Cybersecurity advice is everywhere — frameworks, standards, best practices, expert opinions — enough PDFs to last you the rest of the year. But for small and mid-sized businesses, the real question isn’t “What guidance exists?” It’s “What should we actually do that lowers our chances of having a really bad cyber day?” If you’ve ever looked at a massive cybersecurity framework and thought, “This feels like studying for a final exam I didn’t sign up for,” you’re not alone. That’s where CISA’s updated Cybersecurity Performance Goals (Version 2.0) come in. Designed to be practical, prioritized, and actually usable, this streamlined approach may be the clearest cybersecurity foundation SMBs have seen yet. In this episode, we break down what changed, why it matters, and how to use it.
In this episode:
CISA CPGs V2 Might Be the Best SMB Cybersecurity Approach Yet – Ep 548
Today’s Episode is brought to you by:
Kardon
and
HIPAA for MSPs with Security First IT
Subscribe on Apple Podcast. Share us on Social Media. Rate us wherever you find the opportunity.
Great idea! Share Help Me With HIPAA with one person this week!
Learn about offerings from the Kardon Club
and HIPAA for MSPs!
Thanks to our donors. We appreciate your support!
If you would like to donate to the cause you can do that at HelpMeWithHIPAA.com
Like us and leave a review on our Facebook page: www.Facebook.com/HelpMeWithHIPAA
When you see a couple of numbers on the left side of the text below click that and go directly to that part of the audio. Get the best of both worlds from the show notes to the audio and back!
CISA CPGs V2 Might Be the Best SMB Cybersecurity Approach Yet
[00:35] Cybersecurity guidance is everywhere. Frameworks, standards, best practices — there’s no shortage of advice. But when you talk to real organizations, especially smaller ones, the struggle isn’t a lack of information.It’s knowing what actually lowers the odds of a bad cyber day.
Most organizations are trying to answer three very practical questions:
- What should we be doing that actually makes us safer?
- What should we focus on first, second, and maybe later?
- And how do we explain to leadership why any of this work matters?
That’s a big reason why CISA created the Cross-Sector Cybersecurity Performance Goals, or CPGs.
Cybersecurity Performance Goals 2.0 (CPG 2.0) | CISA
Cross-Sector Cybersecurity Performance Goals, Version 2.0 (pdf)
The CPGs were always designed to cut through the noise — focusing on clear, outcome-driven cybersecurity practices for everyday IT and operational technology environments. Not perfect security. Not theory. Just the things that most consistently help prevent real-world incidents.
But with Version 2, CISA made a meaningful leap forward in actually delivering on that promise. They identified 4 challenges they ran into with the first version to address in this one:
- OT cybersecurity often remains overlooked and under-resourced. Primary focus has been on business IT systems.
- Many organizations have not adopted fundamental security protections. Basics like MFA still not happening,
- Small- and medium-sized organizations are left behind. Small organizations struggle to identify where to invest to improve their cybersecurity posture and how to effectively implement cybersecurity protections.
- Lack of consistent standards and cyber maturity. This is something we talk about often – significant inconsistency in investment and practices.
The updated CPGs don’t just list what organizations should do — they address the real barriers that kept many organizations from acting in the first place. Version 2 sharpens the focus on foundational actions tied to real threats, uses clearer language, and adds structure that helps organizations make practical decisions about where to spend time, money, and effort.
Instead of overwhelming teams with options, CPGs Version 2 gives organizations a more realistic, usable starting point — one that finally aligns intent with execution and makes “doing something meaningful” achievable, especially for smaller organizations.
Don’t get too excited though. They still include this disclaimer kind of point right up front:
“CISA’s CPGs are not comprehensive. They do not identify all the cybersecurity practices needed to protect national and economic security and public health and safety. They capture a core set of cybersecurity practices with known risk-reduction value broadly applicable across sectors. ”
What Are the CPGs (And What They Are Not)
[00:00]- What CPGs actually are
- CISA’s Cross-Sector Cybersecurity Performance Goals
- A prioritized minimum set of cybersecurity practices
- Designed to reduce real-world risk, not check compliance boxes
- Who they are for
- All sectors, but especially small and medium-sized organizations
- Organizations that don’t have security teams or framework expertise
- What they are not
- Not a full cybersecurity framework
- Not a replacement for NIST CSF
- Not a maturity model
- Not mandatory
- How to think about them
- The “floor,” not the ceiling
- The shortest path to meaningfully reducing risk
Overview of Key Changes in CPG 2.0
[15:05]- Addition of the Govern function – Puts in that leadership accountability, the oversight, actual planning and management of these cybersecurity practices.
- Consolidation and simplification of goals – Reduced and reorganized overlapping goals into a smaller, clearer set of priorities, eliminating duplication and making the framework more streamlined and manageable across sectors.
- Address Emerging threats and gaps – Added four new goals:
- Proactive Program Management
- Managed Service Provider Risk
- Least-Privilege Enforcement
- Incident Communication Procedures
- Removed goals without losing intent – Eliminated standalone sections while preserving their core intent by integrating related concepts into unified goals, simplifying execution without sacrificing substance.
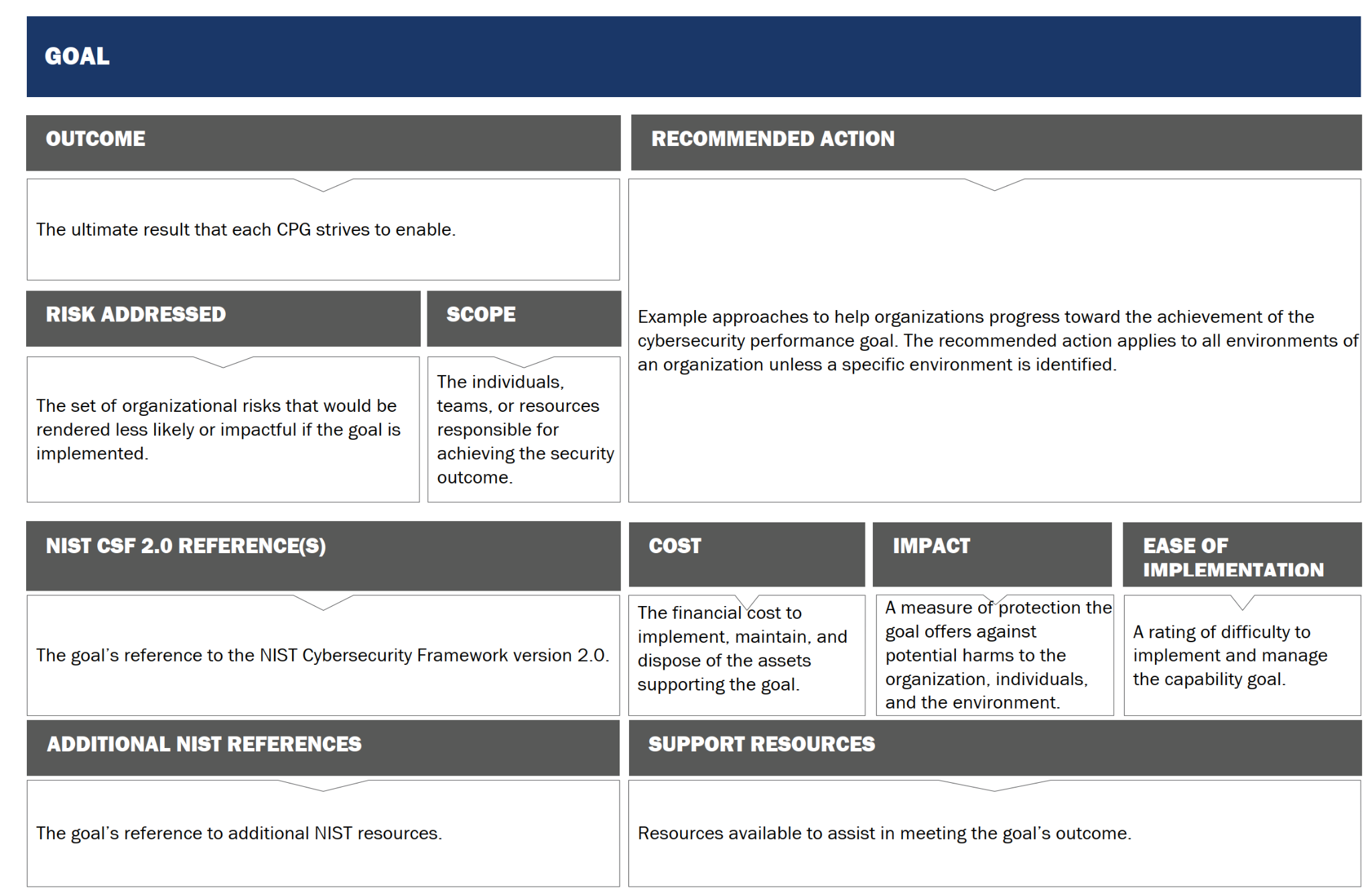
- Methodology and documentation updates – Added Cost, Impact, and Ease of Implementation ratings to the CPG Report and Checklist
Govern
[24:27]- Establish Cybersecurity Responsibilities
- Manage Cybersecurity Oversight
- Maintain Incident Response Plans
- Supply Chain Incident Reporting & Vulnerability Disclosure
- Manage Risks From Managed Service Providers
Identify
[30:09]- Manage Organizational Assets
- Mitigate Known Vulnerabilities
- Obtain Independent Validation Of Cybersecurity Controls
- Maintain Vulnerability Disclosure/Reporting Process
- Document Network Topology
Protect
[33:42]- Change Default Passwords
- Establish Minimum Password Strength
- Create Unique Credentials
- Revoke Credentials For Departing Staff
- Monitor Unsuccessful (Automated) Login Attempts
- Implement Multifactor Authentication (Mfa)
- Administrators Maintain Separate User And Privileged Accounts
- Implement The Principles Of Least Privilege
- Implement Logical/Physical Network Segmentation
- Implement Cybersecurity Training
- Utilize Strong Encryption
- Enable Email Security
- Disable Autorun & Macros By Default
- Establish Change Management Processes
- Maintain System Backups & Restoration Ability
- Maintain Hardware & Software Approval Process
- Maintain Log Collection & Storage
- Prohibit Connection Of Unauthorized Devices
- Secure Internet-Facing Devices
Detect
[40:25]- Establish Malicious Code Detection
- Identify Adverse Events
Respond
[43:20]- Establish Incident Communication Procedures
- Establish Incident Reporting Procedures
Recover
[46:00]- Execute Incident Recovery Plan
This update turns the CPGs into a clear, leadership-friendly roadmap that helps organizations move from “we know we should do better” to concrete, defensible action, making it harder to justify ignoring them when they represent a practical, voluntary floor of protections designed specifically to close the most common and damaging cybersecurity gaps.
At the end of the day, the CISA CPGs Version 2.0 aren’t trying to turn you into a cybersecurity compliance superhero. They’re giving you a solid foundation — the subfloor before you start installing hardwood. If you’re doing these things, you’re covering the basics that actually reduce risk. Not the flashy stuff. Not the “we bought a tool so we’re good” stuff. The real, practical controls that make attackers’ lives harder and your bad-day odds lower. And for most small businesses, that’s exactly where you need to start.
Remember to follow us and share us on your favorite social media site. Rate us on your podcasting apps, we need your help to keep spreading the word. As always, send in your questions and ideas!
HIPAA is not about compliance,
it’s about patient care.TM
Special thanks to our sponsors Security First IT and Kardon.


