 Healthcare still has a giant “Hack Me” sign taped to its back — and the latest reports from Mandiant and Verizon are here to confirm it. These cybercrime breakdowns reveal that attackers are smarter, sneakier, and spending more time poking around your network than ever before. Waiting to secure your systems until after a breach is like installing a smoke detector after the house has already burned down — by the time you smell smoke, it’s too late. From dwell times that feel more like extended Airbnb stays to small businesses learning that “we’re too small to target” isn’t a strategy, the findings hit hard and the lessons come wrapped in some well-placed snark.
Healthcare still has a giant “Hack Me” sign taped to its back — and the latest reports from Mandiant and Verizon are here to confirm it. These cybercrime breakdowns reveal that attackers are smarter, sneakier, and spending more time poking around your network than ever before. Waiting to secure your systems until after a breach is like installing a smoke detector after the house has already burned down — by the time you smell smoke, it’s too late. From dwell times that feel more like extended Airbnb stays to small businesses learning that “we’re too small to target” isn’t a strategy, the findings hit hard and the lessons come wrapped in some well-placed snark.
In this episode:
Busy, Broke, and Breached – Ep 508
Today’s Episode is brought to you by:
Kardon
and
HIPAA for MSPs with Security First IT
Subscribe on Apple Podcast. Share us on Social Media. Rate us wherever you find the opportunity.
Great idea! Share Help Me With HIPAA with one person this week!
Learn about offerings from the Kardon Club
and HIPAA for MSPs!
Thanks to our donors. We appreciate your support!
If you would like to donate to the cause you can do that at HelpMeWithHIPAA.com
Like us and leave a review on our Facebook page: www.Facebook.com/HelpMeWithHIPAA
When you see a couple of numbers on the left side of the text below click that and go directly to that part of the audio. Get the best of both worlds from the show notes to the audio and back!
HIPAA Briefs
[02:26] Two more settlements were announced by OCR.First was another big dollar amount settlement of $600,000 with a 2 year CAP.
PIH Health, Inc settlement with OCR PIH Health is a care provider in Los Angeles, CA
“Hacking is one of the most common types of large breaches reported to OCR every year,” said OCR Acting Director Anthony Archeval. “HIPAA-regulated entities need to be proactive and remedy the deficiencies in their HIPAA compliance programs before those deficiencies result in the impermissible disclosure of patients’ protected health information.”
The settlement resolves an investigation that OCR conducted after receiving a breach report from PIH on January 10, 2020. The breach report stated that between June 11 and June 21, 2019, a phishing attack compromised forty-five, yes 45, of its employees’ email accounts, resulting in the breach of 189,763 individuals’ unsecured ePHI. PIH reported that the ePHI disclosed in the phishing attack included affected individuals’ names, addresses, dates of birth, driver’s license numbers, Social Security numbers, diagnoses, lab results, medications, treatment and claims information, and financial information.
OCR’s investigation found multiple potential violations of the HIPAA Rules, including:
- Failure to use or disclose protected health information only as permitted or required by the HIPAA Privacy Rule.
- Failure to conduct an accurate and thorough risk analysis of the potential risks and vulnerabilities to the confidentiality, integrity, and availability of ePHI held by PIH.
- Failure to notify affected individuals of a breach of unsecured protected health information within 60 days of its discovery.
- Failure to notify the HHS Secretary of a breach of unsecured protected health information within 60 days of its discovery.
- Failure to notify the media of a breach of unsecured protected health information within 60 days of its discovery.
And then there was one more two days later.
[10:58] Comprehensive Neurology, PC settlement with OCR $25k and 2 year CAPThis settlement marks OCR’s 12th Ransomware Enforcement Action and 8th Enforcement Action in OCR’s Risk Analysis Initiative.
On April 25th, OCR dropped the latest settlement. This one is with a small neurology practice in Hollis, New York, called Comprehensive Neurology, PC.
Comprehensive consists of a single physician neurologist, Dr. Gene Zitser. Comprehensive is in Hollis, New York. Comprehensive is an S corporation with five full-time staff members not including Dr. Zitser.
What happened?
On December 17, 2020 OCR received a breach notification report from Comprehensive. Comprehensive reported that on December 14, 2020, Comprehensive became aware of an issue with its systems when an employee discovered that they could not access medical records. Comprehensive’s internal investigation determined that it had been subjected to ransomware and that 6,800 individuals may have been affected by the breach incident.
For their HIPAA failures, Comprehensive gets a $25,000 fine and a 2-year CAP. Their violation listed was failing to do an SRA. Their CAP looks like there were probably some other things that weren’t done.
The usual suspects are discussed in the Resolution Agreement CAP:
- Conducting an accurate and thorough risk analysis to determine the potential risks and vulnerabilities to the ePHI in its information systems;
- Developing and implementing a risk management plan to address and mitigate reduce security risks and vulnerabilities identified in the risk analysis;
- Reviewing, and to the extent necessary, revising its written policies and procedures to comply with the HIPAA Rules; and
- Training its workforce on its HIPAA policies and procedures.
“Effective cybersecurity requires proactively implementing the HIPAA Security Rule requirements before a breach or cybersecurity incident occurs,” said OCR Acting Director Anthony Archeval. “OCR urges health care entities to prioritize compliance with the HIPAA Security Rule risk analysis requirement.”
Busy, Broke, and Breached
[15:58] We have two reports that just came out to reiterate what we have been hearing anecdotally and in other publications. Both are long term annual reports that we have counted on over the years.Basically the theme is the same if you’re a healthcare provider these days. You might as well hang a neon ‘Hack Me!’ sign on your server or as we said recently the Kick Me sign. And no, updating your ‘We Care About Your Privacy’ webpage won’t cut it anymore. Let’s hit the high points and the recommendations which are the most important part.
M-Trends 2025: Data, Insights, and Recommendations From the Frontlines | Google Cloud Blog
Mandiant Consulting releases the 16th edition of their annual report. This report uses data from their actual incident response team experiences. 450,000 hours of Mandiant Consulting investigations were reviewed.
Stolen credentials now represent 16% of Mandiant’s investigations and have become the second most common initial infection vector. This is due to a significant increase in the use of infostealers observed by Mandiant.
Highlights from M-Trends 2025 Report
Key Points:
- Exploits were the top initial infection vector (33%), followed by stolen credentials (16%) and email phishing (14%).
- Global median dwell time (how long attackers lurk before detection) rose slightly to 11 days from 10. But dwell time was 26 days when external entities notified the victims. 5 days when the criminals notified the victim mostly in the ransomware cases. Organizations that catch it themselves usually take 10 days.
- Ransomware is involved in 21% of all incidents. Notably, financially motivated threat actors made up 55% of threat groups.
- Infostealer malware, cloud compromise risks, and unsecured data repositories are big problems.
- Insider threats from North Korean IT workers are real—posing new insider risks.
- Centralized authority, such as single sign-on portals, are being targeted by attackers to gain broad access to cloud-based stores.
Healthcare-Specific Findings:
- Healthcare is one of the top targeted sectors, right behind high tech and retail.
- Ransomware, cloud compromises, and credential theft pose particularly high risks for healthcare organizations.
- Healthcare sector incidents mostly tied to financially motivated groups but also include espionage-focused campaigns targeting sensitive healthcare data.
Highlights from the Verizon 2025 DBIR
[27:00] This report is one most often cited over the years and taking the time to read it is recommended not just for that reason but also because they usually include some humor and wit in their writing. For example:Grace us with your physical eyeballs and human cognition perfected over thousands of years of evolution. We promise it will be worth it.
The Verizon DBIR team’s analysis of 22,052 real-world security incidents in 139 countries. They found that 12,195 were confirmed data breaches affecting organizations of all sizes and types. They said this is the most they ever covered in a single report which means their data just keeps getting better. This is the 15th year they published this report.
2025 Data Breach Investigations Report | Verizon
Although the threat landscape can vary somewhat due to organizational size, mission and location, there are always certain overarching themes that seem to predominate our dataset regardless of any of these variables. This year is no exception. Possibly the most obvious and noteworthy among them is the role that third-party relationships play in how and why breaches occur.
Incident vs Breach definition was nice to see in the opening pages. We run into some confusion about this A LOT. All breaches are incidents but not all incidents are breaches.
Key Points:
- Credential abuse remains the most common initial access vector, but exploitation of vulnerabilities surged 34% over last year, now accounting for 20% of breaches. It is interesting to note the difference here vs the M Trend report above. This is exactly why we use several different ones to keep track of the big picture.
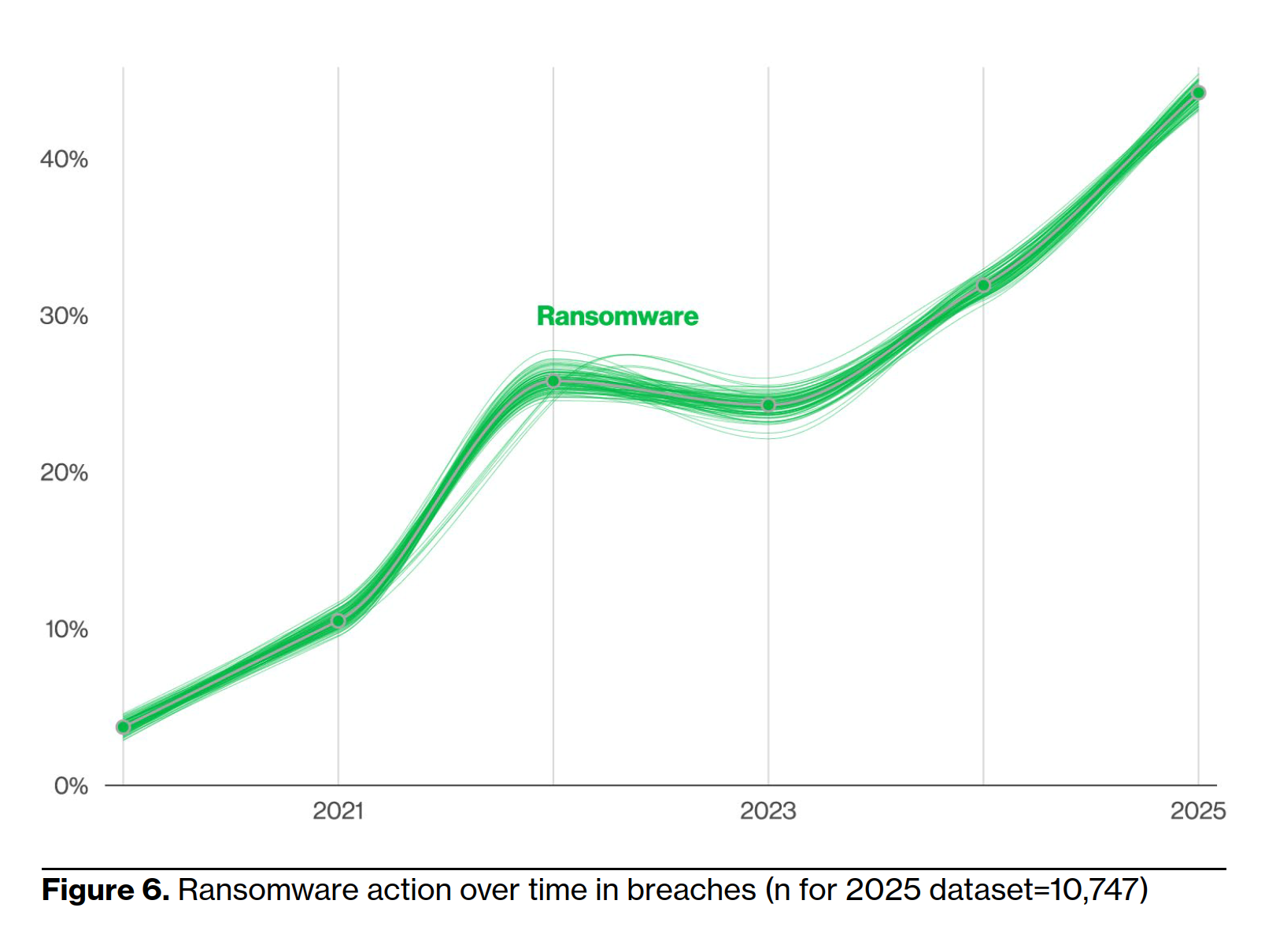
- Ransomware continues to be a menace, involved in 44% of breaches—a 37% increase from last year. However, the median ransom paid dropped to $115,000, and 64% of victims refused to pay.
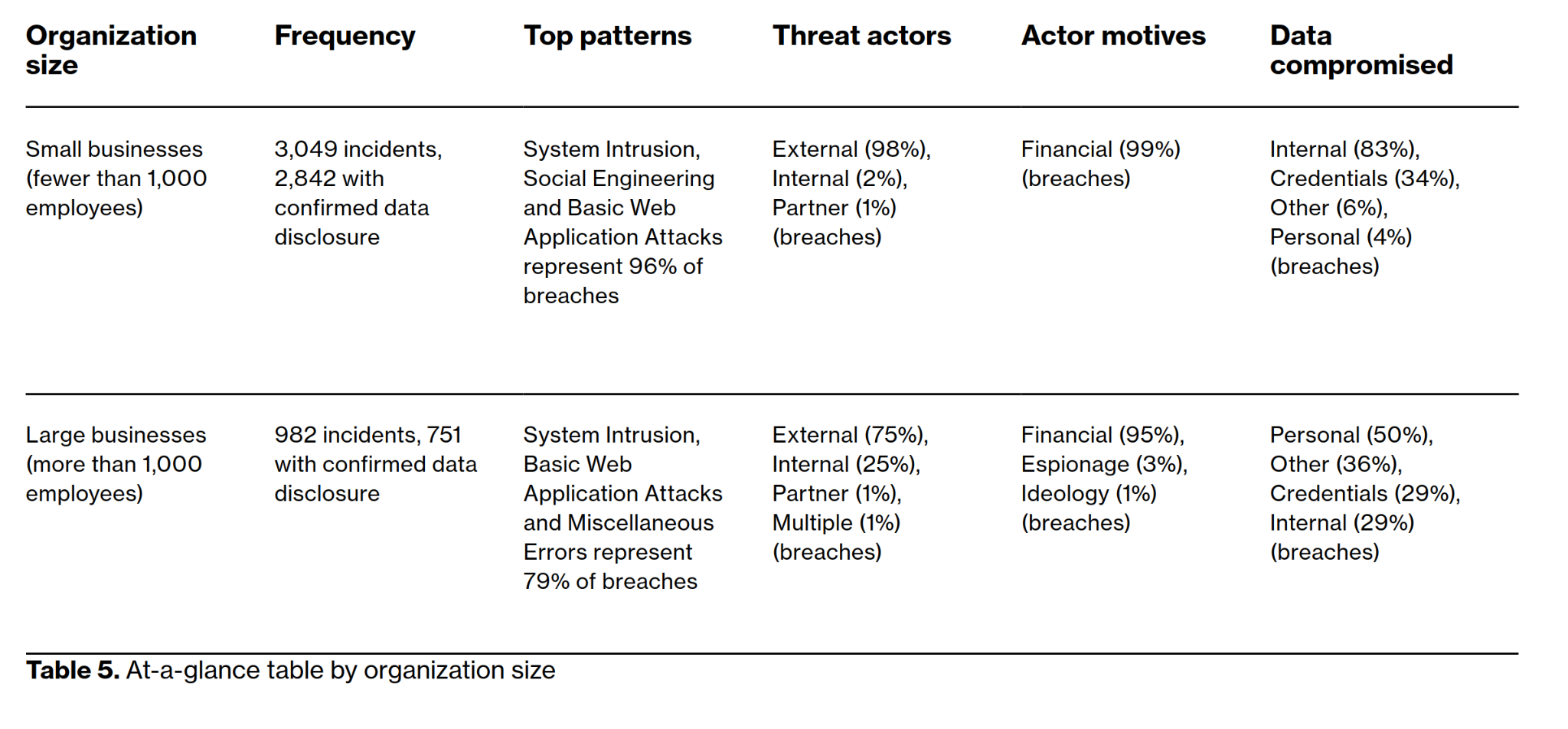
- Breaches for SMBs is mostly due to ransomware – 88% of SMB reported breaches.
- Third-party involvement in breaches doubled to 30%, making supply chain risk a screaming hot potato.
- Espionage-motivated breaches grew to 17%, often leveraging vulnerability exploitation.
- Generative AI misuse: Use of AI in malicious emails doubled, and 15% of employees are accessing GenAI services at work—sometimes unsafely.
- 54% of perimeter vulnerabilities were fully remediated in the past year. Great, right! NO – that means only a little more than half of them are protected.
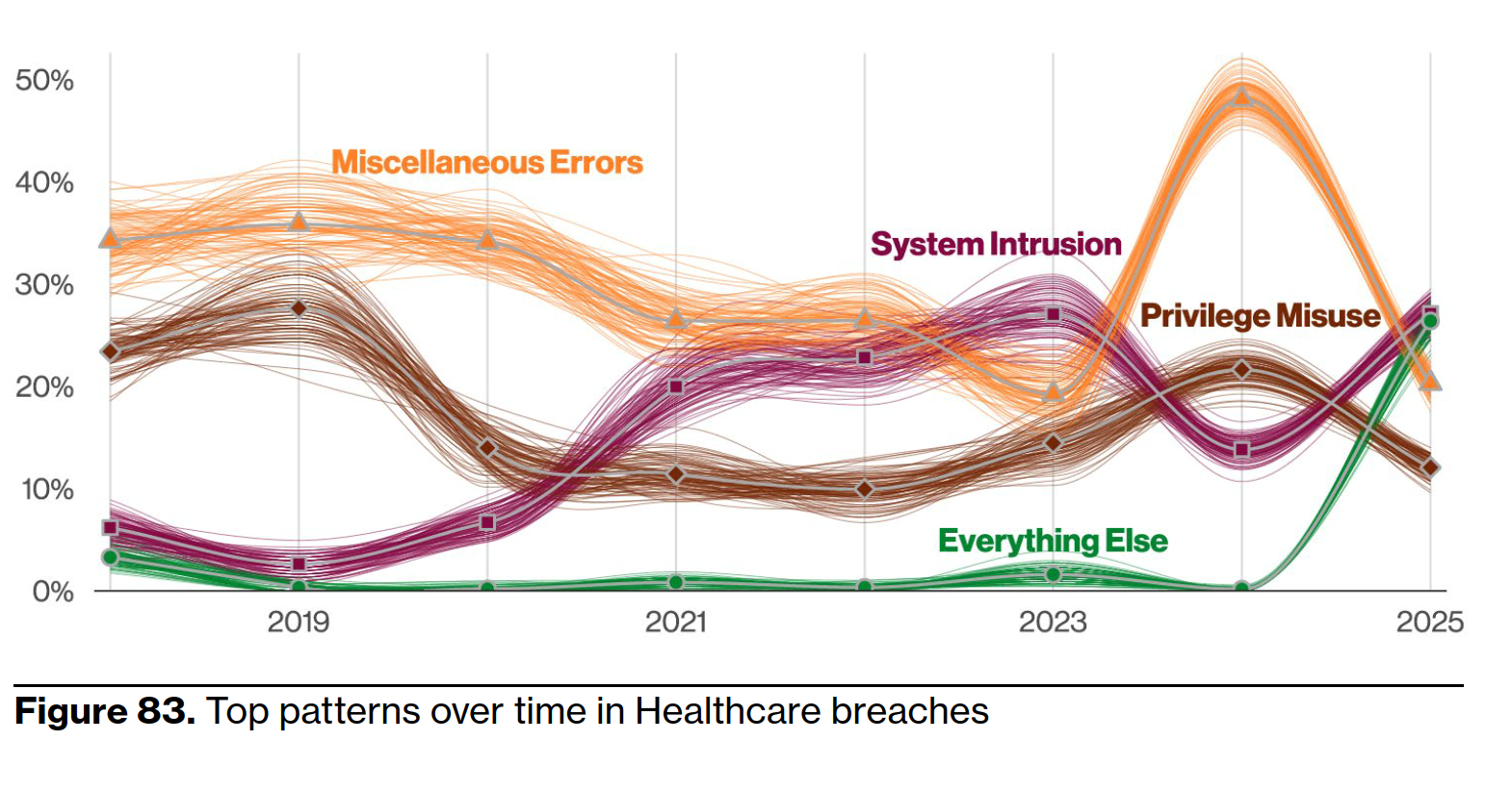
Healthcare-Specific Findings:
- Healthcare remains a prime target with 1,710 incidents and 1,542 confirmed breaches.
- Top patterns: System Intrusion (including ransomware) is now the leading cause of breaches, overtaking Miscellaneous Errors.
- Espionage motives in healthcare breaches increased to 16%, a concerning trend.
- Third-party breaches are a huge issue—radiology services, pharma firms, IT providers, and even pharmacies were hit.
- Notably, ransomware’s impact on healthcare is brutal due to urgent need for data access—forcing downtime and manual processes.
Size does not matter any more folks!
[46:48] Back when they first checked on small businesses in 2013 there was a difference in the threats and attacks happening. Today it is no longer the case. As they said in their opening to the section:This year, we decided to take another look and see how things currently stand. Let’s jump in to the results, but before we do (spoiler alert!), it’s mostly bad news for SMBs.
So, what did we learn from Mandiant and Verizon’s latest cybersecurity tell-alls? That ransomware is still partying hard, healthcare remains the hacker’s favorite VIP lounge, and small businesses need to stop pretending they’re wearing digital invisibility cloaks. From third-party chaos and cloud misconfigurations to dwell times that rival bad Airbnb guests, it’s all getting a bit too real out there. Whether you’re a solo practice or a sprawling health system, the message is loud and clear: hope isn’t a strategy, ignoring your firewall updates isn’t cute, and attackers are getting way too creative for comfort. Time to audit, assess, and armor up before you make next year’s breach list.
Remember to follow us and share us on your favorite social media site. Rate us on your podcasting apps, we need your help to keep spreading the word. As always, send in your questions and ideas!
HIPAA is not about compliance,
it’s about patient care.TM
Special thanks to our sponsors Security First IT and Kardon.


