Imagine your hospital gets hacked—the MRIs are down, billing’s frozen, and suddenly you’re faxing patient records like it’s 1999. No, that’s not a “Twilight Zone” rerun—it’s real life in health care. This week, we’re diving into what the Health Sector Coordinating Council (HSCC) is doing about it, including their recent trip to Congress to lay it all out. From legacy devices clinging to life like old Tamagotchis to cybersecurity plans that don’t sound half bad, we break it all down with just the right amount of snark.
In this episode:
HSCC Makes Bold Cyber Rx Move Before Congress – Ep 505
Today’s Episode is brought to you by:
Kardon
and
HIPAA for MSPs with Security First IT
Subscribe on Apple Podcast. Share us on Social Media. Rate us wherever you find the opportunity.
Great idea! Share Help Me With HIPAA with one person this week!
Learn about offerings from the Kardon Club
and HIPAA for MSPs!
Thanks to our donors. We appreciate your support!
If you would like to donate to the cause you can do that at HelpMeWithHIPAA.com
Like us and leave a review on our Facebook page: www.Facebook.com/HelpMeWithHIPAA
When you see a couple of numbers on the left side of the text below click that and go directly to that part of the audio. Get the best of both worlds from the show notes to the audio and back!
HSCC Makes Bold Cyber Rx Move Before Congress
[04:41] We need to start by pointing out that the things we are discussing today did happen on April 1st but we don’t think it was a fool’s errand. Several members of the HSCC actually did go through presenting testimony in front of a Congressional committee. They laid out what we know to be the truth: our medical technology is aging, our systems are under attack, and we’re running out of time.More importantly, though, it gave them an opportunity to make a bold statement about what HSCC proposes for moving forward with the Security Rule. That proposal wasn’t just a press release, they got a chance to propose it in conjunction with this testimony and that is where you have to get the attention of the most people first.
Subcommittee on O&I Holds Hearing on Cybersecurity Vulnerabilities in Legacy Medical Devices
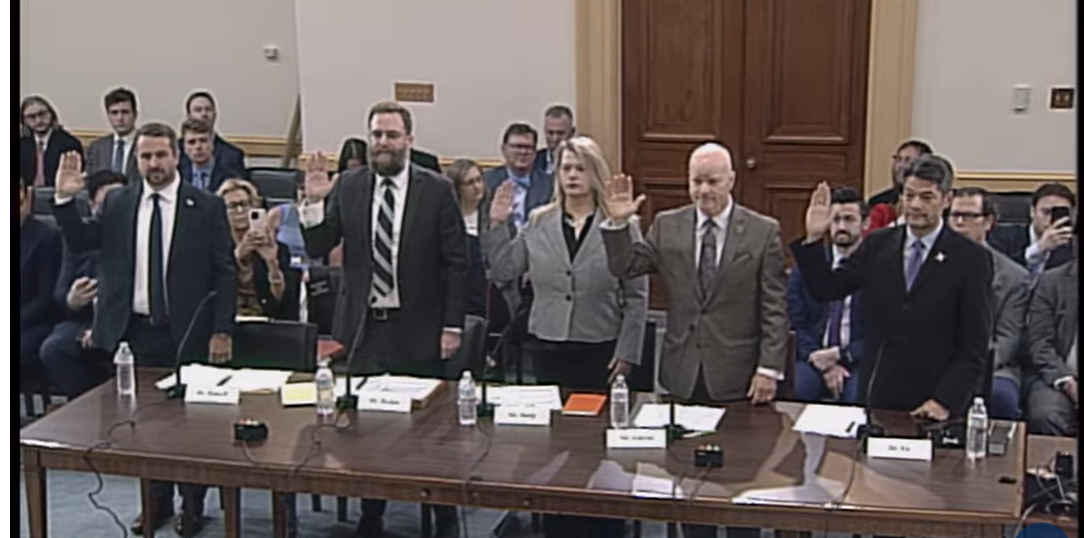
The panel included:
Greg Garcia, Executive Director, HSCC Cybersecurity Working Group
Erik Decker, CISO, Intermountain Health
Dr. Christian Dameff, Medical Director of Cybersecurity, UC San Diego Health, who hosted us in Nov HSCC meeting plus is the star of our cybersecurity for the clinician videos.
The other two are superstars in the medical device cybersecurity world.
Dr. Kevin Fu, Professor of Electrical & Computer Engineering, Northeastern University. He was the inaugural Acting Director of Medical Device Cybersecurity in the U.S. FDA’s Center for Devices and Radiological Health (CDRH)
Michelle Jump, Chief Executive Officer (CEO) at MedSec a medical device cybersecurity company (now that is a niche)
The Problem is Massive, and It’s Not Getting Better
They all offered different perspectives of the same problem and stressed how little we know about how bad it really is for us. Erik was specifically asked by one of the committee members:
Are there updated estimates on how many legacy medical devices are currently in-use across the U.S. health care system?”
Erik’s response: “The problem is actually sort of unknown, as far as how many devices exist, especially when we start talking about the concept of what is legacy versus what is non-legacy devices… We can estimate how many devices we think exist. So, if you look inside any typical hospital, you have for any bed 8-15 some devices connected to it. There are stats that show there’s about 913,000 beds in the United States, so extrapolating that, you get to about easily 10,000,000 devices that exist.”.
The really good one was an exchange with one congressman and Greg Garcia:
Congressman:
“Mr. Garcia, during your verbal testimony, you made a statement that surprised me a little bit and it was that the medical device security in the medical industry, if I understood you correctly, was the most targeted for cyberattacks. Did I get that right?”
Mr. Garcia: “The entire health care ecosystem, not just medical devices.”
Congressman: “Okay, so why health care? I mean, we hear about the banking, right? And power grids. What is it about the health care industry that creates that target?”
Mr. Garcia: “Yeah, I came from financial services before this and, at that time 15 years ago, banking was the biggest target because that’s where the money is. But then they started outspending the criminals. The problem with health care is, first off, it is a widely distributed, multifaceted ecosystem that has a lot of touch points, a lot of vulnerabilities. Secondly, there is less money to spend against cyber threats. And thirdly, it’s easy money. When you have a ransomware attack, if you are a hacker and you ransom a hospital, you are forcing the decision on the hospital: should I pay the ransom and continue to treat patients or should I not and run the risk of not treating patients and/or going out of business. That’s why.”
There were also questions that let Greg point out we have a report coming out any day now that explains how rural health and “Resource-Constrained health providers” are struggling and some recommendations for helping them survive and protect patient safety. We will review that for sure once it is released.
It was also perfect to submit the statement on policy that we are really happy to see come out.
The Bold Cyber Rx Proposal
[16:40]HSCC Cybersecurity Policy Statement
HIC – Recommendations for Government Policy and Programs (HIC RGPP?)
In his testimony Greg Garcia had some good quotes but one of the best was: Fixing a flat tire won’t do you much good if the steering column is loose and the oil warning light is broken.
He got the proposal into the record with this statement:
First, we submitted to the Administration yesterday a policy statement, which I would ask be entered
into the record. In it we recommend initiation of a consultative process between the health sector and
the government that starts with the best practices we have developed – by the sector for the sector and jointly with HHS. This process would supplant one-way government regulation that presumes the best way to do things, with a more deliberative pathway toward eventual requirements for minimum
cybersecurity accountability.
Let’s see what that proposal includes. One note is they leaned into the themes and buzz words of the day like Make American Healthy Again and several others. Really smart. Well and easy since we were already going with our “Cyber safety is patient safety” and 5 year plan going “from critical to stable”. Just fit right in there with no additional tweaks really. From the opening of the proposal:
Thus, ensuring that an individual health provider, IT, payer, pharmaceutical or medical technology capability is “cybersecure” alone is no longer sufficient; modern care delivery and its supporting infrastructure require that all disparate pieces of the evolving healthcare ecosystem be considered and appropriately secured.
This imperative can be addressed through negotiated cybersecurity regulation, policy, and voluntary practices implemented across the healthcare ecosystem. It is clear that, given the increasing number and techniques of cyber incidents inflicted on the health system, neither voluntary practices nor government policy have been sufficient to reduce cyber risk and incidents across the sector.
There are 5 areas the proposal breaks down and provides recommendations. It all starts with us working together to build a new Security Rule.
[22:03]- Preparedness and Information Sharing – The following Preparedness and Information Sharing recommendations operationalize the HSCC cyber wellness themes of Access, Community and Innovation, and address numerous Health Industry Cybersecurity Strategic Plan Objectives.
1.1 HHS should join with the HSCC and healthcare stakeholders in a national communications and outreach campaign to the health provider community and its supporting infrastructure about the imperative of cyber security as a patient safety issue. This begins with a federated communications strategy featuring the many healthcare-specific cybersecurity practices offered by industry and government that help users to:
1) monitor threats;
2) manage risks;
3) secure medtech;
4) respond and recover; and
5) measure effectiveness.
1.2 Joint security guidance published by HHS and HSCC tend to have more credibility, reach and adoption than publications released independently by either. Procedures for developing joint publications should be formalized and structured similar to how the HHS 405(d) program and HSCC produced the flagship cybersecurity guide “Health Industry Cybersecurity Practices (HICP)– Managing Threats and Protecting Patients” and the “Hospital Resiliency Cyber Landscape Analysis”.
1.4 Remove potential regulatory or legal barriers (eg., antitrust, Stark law, etc) to the formation of a health provider consortium that would develop and promote uniform minimum cybersecurity program requirements for any entity that sells hardware, software or services to a health system. This could be modeled on, for example, a FEDRAMP-type govt conduit to 3rd party cyber risk management requirements using a version of the HSCC Model Contract – https://healthsectorcouncil.org/model-contract-languagefor-medtech-cybersecurity-mc2.
1.5 Generally 50% of healthcare breaches and ransomware attacks on healthcare are due to breaches against third party technology and service providers; we should accordingly explore national-security based regulatory mechanisms to hold technology, software and service providers supporting critical health infrastructure to higher levels of accountability for enhanced product and enterprise cybersecurity requirements, similar to FDA pre-market and post-market cybersecurity requirements on medical device manufacturers subject to safety and quality standards, using a cleared entities list approach similar to FEDRAMP.
1.8 Cyber insurance carriers have varying and inconsistent cybersecurity control requirements for determining premiums and coverage of insured healthcare entities. For cyber risk reduction and risk transfer efficiencies to scale across the sector, consistency in expectations is needed for assessing providers’ investments in risk management programs. Accordingly, HHS and CISA should coordinate with major cyber insurance carriers and their state regulatory agencies to encourage the reference of HICP into cyber insurance policy requirements, similar to the incentive signed into law as P.L. 116-321 on January 5, 2021. This law recognized breached entities’ implementation of HICP, the NIST Cybersecurity Framework and other recognized security practices as mitigating factors that HHS must consider when pursuing a HIPAA data breach enforcement action. Reference practices could also include participation in the Health-ISAC or other information sharing and analysis organizations (ISAO’s) as an element of good cybersecurity practice that would improve premiums and coverage.
1.9 Protect health delivery organizations from class action lawsuits if they can demonstrate that they implement NIST CSF, HICP, or other recognized cybersecurity practices. This could incentivize more robust adoption and implementation of security controls.
1.10 Continue development, outreach and provision of innovative CISA support programs, such as the Cyber Hygiene (CyHy) program and cyber exercises, that can be tailored in close consultation with HHS to healthcare entities.
[33:59]2. Financial Support and Incentives – The following Financial Support and Incentives recommendations operationalize the HSCC cyber wellness themes of Access and Community, and address numerous Health Industry Cybersecurity Strategic Plan Objectives
2.1 CMS reimbursement incentives
2.2 Unregulated third-party technology and service providers represent both a major threat vector and costly third-party risk management demands. Health providers should not bear sole burden for policing their vendors; such third parties must be held to an enforceable higher cybersecurity standard when they support critical healthcare infrastructure where lives are at risk.
2.3 Workforce augmentation for needed cybersecurity skills should be funded at the federal level.
2.4 Maintain and expand of the U.S. Department of Agriculture’s Rural Loan Program
2.5 As one-time grant support payments generally cannot be used for hiring, grant programs should be tailored to the specific needs of the Resource-Constrained health providers and should be ongoing as part of the payment structure.
2.6 CISA and HHS should encourage state insurance regulatory agencies to work with insurance companies to devise incentive programs that tie reduced premiums and/or improved coverage for cyber insurance to participation in the Health-ISAC and other information sharing and analysis organizations as one element of an appropriate cybersecurity risk management program.
2.7 HHS should explore mechanisms to fund or incentivize qualified managed security service providers (MSSPs) to assist critical access, safety net and rural emergency hospitals to remediate urgent vulnerabilities or mitigate threats.
2.10 HHS should compile a reference of federal subsidies and grants across the government that fund
cybersecurity services, tools, and education for health providers.
[43:38]3. Incident Response and Recovery – The following Incident Response and Recovery recommendations operationalize the HSCC cyber wellness themes of Community and Innovation, and address numerous Health Industry Cybersecurity Strategic Plan Objectives
3.3 Because health systems are burdened with multiple differing report forms and overlapping agency requirements for the same incident, incident reporting timeframes and methodologies should be standardized across government regulatory entities.
3.4 Cyber-attack victim reporting requirements should be waived while an incident response is underway in the early stages of discovery and operational triage.
3.5 Provide federal-sponsored incident response support for organizations that are experiencing security incidents and in need of assistance getting through and recovering from the breach.
3.8 Provide Military, State, or National Guard cyber/medical personnel, equipment and services support for providers meeting specific need thresholds after an attack (incident response and recovery), with appropriate reimbursement from HHS/CISA
[48:46]4. Workforce – The following Workforce recommendations operationalize the HSCC cyber wellness themes of Access and Workforce, and address numerous Health Industry Cybersecurity Strategic Plan Objectives. A number of recommendations supplement those made in the forthcoming HSCC Report and Recommendations on Cybersecurity for U.S. Resource-Constrained Health Providers.
4.1 HHS should administer a healthcare cybersecurity workforce development and cyber training program with assistance from NIST, CISA, and/or Veterans Administration. A program could include access to free cyber training, assistance to providers under an expanded Regional Extension Centers program, and student loan forgiveness programs modeled after physician loan forgiveness programs, or the National Science Foundation’s CyberCorps® Scholarship for Service (SFS) program. This program provides a full scholarship plus stipend for undergraduate and master’s degrees in cybersecurity and requires two years of government service.
4.2 Fund federal, and supplement state-subsidized – “civilian cyber health corps” programs. This could take the form of loan forgiveness; i.e., a Federal program pays / helps pay for a cyber education in exchange for a minimum number of years served, modeled after a uniformed health corps such as the U.S. Public Health Service Commissioned Corps – https://www.hhs.gov/surgeongeneral/corps/index.html. Also suggest establishing career pathways that do not require a full 4 years of college (i.e. certificate programs and associates).
[50:12]5. Regulatory Reform
5.1 As the primary cross-sector healthcare advisory council focused exclusively on critical infrastructure cybersecurity, the HSCC is prepared to engage with government leadership in a phased series of policy consultations and workshops to negotiate a modernized, coherent, practical, scalable and effective framework that combines both mandatory and flexible voluntary practices for healthcare technology, enterprise and health provider cybersecurity. A successful model for this type of public-private engagement is the development of the NIST Cybersecurity Framework initially published in 2014 after 1 year of work, a process convened and guided by NIST with content generated by the industry owners and operators of critical infrastructure – those most knowledgeable and responsible for securing it.
5.2 The December 2024 HHS notice of proposed rulemaking updating the HIPAA Security Rule did not demonstrate sufficient insight to the complexities of achieving effective cybersecurity protections for the health sector, nor acknowledge the considerable work the sector and government partners have accomplished in good faith and urgency over the past 6 years to build a collective cyber defense. The HIPAA Security Rule update process should be reset with the collaborative process described above.
5.5 Harmonize current sector specific regulations to possible future regulations on Consumer Data Privacy and Security as well as Artificial Intelligence to further create a holistic, coherent strategy with clear aligned requirements and regulatory authority.
Wrapping this up like a freshly printed discharge summary—there’s no denying the health care sector has a lot of cyber cobwebs to clean out. But at least we’ve got folks like the HSCC pushing to turn things around, even if it means dragging Congress into a conversation about hacking pacemakers and DOS-based servers. Will their plan actually make us safer? Only time—and probably a few more ransomware incidents—will tell.
Remember to follow us and share us on your favorite social media site. Rate us on your podcasting apps, we need your help to keep spreading the word. As always, send in your questions and ideas!
HIPAA is not about compliance,
it’s about patient care.TM
Special thanks to our sponsors Security First IT and Kardon.



