
Reports are coming out evaluating cyber threats with stats and details documenting the aftermath of attacks happening in 2020 and the outlook for 2021. Let’s just say they are all on brand with what you expect from anything related to 2020. As you can guess, it isn’t looking good for 2021 based on where we are right now. We reviewed some of the articles and reports evaluating cyber threats so you don’t have to… unless you must.
In this episode:
Evaluating Cyber Threats 2020 to 2021 – Ep 296
Today’s Episode is brought to you by:
Kardon
and
HIPAA for MSPs with Security First IT
Subscribe on Apple Podcast. Share us on Social Media. Rate us wherever you find the opportunity.
The HIPAA Boot Camp
Virtual Edition Aug 17-19, 2021
Great idea! Share Help Me With HIPAA with one person this week!
Thanks to our donors. We appreciate your support!
If you would like to donate to the cause you can do that at HelpMeWithHIPAA.com
Like us and leave a review on our Facebook page: www.Facebook.com/HelpMeWithHIPAA
If you see a couple of numbers on the left side you can click that and go directly to that part of the audio. Get the best of both worlds from the show notes to the audio and back!
Evaluating Cyber Threats 2020 to 2021
[03:28] As the reports come out regarding the aftermath of attacks that happened in 2020 and the outlook for 2021, we can tell that they are all on brand with what you expect from anything related to 2020. Unfortunately, there isn’t much exciting news about improvements in 2021. Seriously, you have to worry about ransomware attacks continuing to evolve and adapt to everything we are doing to prevent them. We wish we could tell you that everything will be ok based on what you have been doing. But it is just not good advice. Why not just keep doing what you have been doing and assume it will continue to work?2019 IBM X-Force Threat Intelligence Index
[08:35] We started 2020 dealing with the new tactic of double extortion by attackers exfiltrating data and threatening to release it if you don’t pay. No more restore and keep going when that started. It proceeded to explode as a tactic and by the end of the year that is getting worse.The evolution of attack vectors and malware families continues. In fact, it seems to just be making the threat landscape wider and deeper. 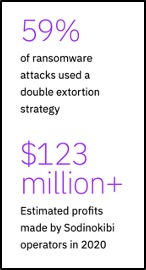
Threat actors were also innovating their malware, particularly malware that targeted Linux, the open source code that supports business-critical cloud infrastructure and data storage. Analysis by Intezer discovered 56 new families of Linux malware in 2020, far more than the level of innovation found in other threat types.
The note in the IBM report concerning the growth of Linux malware in 2020 should be a wake up call to all those IT professionals. Many have relied on the seemingly low amount of malware aimed at that OS as a sort of comfort zone. It can be that no longer. A 40% increase in Linux malware year over year is just an astonishing level of growth compared to the assumed level of vulnerabilities expected in the OS.
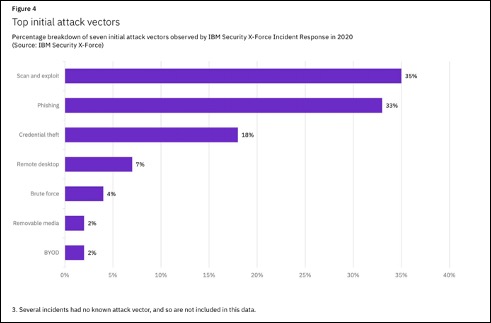
You can see from the chart above that the top ways that cyber criminals try to attack are #1 scanning for weaknesses into networks and then exploit what they can once inside and then #2 phishing attacks. That shouldn’t be too surprising. The thing that is interesting is that BYOD made this list. We’ve talked about this before that you need to truly evaluate whether to allow employees or even vendors or folks you meet to use their own devices to connect to the office WiFi. Just allowing your staff to plug their cell phone into a computer to charge it can open you up to attack. The computer isn’t just charging the phone, it has access to data and software, even malware, that could be on the phone.
Mark of Ransomware’s Success: $370 Million in 2020 Profits in HealthInfoSecurity.com
[21:50] When we look at the stats on the biggest ransomware families that are attacking the healthcare sector, Maze accounted for 20 infections alone and they were the ones that started with double extortion tactics. But there are 17 other ransomware families listed in this report that are still hitting the healthcare sector.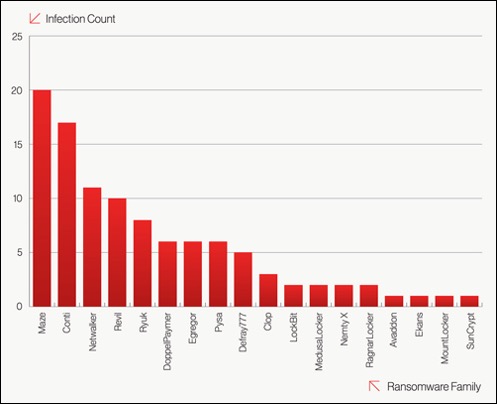 Confirmed healthcare sector victim count by ransomware family in 2020 (Source: CrowdStrike)
Confirmed healthcare sector victim count by ransomware family in 2020 (Source: CrowdStrike)
HIPAA Say What!?!
[23:10] This week it comes in the middle of the episode. We needed it to be included here because there were two specific healthcare scenarios in the news that we want to discuss and because, frankly, we get to make the rules… so we moved it here this week.NC: FBI investigating 8-day cyber attack after ransomware attack on Allergy Partners
GA: Atlanta Allergy & Asthma hit by Nefilim threat actors
So, two allergy practices, one in NC and one in GA, were hit by the same ransomware bug and data was released on the web. We hear all the time “We don’t have any PHI on our computers. It’s all in the cloud EHR or on the server.”
That’s clearly not the case in the GA breach. DataBreaches.net reported that a spreadsheet, from Atlanta Allergy and Asthma, organized by type of insurance that included records on outstanding claims from 2017 and 2018 and there were more than 100 audits of medical record reports left sitting out there unprotected. The article even shows a screenshot of a portion of one of the medical records. This data was released on the darknet and the ransomware attacker says we have 19 GB more of your data and we will release it if you don’t pay up.
The Allergy Partners practice in Asheville, NC was attacked on Feb. 23, 2021. The attack lasted for eight days because they were being asked for $1.75 million. They were unable to provide allergy shots at two offices. That’s a steep ransom, but not being able to provide shots to your patients takes it to a different level. That can be reputational damage and loss of patients at the practice because they had to go somewhere else for their shots.
This goes beyond just having IT. You have to have an effective privacy and security program throughout the organization. HIPAA compliance is NOT security, folks. Even Roger Severino said HIPAA is the floor. It is the bare minimum you should do. Think about it. HIPAA was established in 2005 and now 16 years later healthcare is still getting hit by attacks more and more each year. Checking the box for compliance is nowhere remotely like an actual effective privacy security program that I can prove I am doing.
New Free Services for Ransomware Affiliates
Ransomware gang plans to call victim’s business partners about attacks
[33:58] A new ad featured by REvil RaaS gang shows they are upping the game to better “serve” their affiliates. They will include this “free service”.The REvil ransomware operation announced this week that they are using DDoS attacks and voice calls to journalists and victim’s business partners to generate ransom payments.
The REvil ransomware operation, also known as Sodinokibi, is a ransomware-as-a-service (RaaS) where the ransomware operators develop the malware and payment site, and affiliates (adverts) compromise corporate networks to deploy the ransomware.
As part of this deal, the REvil developers earn between 20-30% of ransom payments, and the affiliates make the remaining 70-80%.
To pressure victims into paying a ransom, ransomware gangs have increasingly turned to a double-extortion tactic, where attackers steal unencrypted files that they threaten to release if a ransom is not paid.
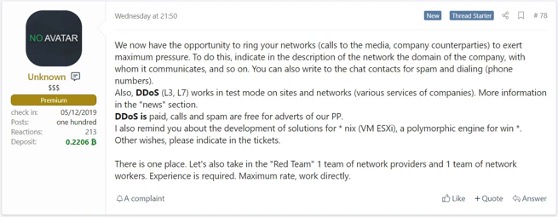
So this new free service adds a third or maybe a fourth extortion tactic. This is such a big deal.
“Group-IB says 64% of all ransomware attacks it saw in 2020 came from ransomware-as-a-service operations, which use an affiliate-based model. RaaS operators provide versions of their ransomware – often frequently updated – to affiliates as a service. Those affiliates then infect victims’ devices. For every victim who pays a ransom, the affiliate and operator share profits.”
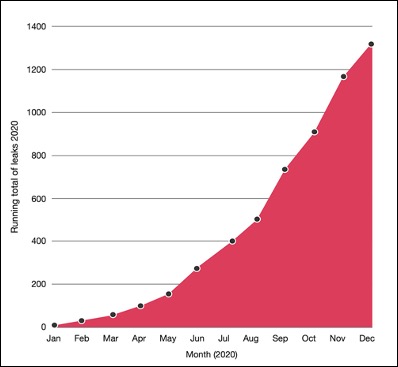
Running total of organizations with data leaked via ransomware gangs’ data leak sites (Source: PwC)
Outlook for 2021
[43:02] The BlackBerry 2021 threat report included one stark reminder for healthcare that what we have known is changing quickly and moving forward as we always have it really not an option any more.Ransomware threats to watch for in 2021 include crimeware-as-a-service
Threat Actors Contacting Patients as Part of Healthcare Extortion Strategies
“Throughout 2020, healthcare organizations continued to top the target list of cyber attacks. The healthcare industry is critical for providing services during the pandemic and also holds confidential data like medical records, which are extremely valuable to attackers. Threat researchers saw cases where medical records were weaponized to facilitate the attacker’s objectives.
In October 2020, a Finnish psychotherapy center had their systems attacked and patient data stolen. Not only did the attackers demand a ransom from the psychotherapy center, they also contacted patients individually seeking a ransom of 200 Euros in bitcoin. The threat actors ultimately published the records of at least 300 patients via a Tor site135. This tactic could become more popular throughout 2021, especially when combined with traditional ransomware attacks. Furthermore, it could also provide additional pressure on healthcare service providers from patients who are being extorted individually, leading to a higher probability of ransom payment.
The “calling others threat” really hurts in healthcare because they are calling your patients. If your specialty warrants extra levels of confidentiality you can expect to be a bigger target than ever before. You may seem small but if your patient list allows them to call each one and demand a ransom from each one. How long will you be in business if that happens?
So, the good news is 2020 is done and we’re aware and there are things you can do about it. You can’t just keep doing what you’ve always done. We’re way past that now. A simple antivirus program doesn’t cut it anymore. You need the multilayered security approach that is part of your privacy and security program that you can use to prove you’re doing all the other stuff. IT professionals should get caught up on these attacks and be proactive in discussion with clients. Practices need to have these discussions with IT and find what is reasonable to do and then make sure you’re doing it and can prove that you’re doing it. That’s the key element, because if you do get hit, you need to be able to prove you were doing all you could to have a fighting chance.
Remember to follow us and share us on your favorite social media site. Rate us on your podcasting apps, we need your help to keep spreading the word. As always, send in your questions and ideas!
HIPAA is not about compliance,
it’s about patient care.TM
Special thanks to our sponsors Security First IT and Kardon.


