Ever leave a conference with a notebook full of “wait…we should probably be doing that” moments? That’s exactly the energy here. In this episode, we unpack key takeaways fresh from the HIPAA Summit – what stood out, what raised eyebrows, and what might quietly keep compliance folks up at night. Then we pivot into a timely breakdown of the latest OCR webinar on Risk Management Plans, connecting the dots between what’s being said on stage and what’s expected in practice. Think of it as part field report, part reality check.
In this episode:
HIPAA Summit 2026 – What OCR Had To Say – Ep 557
Today’s Episode is brought to you by:
Kardon
and
HIPAA for MSPs with Security First IT
Subscribe on Apple Podcast. Share us on Social Media. Rate us wherever you find the opportunity.
Great idea! Share Help Me With HIPAA with one person this week!
Learn about offerings from the Kardon Club
and HIPAA for MSPs!
Thanks to our donors. We appreciate your support!
If you would like to donate to the cause you can do that at HelpMeWithHIPAA.com
Like us and leave a review on our Facebook page: www.Facebook.com/HelpMeWithHIPAA
When you see a couple of numbers on the left side of the text below click that and go directly to that part of the audio. Get the best of both worlds from the show notes to the audio and back!
HIPAA Summit 2026 – What OCR Had To Say
[00:42]HIPAA Summit Sessions on lots of AI which we will cover another time – this one is about OCR and the info they put out for us to read between the lines.
First up – Paula M. Stannard, new director on her 3rd job within HHS plus been on the other side working directly in a CE plus other work consulting with clients. She said that work gave her a whole new perspective and understanding about why leadership should be looking @ HIPAA not just assuming things.
“OCR’s HIPAA Portfolio Vision
- Be Agile and Strategic
- Execute High-Impact Enforcement for Maximum Impact
- Build Resilience through Compliance”
Note: The thoughts on dates and status are just my opinions – she couldn’t say anything that they had not finalized.
Discussed Part 2 and the Parent Access to Minor Child records info. Not focusing on this section.
NPRM – Privacy
- Over 1,400 comments back in 2021
- Big deal about getting rid of the npp signature requirements and keeping up with them.
- Mentioned importance of the coordination of care areas
- Noted Spring agenda item.
Right of access enforcement initiative
- OCR receives many complaints alleging denial or no access records.
- 54 completed enforcement actions.
- A new focus on parent/personal representative access.
HIPAA Audits
- Audits initiated in December 2024.
- Reviewing compliance with selected provisions of the HIPAA Security Rule most relevant to hacking and ransomware attacks.
- OCR will publish an industry report summarizing OCR’s findings after the Audits are completed.
2025 breach reports stats showed 76% hacking/IT incidents specific high areas are network servers and email.
[19:43]NPRM – Security
- Over 4,700 comments
- Can’t comment on plans
- Costs and burdens of regulations complaints received but she pointed out costs of doing nothing
- Addressable sound like it is toast.
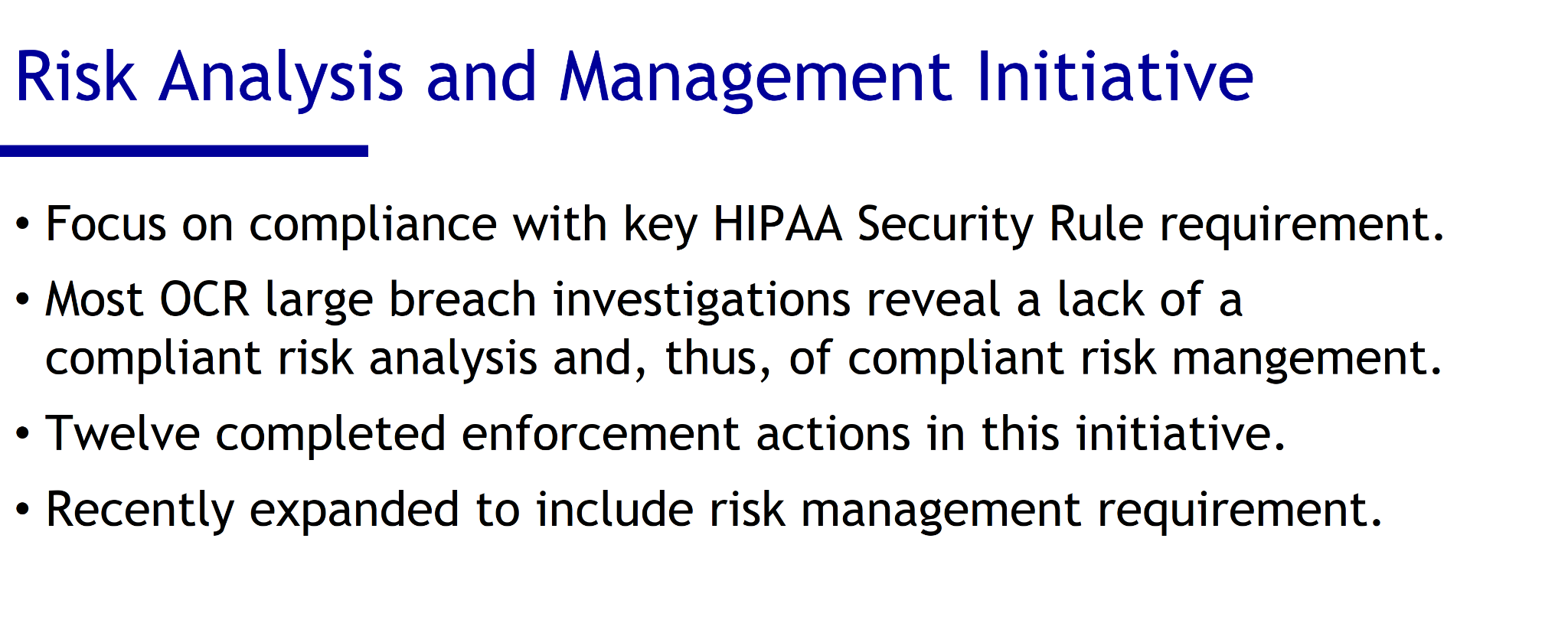
Adding risk management to SRA enforcement initiatives and announced a new video on risk management coming out.
Don’t forget about AI in anything you do – and boy is that a whole other episode!
Nick did a cybersecurity update in his presentation.
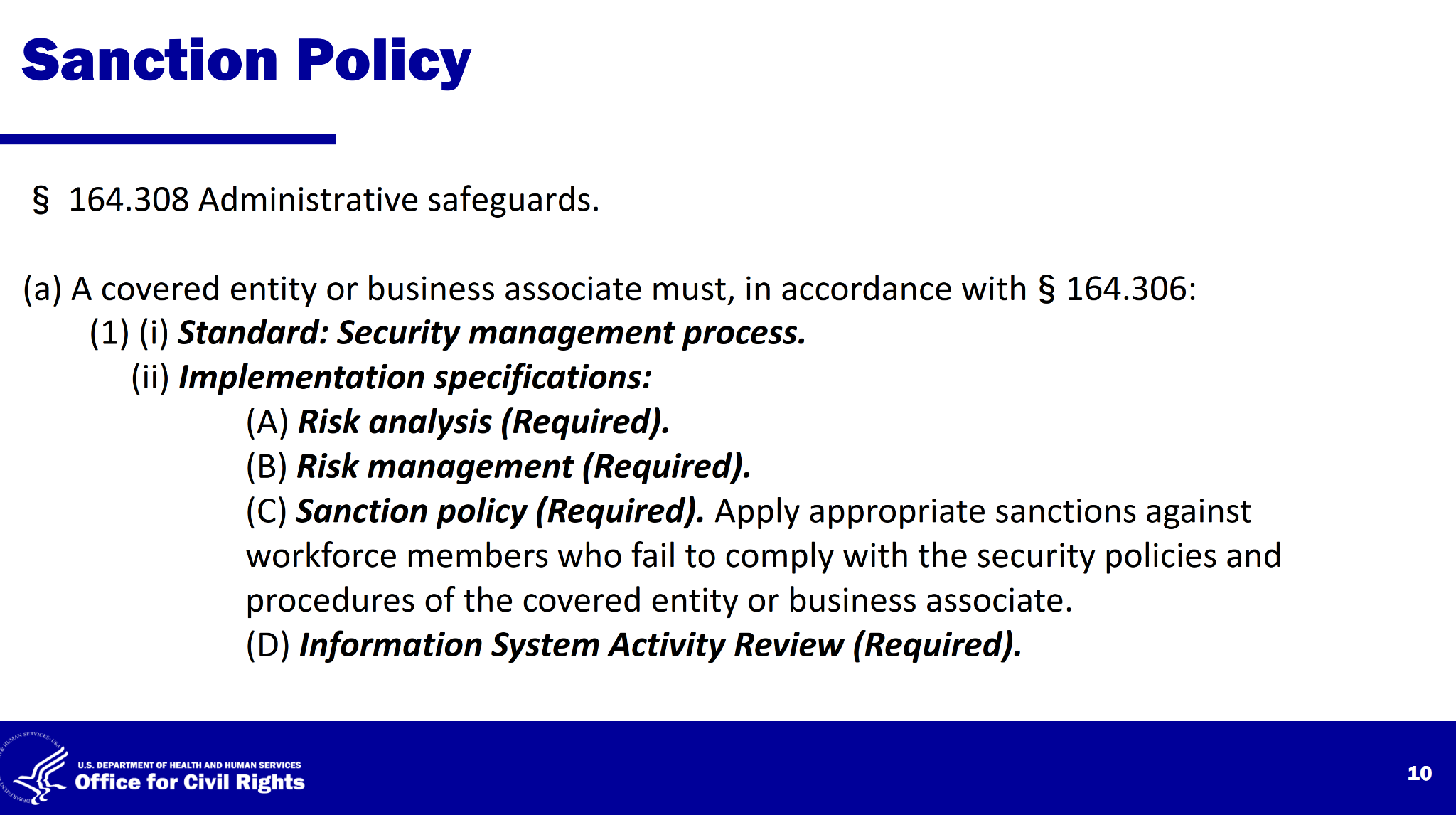
Points out most problems solved with a focus on Administrative Safeguards including the Sanction Policy and System Reviews with the SRA and RM.
OCR didn’t raise the standard… they clarified what the standard always was, which is what we have been saying all along.
The real shift:
- From documentation → implementation
- From awareness → action
- From one-time analysis → continuous management
The new RM Video is out
The RM video came out the same day. Much like the SRA one we need to hit the points but you should take the time to watch it yourself looking for nuggets.
OCR continues to encounter incomplete or nonexistent risk analyses during its HIPAA security rule investigations. It is unsurprising that OCR’s investigations frequently find that regulated entities with poor risk analysis often have noncompliant risk management processes as well because the entities do not understand the risks and vulnerabilities to their ePHI.
Patterns from investigations:
Pattern 1: Known risks ignored for years
- Same vulnerabilities identified repeatedly
- No remediation
Pattern 2: Security theater
- Policies exist
- No real implementation
Pattern 3: Fixing everything… after the breach
- MFA
- Logging
- segmentation
- etc.
Nick pointed out that a risk management plan is NOT just a plan. It has to be implemented with evidence. Such as:
- configurations
- screenshots
- logs
- timelines
- approvals
What pushes you into “willful neglect”
- You knew the risk
- You didn’t fix it
- You had time
Key Points:
Risk management is required under HIPAA and must follow a thorough risk analysis. In other words, Step 1 is the Risk Analysis; Step 2 is the Risk Management (plan and implementation).
Organizations must protect the confidentiality, integrity, and availability of ePHI.
Security measures must address:
- Anticipated cyber threats
- Impermissible disclosures
- Workforce compliance
- Ongoing review and updates of controls
OCR investigations often find:
- Risks identified but never mitigated
- Repeated breaches exploiting known weaknesses
- Weak authentication, especially single-factor access
- Policies written but not actually implemented
Common improvements organizations only implement after breaches (be smart and do these before a breach):
- Multi-factor authentication
- Network segmentation
- EDR/anti-malware
- Reduced admin privileges
- Improved logging and monitoring
Failure to address known risks can be considered willful neglect, with penalties up to about $73,011 per day per violation.
Documentation must PROVE actual implementation, not just policies.
Organizations can use internal teams or third parties for assessments.
Frameworks like NIST are acceptable if they demonstrate real control implementation.
Risk management must be CONTINUOUS, not a one-time activity.
Bottom line:
HIPAA expects regulated entities to identify risks, implement controls, document actions, and continuously maintain security. Failure to actively reduce known risks is a major enforcement focus and a common cause of breaches.
At the end of the day, the themes from the HIPAA Summit and the OCR’s guidance all point in the same direction: awareness is only step one. It’s not enough to know where your risks live – you actually have to do something about them. Because as blunt (and accurate) as it sounds, risk analysis without risk management is just writing down your problems in a very official way. The real challenge, and opportunity, is turning insight into action before someone else points out the gaps for you.
Remember to follow us and share us on your favorite social media site. Rate us on your podcasting apps, we need your help to keep spreading the word. As always, send in your questions and ideas!
HIPAA is not about compliance,
it’s about patient care.TM
Special thanks to our sponsors Security First IT and Kardon.


