.
Not a lot of malware using AI to create it yet but that isn’t the biggest use yet. They code and test, code and test much more quickly with it though.
Supply Chain Attacks
[22:07]Examples reviewed because they were huge but didn’t even talk about Change Healthcare in this list yet.
- Solar Winds
- MOVEIT – they stole so much data they haven’t even been able to parse all of it yet
- Kaseya VSA attack
Third party is the biggest threat because we don’t have effective protections in place downstream. The long chain of vendors makes it impossible to know if 3 steps down there are problems. You will not know if one of those vendors has a breach for weeks, months or maybe ever for some of them.
Securing the human is still the biggest game and supply chain is that problem on a massive scale. They find one key and open a bunch of doors down that chain. They are tracking the vendors and knowing when they are being bought to know when there are purchases of purchased companies that are owned by Russian Oligarchs that open new doors.
Multistage attacks where they slowly draw you into trusting them before giving you the big boom. Newest fad is zero click exploits launched with accessing a website or looking at a text message that lets them into a device to scrape data without the user even knowing it.
Nation states are spending money on quantum computing and AI tools which will allow them to get ahead of us so we have to constantly push for better tools and protections.
Sector specific
- Ransomware – primarily is for the money more than anything
- Legacy systems are a problem in healthcare because it works forever and not patched or not secured
- Medical IoT because of the intersection between professional products and consumer grade which do not have the same level of security in place. Just because it is cheaper they get used in an insecure manner.
- Data breaches impacts will keep happening and only increase in number and scope.
Zero trust is expensive but the benefits outweigh the costs.
FTC Actions
[34:32]In its first case focused on both the privacy and security of genetic information, the FTC said in a complaint that Vitagene deceived consumers about its privacy and security practices. On its website, the company prominently touted its privacy and security, claiming to offer “Rock-solid security” and promised users that it “collects, processes, and stores your personal information in a responsible, transparent and secure environment.” From 2017-2020, the company also said it would only share consumers’ sensitive health and other personal information in limited circumstances such as providing information to a customer’s doctor or with the lab doing genetic testing.
And in 2020, the company changed its privacy policy by retroactively expanding the types of third parties that it may share consumers’ data with to include, for example, supermarket chains and nutrition and supplement manufacturers—without notifying consumers who had previously shared personal data with the company or obtaining their consent to share such sensitive information, according to the complaint.
In addition, Vitagene’s security failures put consumers’ sensitive data at risk, the FTC said. Vitagene stored in publicly accessible “buckets” on Amazon Web Service’s (AWS) cloud storage service nearly 2,400 health reports about consumers and raw genetic data of at least 227 consumers sometimes accompanied by a first name—despite promising users its security practices would exceed industry-standard security practices. Vitagene did not encrypt that data, restrict access to it, log or monitor access to it, or inventory it to help ensure its security, according to the complaint.
Over a two-year period, Vitagene was warned at least three times that the company was storing unencrypted health, genetic, and other personal information in publicly accessible data buckets, according to the complaint. After a security researcher contacted the company in June 2019, the company finally investigated the issue and notified its customers whose data it had exposed publicly.
In the settlement:
- Must ensure any company that purchases all or parts of 1Health’s business agrees by contract to adhere to provisions of the order;
- Must implement a comprehensive information security program addressing the security failures outlined in the complaint.
He stated that they have brought scores of actions against businesses that use HIPAA seals and HIPAA compliance claims.
FDA Medical Devices
- A cyber device definition – Asks only if the device CAN connect to the internet via Ethernet, Bluetooth, WiFi, or connects to a network that does connect to the internet which means you can access it from the internet.
- YOU MUST HAVE A COORDINATED VULN DISCLOSURE PROGRAM FOR YOUR COMPANY IF YOU HAVE ANY PRODUCT THAT CONNECTS TO THE INTERNET.
- Cyber devices must be updateable.
- Cyber security applies to the entire system, not just the end point devices – everything from development, updates, support and deployment.
- SBOM must include open source and commercial software to get FDA approval. Many think only open source matters.
- Software engineering thinks about making things happen, security engineering thinks about making sure things don’t happen.
- Past performance in security does not indicate future performance.
- Do NOT say to the FDA “Who is ever going to do that?”
IoT and AI Panel
[43:12]IoT vs IT
IT is focused on information risks to the data. IoT new risks come into play mobile devices brought in batteries as an issue, IoT adds more risks like overriding thermostats or pacemakers impacts heart rate or baby cameras used maliciously. Now, risks aren’t just data but can be risks to the people themselves. Security in IT doesn’t have to worry about the impacts to the people using them.
IoT devices live within a system of systems that are all connected and they can connect to.
You can’t add MFA to a defibrillator in the ER!
Example of a device that only works when it can connect to the vendor tools so when the vendor goes down the devices stop working no matter what is happening at the sites that use the devices. EKG devices send info to vendor tools that go down. Now they can’t review the EKGs – those things MUST be in your SRA.
Encryption and MFA are the most discussed but software updates are usually much more important and not discussed from the top of the cybersecurity lists.
AI vendors are all in “shoot first, aim later” mode right now. The overriding theme is speed to market which doesn’t include security. They have the attitude that our customers will let us know if regulatory requirements are needed to be addressed on the back end.
You need to account for all the activity in the AI applications and tools to make sure PHI is addressed and secured. Where does it live, move and breathe is still in question.
Transparency in AI will be key to securing it……
Note that HHS AI Task Force. The value of AI is HUGE. We just have to make sure we figure out how to manage the potential downside it brings at the same time.
NIH – Investments in AI are huge. Over $296m this year just in AI projects for research and development. A bunch of programs and comparable to DoD and DHS AI project funding. A BUNCH of things happening.
All the work to get healthcare to digital over the last decade or so allows us to take advantage of the AI revolution that we are going into now. Things like FHIR APIs required for EHR and Payers systems and the TEFCA exchange rolling out to communicate with each other in conjunction with the information blocking rules allow us to take advantage of the things AI has to offer. Regs are 40-50 years old. They were put in place when we never dreamed of the things AI is already capable of doing today.
“We want to ensure that AI is working “for us” not “on us”.”
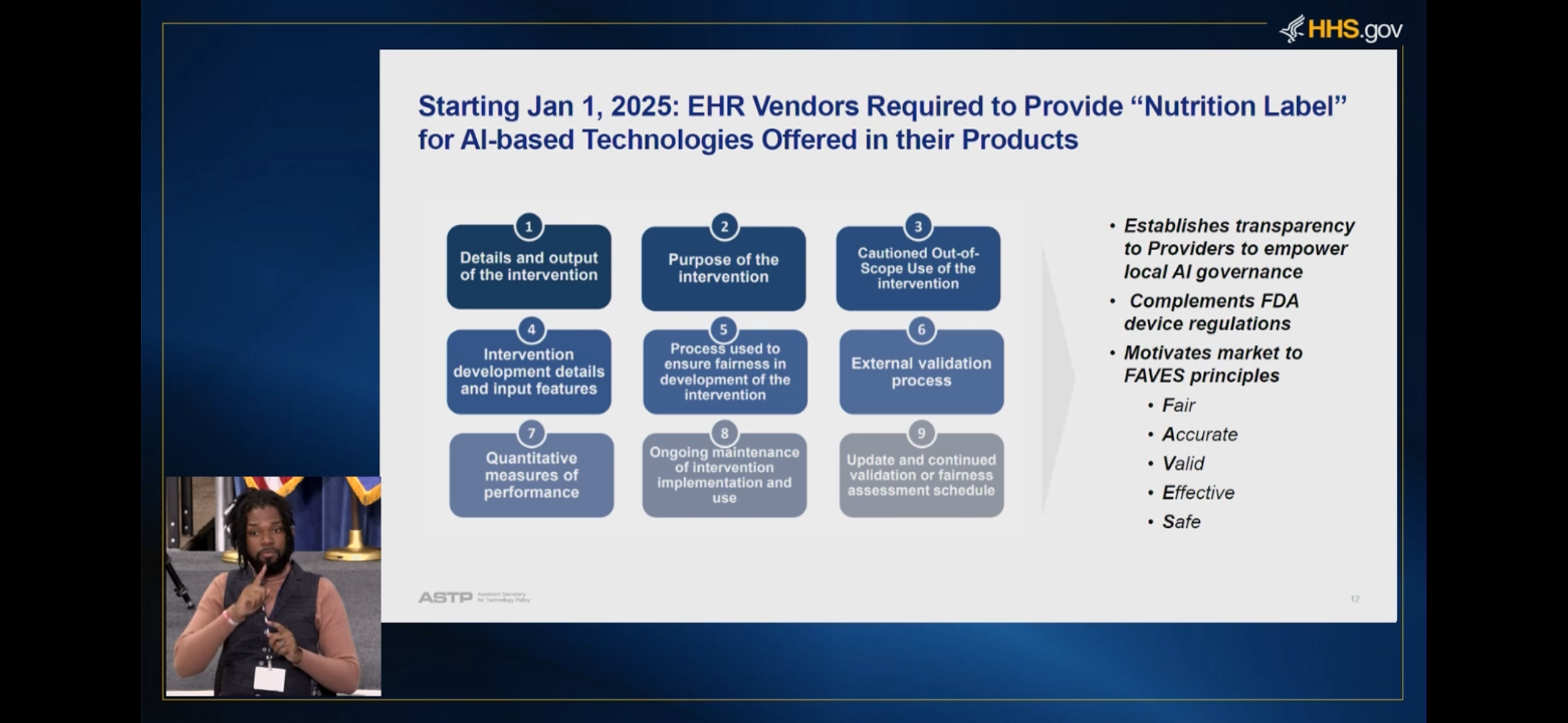
These new requirements apply to all certified health IT. Make sure you watch to see how your EHR vendors address them.
Next time we talk SRAs and HIPAA Security Rule
Protecting healthcare data these days is like watching a magician’s show—there’s always a new trick up someone’s sleeve. The question is: are you catching every sleight of hand? It’s clear that keeping data safe these days means thinking like a spy, fortifying every link in the supply chain, and being prepared for the AI-powered “bad guys.” But while the threats are evolving fast, so are the defenses. Whether it’s the FTC cracking down on shady practices or AI “nutrition labels” (yes, really) coming to your EHR, healthcare security is adapting one step at a time. Until next time—stay sharp, watch those QR codes, and remember, just because someone says their security is “rock solid” doesn’t mean you should skip the fine print!
Remember to follow us and share us on your favorite social media site. Rate us on your podcasting apps, we need your help to keep spreading the word. As always, send in your questions and ideas!
HIPAA is not about compliance,
it’s about patient care.TM
Special thanks to our sponsors Security First IT and Kardon.


