
Imagine leaving your front door wide open in a neighborhood full of burglars, then acting shocked when your TV disappears. That’s basically what’s happening in healthcare cybersecurity. This week, we’re talking about why hackers are running rampant, how small healthcare practices are prime targets (no, you’re not “too small to matter”), and what basic security steps can actually make a difference. Spoiler alert: Ignoring the problem won’t make it go away.
In this episode:
Healthcare Has A Kick Me Sign – Ep 496
Today’s Episode is brought to you by:
Kardon
and
HIPAA for MSPs with Security First IT
Subscribe on Apple Podcast. Share us on Social Media. Rate us wherever you find the opportunity.
Great idea! Share Help Me With HIPAA with one person this week!
Learn about offerings from the Kardon Club
and HIPAA for MSPs!
Thanks to our donors. We appreciate your support!
If you would like to donate to the cause you can do that at HelpMeWithHIPAA.com
Like us and leave a review on our Facebook page: www.Facebook.com/HelpMeWithHIPAA
When you see a couple of numbers on the left side of the text below click that and go directly to that part of the audio. Get the best of both worlds from the show notes to the audio and back!
Healthcare Has A Kick Me Sign
[04:57]First, just note this article HICP Includes Medical Devices for a reason. We often have been asked about them and now we have a perfect example of why it is one of the 5 threats we must worry about. Here you have it – a medical device that has the potential to cause a lot of problems with patient safety and patient care.
Medical monitoring machines spotted stealing patient data • The Register
Another HICP threat is ransomware and a report has some interesting data to share.
[07:44]- Ransomware isn’t just a problem for big hospital systems—attackers are hitting practices, clinics, and smaller healthcare entities too.
- The idea that “I’m too small to be a target” is leaving way too many organizations wide open.
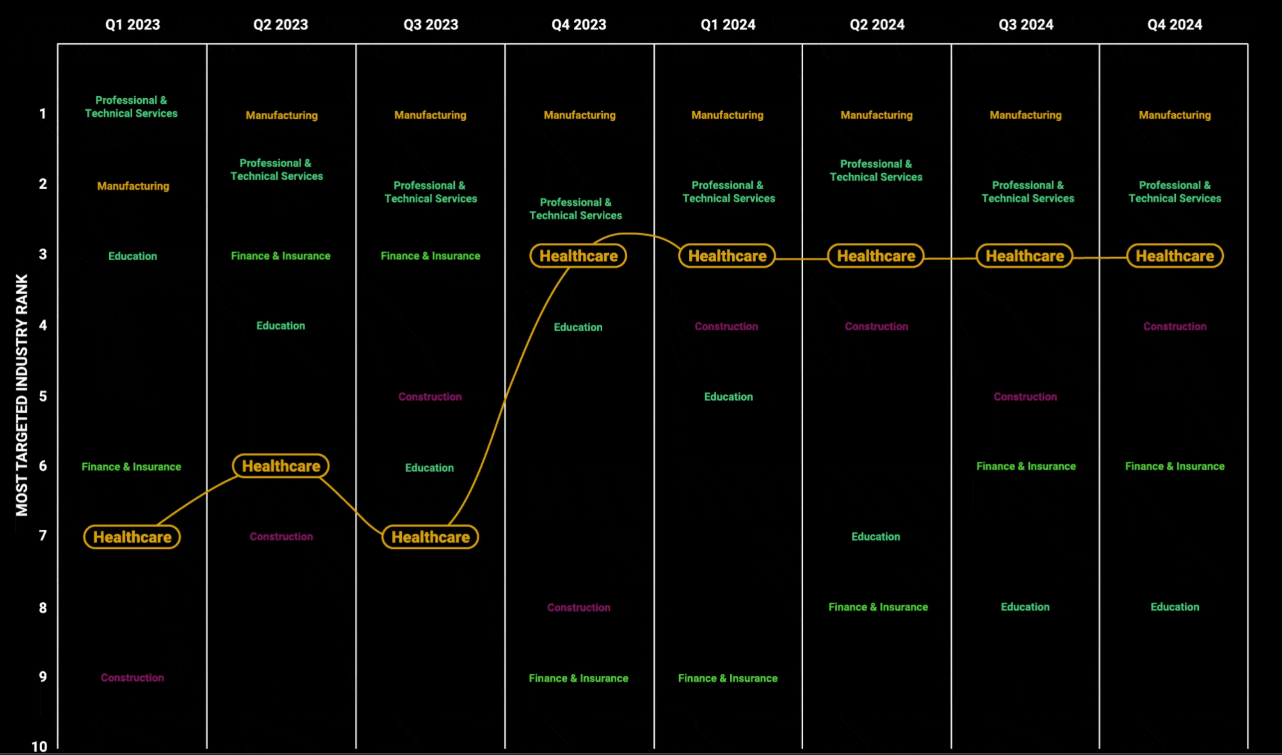
- A new report from Black Kite Report focuses on healthcare and ransomware attacks and we found it very interesting.
📊 Breaking Down the Findings: Who’s Getting Targeted?
- Most people assume ransomware actors only go after big hospital networks, but the report shows a broader range of victims.
- Breakdown of who’s been hit – large systems vs. smaller practices, third-party vendors, and other healthcare-related entities.
- Are attackers shifting focus? Are smaller targets becoming more attractive?
Great charts in this report like this one: Healthcare Ransomware Attack Distribution by Subindustry
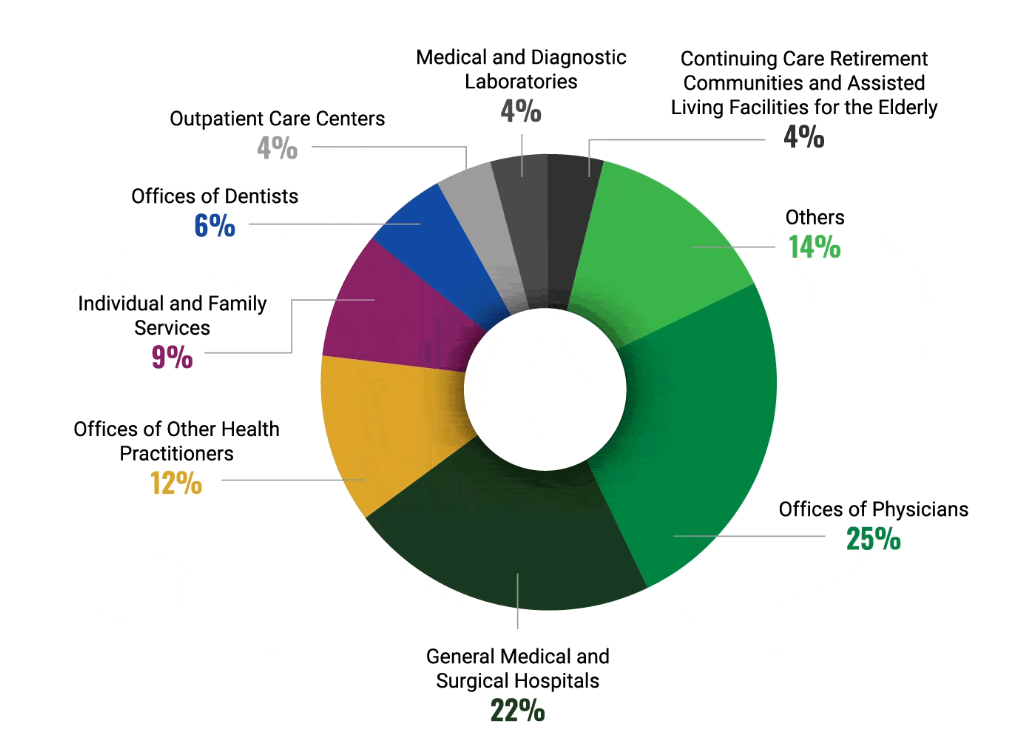
Healthcare attacks have been rising because the criminal’s code of conduct has been tossed out the window. The report connects a lot of it to the big gangs that law enforcement was able to take down over the last few years. Great, but the vacuum won’t last when the amount of money includes billions of dollars each year. New RaaS groups have emerged that are more aggressive about getting the money and less scrupulous about where they get their money. They don’t negotiate with you and they are even starting to just steal the data and leave the systems alone – or it appears that may be happening more often. Then, we don’t have ransomware. It is just a ransom attack.
🚨[18:54] The ‘Not Gonna Happen to Me’ Mentality
- Why smaller organizations think they’re safe – and why that’s a dangerous mindset.
- Attackers know that smaller healthcare groups often have weaker security, fewer resources, and slower response times.
- Many smaller entities don’t think about their value—but to hackers, any access to patient data or hospital networks is valuable.
🛡 [29:29] Cyber Hygiene: The Basics That Stop Big Problems
- Patching: Many attacks still exploit old vulnerabilities that have been publicly known for months or years.
- MFA (Multi-Factor Authentication): Ransomware gangs exploit weak passwords and lack of MFA to break in. Better yet start looking at using passkeys.
- Supply Chain Risk: Just because you outsource IT or services doesn’t mean you’re off the hook. Your vendors can be the weakest link!
We always loop back to the same answers. If we would just do the things we know we need to do things would get better. But, guess what – no one has time or money to do them until it is too late.
Now, add this thought back to where we started with the medical device. What happens when they learn how to use those devices? How long before they start to target them specifically?
🔑 [40:38] Takeaways: How to Stop Being an Easy Target
- Every healthcare entity needs to assume they’re a target.
- Basic security steps can stop a lot of attacks.
- Smaller organizations need to stop relying on “we’re too small” as a strategy.
But this one isn’t ransomware, it is stolen data. Is that the new trend? US healthcare provider data breach impacts 1 million patients probably but maybe not……
At the end of the day, ignoring cyber threats won’t make them disappear—just like pretending that weird clunking noise in your car will somehow fix itself. Healthcare organizations, big and small, need to take action. Patch your systems, enable MFA like your business depends on it (because it does), and don’t just assume IT has everything under control. Hackers certainly aren’t assuming you’re secure—they know you’re not. And if they’re already circling like sharks, do you really want to be the one bleeding into the water without a single defense?
Remember to follow us and share us on your favorite social media site. Rate us on your podcasting apps, we need your help to keep spreading the word. As always, send in your questions and ideas!
HIPAA is not about compliance,
it’s about patient care.TM
Special thanks to our sponsors Security First IT and Kardon.



