 Welcome to the latest Help Me With HIPAA episode where healthcare becomes the star of a suspense thriller, except the villains are hackers, and the plot twist? They really don’t care how small your practice is. We’re diving into Huntress’ 2025 Cyber Threat Report, which basically confirms that if you’re in healthcare, you’ve got a giant “Hack Me” sign taped to your digital forehead. From script-based exploits to info stealers with boundary issues, this episode breaks down how cyber threats are no longer knocking on the front door – they’re already on the couch, eating your snacks, and stealing your patient data.
Welcome to the latest Help Me With HIPAA episode where healthcare becomes the star of a suspense thriller, except the villains are hackers, and the plot twist? They really don’t care how small your practice is. We’re diving into Huntress’ 2025 Cyber Threat Report, which basically confirms that if you’re in healthcare, you’ve got a giant “Hack Me” sign taped to your digital forehead. From script-based exploits to info stealers with boundary issues, this episode breaks down how cyber threats are no longer knocking on the front door – they’re already on the couch, eating your snacks, and stealing your patient data.
In this episode:
Healthcare, The Hacker’s Playground – Ep 535
Today’s Episode is brought to you by:
Kardon
and
HIPAA for MSPs with Security First IT
Subscribe on Apple Podcast. Share us on Social Media. Rate us wherever you find the opportunity.
Great idea! Share Help Me With HIPAA with one person this week!
Learn about offerings from the Kardon Club
and HIPAA for MSPs!
Thanks to our donors. We appreciate your support!
If you would like to donate to the cause you can do that at HelpMeWithHIPAA.com
Like us and leave a review on our Facebook page: www.Facebook.com/HelpMeWithHIPAA
When you see a couple of numbers on the left side of the text below click that and go directly to that part of the audio. Get the best of both worlds from the show notes to the audio and back!
Healthcare, The Hacker’s Playground
[00:51]Huntress 2025 Cyber Threat Report: Threats Targeting the Healthcare Sector
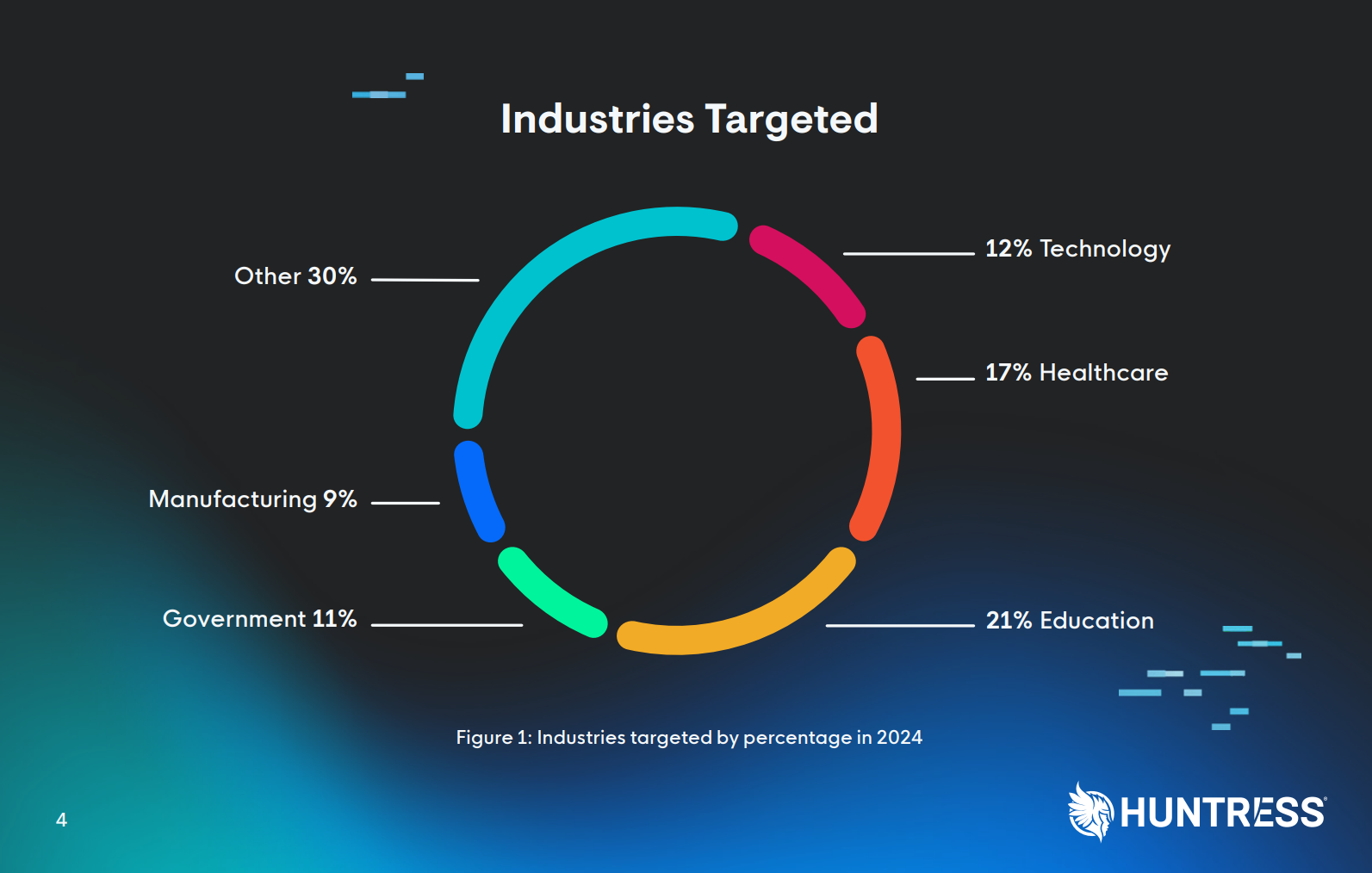
The healthcare industry has never been more connected, or more vulnerable. According to the Huntress 2025 Cyber Threat Report: Threats Targeting the Healthcare Sector, healthcare and education together accounted for nearly 38% of all cyber incidents in 2024. The message is loud and unsettling: attackers have found their favorite playground, and it’s full of PHI.
In this episode, we break down what Huntress uncovered, why healthcare remains a prime target, and how both healthcare organizations and MSPs can build resilience against evolving threats.
The Anatomy of the Problem
Healthcare is unique in the threat landscape. Sensitive data like patient health records, insurance details, and personal identifiers make it one of the most lucrative markets for cybercriminals. But it’s not just the data that’s valuable, it’s the urgency. Hospitals, clinics, and private practices can’t afford downtime, and attackers know it.
The report points to an uncomfortable truth: many healthcare systems still rely on outdated technology and fragmented IT environments. That patchwork creates fertile ground for attackers who exploit old vulnerabilities and use sophisticated techniques once reserved for Fortune-500 targets.
What’s Actually Happening Out There
[06:45] The Huntress data paints a clear picture of 2024’s attack trends:- The size fallacy – As we’ve seen over and over again, you’re not too small to be a target or a victim. The quote from this report is, “Once reserved for targeting large corporations, sophisticated attack methods were used against healthcare organizations of all sizes.”
- Script-Based Exploits are now the top threat vector in healthcare. PowerShell and VBScript-based payloads are being used to establish persistence, download payloads, and evade detection.What are malicious scripts?In general, a script is like a set of instructions for a computer… like a to-do list of actions. The power of scripting is the ability to stack lots of instructions into a single execution. Instead of doing everything one action at a time, a script allows you to run one code (script) to batch multiple actions.
Scripts do not have to involve multiple actions though. They can also do one job, like… “open a backdoor so I can come back later” or “quietly copy files and send them to me”.
These scripts are tiny pieces of code, often just a few lines, but they can do big damage. They can run inside everyday tools like Word, Excel, or email attachments, and they often look harmless until it’s too late.
So, when cybersecurity folks talk about malicious script detection, what they really mean is: “Let’s make sure no one has slipped a fake to-do list into your computers.”
- Infostealers: are quietly exfiltrating sensitive data before ransomware even begins.Infostealers often arrive through phishing emails, malicious ads (malvertising), or bundled in cracked software downloads (be careful of free stuff).Once installed, they scrape browsers, credential vaults, and clipboard data, then exfiltrate it to a remote command-and-control server.
- Malware: Attackers deploy various types of malware, including fileless threats, to disrupt operations or establish persistent network access.
Attack Breakdown – Threats by Industry
[22:20]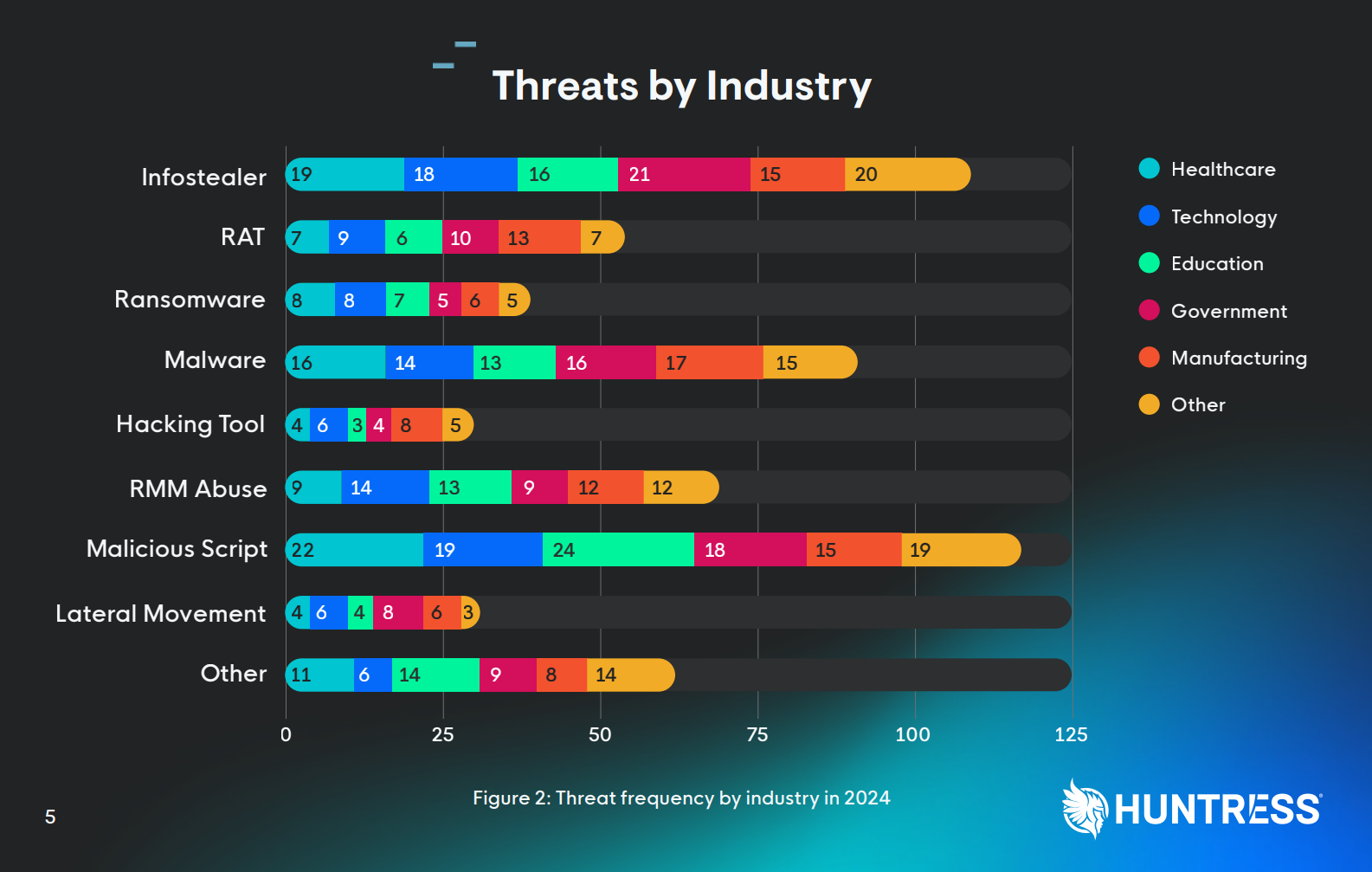
- Remote Access Trojans (RATs) and Java-based exploits are on the rise, taking advantage of older software dependencies still common in medical systems.
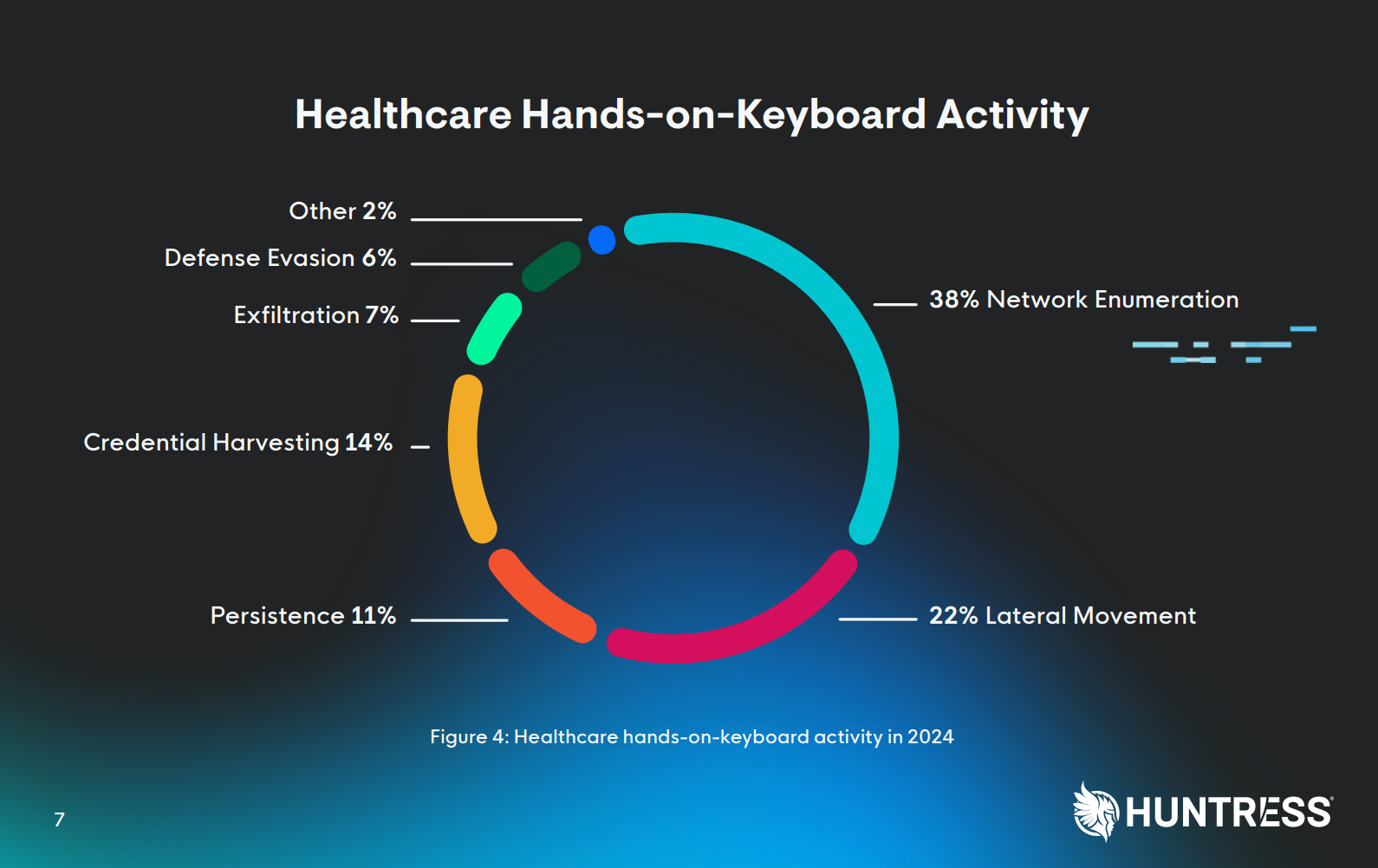
- Hands-on-keyboard intrusions—the human-driven phase of a breach—show attackers spending roughly 38% of their time mapping out networks and domains once inside healthcare environments.Network enumeration is what hackers (and security testers) do right after they get a foothold in a network… they start mapping the digital landscape.This is the digital version of snooping around someone’s office looking for the computers, servers, devices or anything that is connected.
While we’re snooping, we might as well see what operating systems are used, software used, user accounts, permissions, shared files/folders, databases.
Simply put, it is digital reconnaissance. But the information gathered becomes a map the attacker uses for the next move: deciding which systems to attack, which passwords to guess, and which data to steal.
- And the biggest shift: ransomware is no longer just encryption. Data theft and double-extortion schemes are now the default.
The takeaway? Encryption may lock you out, but exfiltration locks you in… into reputational damage, HIPAA violations, and legal fallout.
IT/MSP Role in the Frontline Defense
[29:01] For the IT team and Managed Service Providers, this report should feel like a checklist and a warning rolled into one. Healthcare clients are being targeted precisely because they don’t have enterprise-grade defenses. They need layered protection, visibility, and guidance.Key areas where MSPs (and practices) can make a measurable difference:
- Monitoring script behavior, not just file signatures.
- Proactively managing patching and asset inventory, especially legacy systems and unmonitored endpoints.
- Deploying EDR/ITDR solutions to detect malicious persistence techniques in real-time, with automated responses.
- Implementing network segmentation to contain breaches before they spread.
- Training end-users to recognize phishing and social engineering attempts, because the first click often starts the chain.
- Deploy advanced email security to quarantine and block malicious and spam emails from ever reaching the end-user.
- Deploy advanced DNS filtering to block users from accessing malicious or unwanted sites.
These aren’t just technical measures; they’re business survival tactics.
What Healthcare Leaders Should Be Asking
[42:17] If you’re a healthcare administrator, practice manager, or compliance officer, this report gives you a roadmap of the right questions to ask your IT team or MSP:- “How do we detect and respond to malicious script executions?”
- “Do we have visibility into Java or other outdated components in our environment?”
- “When was our last incident response plan test?”
- “When was our last accurate and thorough security risk assessment?”
- “How are we protecting against data theft (infostealers), not just ransomware encryption?”
If the answer sounds like “don’t worry, we’re probably fine,” that’s your sign to dig deeper.
Resilience Is the New Compliance
HIPAA compliance is no longer enough. The Huntress findings show that the attackers aren’t checking whether you’re compliant, they’re checking whether you’re easy.
Resilience means detecting suspicious behavior early, responding quickly, and limiting damage when (not if) something happens. It’s about creating a living defense system that adapts as attackers evolve.
As Huntress notes, “The TL;DR: Stay vigilant and resilient because cyber threats won’t stop evolving.” The question isn’t whether you’ll face them; it’s whether you’ll be ready.
Closing Thoughts
Cyber threats in healthcare aren’t going away, they’re professionalizing. But the good news is that defenders are too. MSPs, IT directors, and healthcare leaders who collaborate and share threat intelligence are turning the tide.
In the end, cybersecurity in healthcare isn’t just about protecting networks, it’s about protecting trust, safety, and the continuity of care.
In the end, it’s clear that cybersecurity in healthcare isn’t just a tech problem—it’s a survival strategy. Think of it like flossing: nobody likes doing it, but skip it long enough and you’re definitely going to feel the pain. With script-wielding villains, info-stealing gremlins, and AI-enhanced chaos on the rise, it’s time to move past “ignorance is bliss” and into “vigilance is your co-pay.” Ask the hard questions, get the real answers, and maybe finally segment that network like your sanity depends on it—because it kinda does.
Remember to follow us and share us on your favorite social media site. Rate us on your podcasting apps, we need your help to keep spreading the word. As always, send in your questions and ideas!
HIPAA is not about compliance,
it’s about patient care.TM
Special thanks to our sponsors Security First IT and Kardon.


