Recently, a Cybersecurity Advisory was released worldwide to MSPs and their customers. We will take a look into what this guidance is, how it applies, and what needs to be done about it. This is BIG and we all better be paying attention.
Recently, a Cybersecurity Advisory was released worldwide to MSPs and their customers. We will take a look into what this guidance is, how it applies, and what needs to be done about it. This is BIG and we all better be paying attention.
In this episode:
MSP Customer Alert – Ep 357
Today’s Episode is brought to you by:
Kardon
and
HIPAA for MSPs with Security First IT
Subscribe on Apple Podcast. Share us on Social Media. Rate us wherever you find the opportunity.
The Privacy and Security Boot Camp
3.5 day In Person Event
Sep 12, 13, 14 and 15
PriSecBootCamp.com
Great idea! Share Help Me With HIPAA with one person this week!
Learn about offerings from the Kardon Club
and HIPAA for MSPs!
Thanks to our donors. We appreciate your support!
If you would like to donate to the cause you can do that at HelpMeWithHIPAA.com
Like us and leave a review on our Facebook page: www.Facebook.com/HelpMeWithHIPAA
If you see a couple of numbers on the left side you can click that and go directly to that part of the audio. Get the best of both worlds from the show notes to the audio and back!
MSP Customer Alert
[01:05] A recent Cybersecurity Advisory (CSA)involving reports regarding an increase of syber attacks on MSPs and their customers. This CSA was created by multiple cybersecurity authorities from around the world.This guidance is specifically tailored for both MSPs and their customers.
It states in this guidance that it is created specifically for MSPs and their customers. And, it goes so far as to say this is not to do with cloud service providers.
We hear MSPs all of the time say that this doesn’t apply to me because we don’t have access to the EHR. But, you have complete control of everything on the network. Confidentiality, integrity and availability all matter.
Whether the customer’s network environment is on premises or externally hosted, threat actors can use a vulnerable MSP as an initial access vector to multiple victim networks, with globally cascading effects.
All of the cybersecurity authorities co-authoring this advisory…
Recommendations for baseline security measures and operational controls
[20:29] Before we get started on the recommendations, let’s take a minute to point out a very important statement in the introduction about implementation.- Prevent initial compromise
- Improve security of vulnerable devices (VPNs and patching)
- Protect internet-facing services.
- Defend against brute force and password spraying.
- Defend against phishing
- Enable/improve monitoring and logging processes
- MSP make sure you facilitate the logs on systems
- Customers get it in your contracts that the MSP will:
- Implement comprehensive security event management that enables appropriate monitoring and logging of provider-managed customer systems;
- Provide visibility—as specified in the contractual arrangement—to customers of logging activities, including provider’s presence, activities, and connections to the customer networks (Note: customers should ensure that MSP accounts are properly monitored and audited.); and
- Notify customer of confirmed or suspected security events and incidents occurring on the provider’s infrastructure and administrative networks, and send these to a security operations center (SOC) for analysis and triage
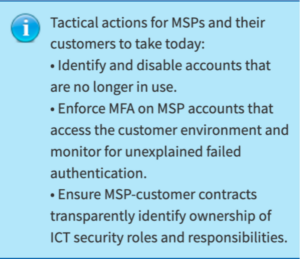
- Enforce multifactor authentication (MFA)
- MSPs should recommend the adoption of MFA across all customer services and products. Note: MSPs should also implement MFA on all accounts that have access to customer environments and should treat those accounts as privileged.
- Customers should ensure that their contractual arrangements mandate the use of MFA on the services and products they receive. Contracts should also require MFA to be enforced on all MSP accounts used to access customer environments.
- [30:27] Manage internal architecture risks and segregate internal networks.
- MSPs should review and verify all connections between internal systems, customer systems, and other networks. Segregate customer data sets (and services, where applicable) from each other—as well as from internal company networks—to limit the impact of a single vector of attack. Do not reuse admin credentials across multiple customers.
- Customers should review and verify all connections between internal systems, MSP systems, and other networks. Ensure management of identity providers and trusts between the different environments. Use a dedicated virtual private network (VPN) or alternative secure access method, to connect to MSP infrastructure and limit all network traffic to and from the MSP to that dedicated secure connection. Verify that the networks used for trust relationships with MSPs are suitably segregated from the rest of their networks. Ensure contractual agreements specify that MSPs will not reuse admin credentials across multiple customers.
- Apply the principle of least privilege.
- MSPs should apply this principle to both internal and customer environments, avoiding default administrative privileges
- Customers should ensure that their MSP applies this principle to both provider and customer network environments. Note: customers with contractual arrangements that provide them with administration of MSP accounts within their environment should ensure that the MSP accounts only have access to the services/resources being managed by the MSP.
- Deprecate obsolete accounts and infrastructure.
- Both MSPs and customers should periodically review their internet attack surface and take steps to limit it, such as disabling user accounts when personnel transition. (Note: although sharing accounts is not recommended, should an organization require this, passwords to shared accounts should be reset when personnel transition.)
- Organizations should also audit their network infrastructure—paying particular attention to those on the MSP-customer boundary—to identify and disable unused systems and services. Port scanning tools and automated system inventories can assist organizations in confirming the roles and responsibilities of systems.
- Customers should be sure to disable MSP accounts that are no longer managing infrastructure. Note: disabling MSP accounts can be overlooked when a contract terminates
- [38:04] Apply updates.
- MSPs should implement updates on internal networks as quickly as possible.
- Customers should ensure that they understand their MSP’s policy on software updates and request that comprehensive and timely updates are delivered as an ongoing service.
- Backup systems and data.
- MSPs should regularly backup internal data as well as customer data (where contractually appropriate) and maintain offline backups encrypted with separate, offline encryption keys. Providers should encourage customers to create secure, offsite backups and exercise recovery capabilities.
- Customers should ensure that their contractual arrangements include backup services that meet their resilience and disaster recovery requirements. Specifically, customers should require their MSP to implement a backup solution that automatically and continuously backs up critical data and system configurations and store backups in an easily retrievable location, e.g., a cloud-based solution or a location that is air-gapped from the organizational network.
- Develop and exercise incident response and recovery plans.
- MSPs should develop and regularly exercise internal incident response and recovery plans and encourage customers to do the same.
- Customers should ensure that their contractual arrangements include incident response and recovery plans that meet their resilience and disaster recovery requirements. Customers should ensure these plans are tested at regular intervals.
- [45:56] Understand and proactively manage supply chain risk.
- All organizations should proactively manage ICT supply chain risk across security, legal, and procurement groups, using risk assessments to identify and prioritize the allocation of resources
- MSPs should understand their own supply chain risk and manage the cascading risks it poses to customers.
- Customers should understand the supply chain risk associated with their MSP, including risk associated with third-party vendors or subcontractors.
- Customers should also set clear network security expectations with their MSPs and understand the access their MSP has to their network and the data it houses.
- Each customer should ensure their contractual arrangements meet their specific security requirements and that their contract specifies whether the MSP or the customer owns specific responsibilities, such as hardening, detection, and incident response.
- Promote transparency.
- MSPs, when negotiating the terms of a contract with their customer, should provide clear explanations of the services the customer is purchasing, services the customer is not purchasing, and all contingencies for incident response and recovery.
- Customers should ensure that they have a thorough understanding of the security services their MSP is providing via the contractual arrangement and address any security requirements that fall outside the scope of the contract. Note: contracts should detail how and when MSPs notify the customer of an incident affecting the customer’s environment.
- Manage account authentication and authorization.
- MSPs should verify that the customer restricts MSP account access to systems managed by the MSP.
- Customers should ensure MSP accounts are not assigned to internal administrator groups; instead, restrict MSP accounts to systems managed by the MSP. Grant access and administrative permissions on a need-to-know basis, using the principle of least privilege. Verify, via audits, that MSP accounts are being used for appropriate purposes and activities, and that these accounts are disabled when not actively being used.
Additional resources included for reference. Below are a few examples:
Cyber Security Considerations For Consumers of Managed Services (ITSM.50.030) from Canadian Centre for Cyber Security
Shields Up Technical Guidance | CISA
It’s not enough for businesses to assume their MSP has them covered when it comes to protecting their networks for cyber attacks. It’s clear from this worldwide advisory that cyber attacks are increasing and more needs to be done to confirm MSPs are not only doing more to protect their business but also those of their customers.
Remember to follow us and share us on your favorite social media site. Rate us on your podcasting apps, we need your help to keep spreading the word. As always, send in your questions and ideas!
HIPAA is not about compliance,
it’s about patient care.TM
Special thanks to our sponsors Security First IT and Kardon.