 If cybercrime truly is the number one problem with mankind and healthcare is the number one cyber attacked industry is it because healthcare sucks at cybersecurity? We could certainly make an argument for many answers to that question. However, a recent report published by SecurityScorecard indicates that may be, at least, part of the problem. So, does healthcare suck at cybersecurity? In this episode, we review that report and add some thoughts of our own to mix, as always.
If cybercrime truly is the number one problem with mankind and healthcare is the number one cyber attacked industry is it because healthcare sucks at cybersecurity? We could certainly make an argument for many answers to that question. However, a recent report published by SecurityScorecard indicates that may be, at least, part of the problem. So, does healthcare suck at cybersecurity? In this episode, we review that report and add some thoughts of our own to mix, as always.
In this episode:
Does healthcare suck at cybersecurity? – Ep 144 – Mar 9
Today’s Episode is brought to you by:
Kardon and HIPAA for MSPs / Security First IT
Where to meet us
- The Georgia Access Management Association (GAMA) March 16, in ATL at PatientCo offices in Buckhead
- 2018 JAWS Society Annual Conference, (a national society of oral and maxillofacial administrators) April 22-25 in Newport Beach, CA
- North GA Medical Management Association in Dalton, GA June 14
Learn more about our Live HIPAA Boot Camp and request one in your area: www.HelpMeWithHIPAA.com/bootcamp [3:00]
The HIPAA Boot Camp – Virtual Edition – For the first time our Boot Camp is going virtual.
- The virtual format is done in 3-4 hour online sessions over a two week period.
- March 13/14/15 and 21/22.
- $997 early bird special rate through Feb 28th.
- $1,297 March 1 – 13.
- One registration covers attendance of up to 3 people on your team.
- One on one planning sessions included. You schedule them for after the end of class.
- Access to recordings and all resource material available online for at least 6 months.
Want to be part of Help Me With HIPAA? Become a Patreon at www.HelpMeWithHIPAA.com/give
HMWH App now has more features. You can now access a PDF with the show notes ready for your HIPAA training documentation! Find it under the bonus feature in the app for both the Apple and Android versions. It is a little gift box on the app bar.
Like us and leave a review on our Facebook page: www.Facebook.com/HelpMeWithHIPAA
[6:54]
Does healthcare suck at cybersecurity?
The report was done by Security Scorecard: SecurityScorecard 2018 Healthcare Report, A Pulse on the Healthcare Industry’s Cybersecurity Risks does provide some interesting information. They start with a big punch right off the bat by saying that since their 2016 report on cybersecurity in healthcare the industry has a whole has dropped 6 spaces. Yes, 6!. That wouldn’t be so bad if it was from say 41st to 47th out of 100 but it is 6 spaces out of a total of 18 industries. That is falling down the list a whole one-third of the way.
First, let’s just point out they did some pretty extensive evaluation in their study to make sure they had a good bit of information on healthcare itself. They analyzed “terabytes of information” from 1200 healthcare companies from July 2017 through December. They also include 10 different risk factors in their considerations.
They list their key insights as
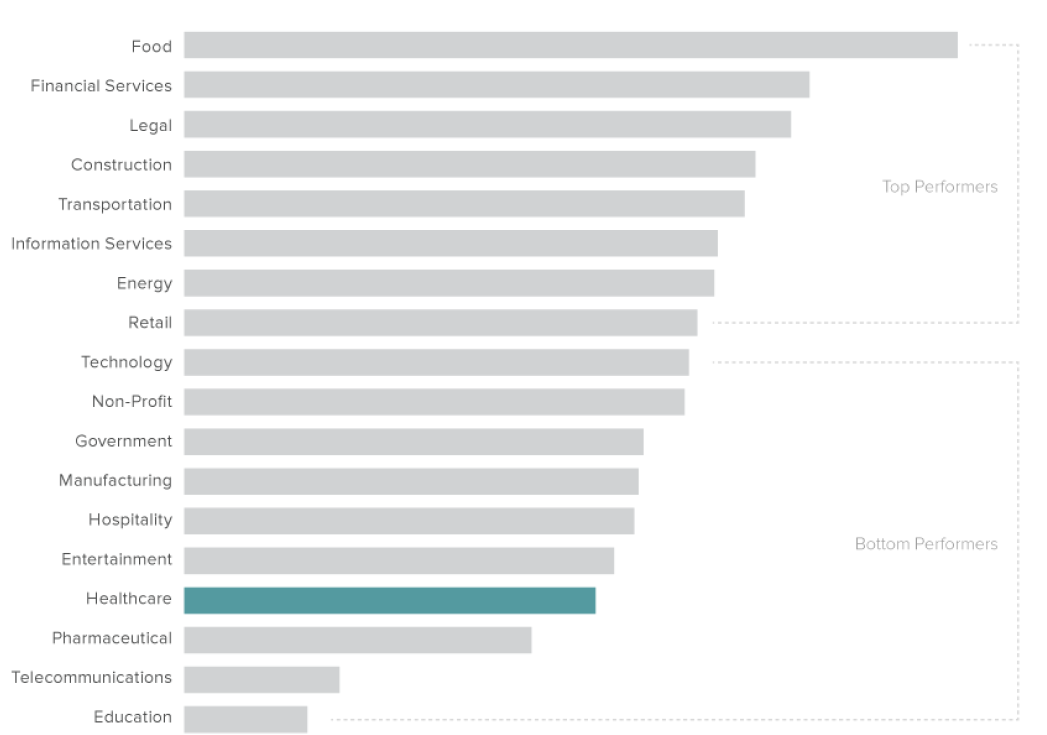
- The healthcare industry ranks fifteenth in terms of cybersecurity health when compared to 17 other major U.S. industries.
- The healthcare industry is one of the lowest performing industries in terms of endpoint security.
- Social engineering attacks continue to be a common attack vector.
- The most common cybersecurity issues in the healthcare industry related to poor patching cadence.
- Healthcare organizations, even top performers, struggled with patching cadence and network security.
At first, I thought it was good that there were at least three industries below healthcare but….. The three are Pharmaceutical (almost part of healthcare really), Telecommunications (which we must have to communicate and connect), and Education (wow, aren’t there a ton of teaching hospitals out there!). Not such a comforting list when I evaluate those.
Here is a good and embarrassing thing, though, the number one industry – Food. Under that is Financial Services and Legal. Another unsettling point is that 4 above us is Government and 5 above us are Non-Profit.
I often make the point of teaching in all of my classes just how healthcare records are so valuable. This data is by far the broadest and deep details captured about any person. It extends throughout their life and all the details of their job history, family history, and much more. It almost seems like the industry takes all of our concerns about this data being under attack as if we are tilting at windmills. I assure you, friend Sancho, those are indeed hulking giants that we must battle!
As the report continues into the details of the risks themselves it becomes clear we have much to address. Maybe even much more than any of the 17 other industries.
Does healthcare suck at cybersecurity? If you only look at how it compares to other US industries then that appears to be the case.
Endpoints
First, this is a term we nerds use all of the time but many people may not really understand what we are talking about here. An endpoint is any device that is connected to a network. In a basic sense, all devices on the network are endpoints except for those routers and switches that move the data from one endpoint to another endpoint.
They made an excellent point, well a point that goes along with what we have been saying for years.
It is painful for me to look at organizations celebrate that they finally got rid of the last Windows XP computer. The problem is the vast majority of the ones that are now current are running Windows 7. That end of life is coming up on us rapidly. January 14, 2020, is less than 2 years away. They are celebrating just now in 2018 getting rid of XP that should have been gone before April 8, 2014. Four years AFTER the devices should no longer be used in a secure environment! I guess we need an episode to discuss planning for Windows 7’s retirement party soon.
In this comparison, healthcare was ranked 16th. Not surprised but at least it wasn’t dead last.
Does healthcare suck at cybersecurity? If you only look at endpoints then that appears to be the case.
Social Engineering
When we say social engineering what do we really mean? It is things like crazy conspiracy theories on social media, phishing attacks, and the long list of attacks that are aimed at individual users to trick them into assisting in a cyber attack in some way.
Comparing healthcare’s ability to deal with people being tricked by social engineering vs all those others still not pretty. There are only two industries below healthcare! That means 16 out of 18.
Does healthcare suck at cybersecurity? If you only look at social engineering then that appears to be the case.
Patching Accounts for the Most Prevalent Cybersecurity Issues in the Healthcare Industry
Patching
Let’s be clear on this patching thing. We talk about it often. It means you need to update your operating systems AND applications regularly. If you can longer get updates from them then you should stop using them and get new solutions. They are finding new problems every single day. This patching cadence they mention really does matter. Get a beat going on this and make it happen.
In fact, in this report, they state that:
Patching Accounts for the Most Prevalent Cybersecurity Issues in the Healthcare Industry
Here the report makes the point that there are 5 primary issues relating to cybersecurity in the healthcare industry. Of those 5, three of them could be solved or at least limited with proper patching cadence.
The top five issues are:
- Typosquatting – When the bad guys set up a website like microsof.com which is Microsoft without the T. You make a typo and end up at their website which is infected and tricking you into downloading things. They are fake web addresses so you don’t notice them behind their nice smile and a fancy suit.
- Slow patching cadence – This one we know. The Wannacry ransomware attack spread using a patch that had been available for months. Equifax’s problems were related to a patch that was available for months. If you vendor says you can’t load it then ride them until you can. Or, find another vendor.
- Vulnerable host – If you only worry about patching your servers but leave all those unpatched devices out there then you have a vulnerable host on your network. They are what an active attacker looks for first thing on your network. Even one is a problem, remember the previous quote. However, this also includes things like open ports and weak security configurations on your computers because you don’t use a checklist to be sure it is done the same way each time.
- Weak cipher – This one deals with encryption. Either no encryption or inadequate encryption is employed on many devices. Just because someone says it is encrypted it isn’t a bad idea to ask them “how”?
- End-of-life date – And now we get our Windows XP computers. No, it isn’t just XP that is the problem. Any device that is no longer supported or maintained by the developer is past its end-of-life date.
The final points they included in this report can be somewhat conflicting. First, it says using HIPAA requirements does help the top performers in healthcare achieve better scores. However, it also points out that like any other long-term issue, the first step is accepting you have a problem. So, yes it seems that healthcare does indeed suck at cybersecurity. We have to accept our problems before we can face them head on and fix them.
Please remember to follow us and share us on your favorite social media site. Rate us on your podcasting apps, we need your help to keep spreading the word. As always, send in your questions and ideas!


