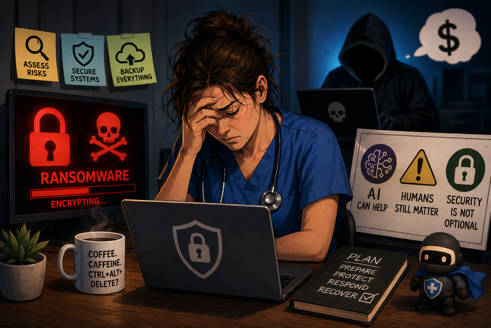
If you’ve ever wondered what happens when ransomware, bad decisions, cyber insurance confusion, and TikTok tech advice all collide in one spectacular dumpster fire… this episode is for you. The conversation dives into four fresh OCR enforcement actions that all share one painfully common theme: nobody did a proper risk analysis until after everything caught on fire. Add in cybersecurity “professionals” secretly helping ransomware gangs and business owners trying to replace enterprise security tools with AI-generated software from TikTok, and you’ve got an episode that somehow manages to be both educational and deeply concerning.
In this episode:
Vibecoding, Breaches, and Regret – Ep 559
Today’s Episode is brought to you by:
Kardon
and
HIPAA for MSPs with Security First IT
Subscribe on Apple Podcast. Share us on Social Media. Rate us wherever you find the opportunity.
Great idea! Share Help Me With HIPAA with one person this week!
Learn about offerings from the Kardon Club
and HIPAA for MSPs!
Thanks to our donors. We appreciate your support!
If you would like to donate to the cause you can do that at HelpMeWithHIPAA.com
Like us and leave a review on our Facebook page: www.Facebook.com/HelpMeWithHIPAA
When you see a couple of numbers on the left side of the text below click that and go directly to that part of the audio. Get the best of both worlds from the show notes to the audio and back!
Vibecoding, Breaches, and Regret
[01:15]OCR Resolution Agreements with Four Ransomware Investigations
Ransomware is malicious software that blocks access to data—typically by encrypting it with a key known only to the attacker—until a ransom is paid. The resolutions announced mark 19 completed investigations from ransomware breaches and 13 completed investigations in OCR’s Risk Analysis Initiative.
The Risk Analysis provision requires regulated organizations (covered entities and business associates) to conduct an accurate and thorough assessment of the potential risks and vulnerabilities to the confidentiality, integrity, and availability of ePHI held by those organizations.
“Hacking and ransomware are the most frequent type of large breach reported to OCR,” said OCR Director Paula M. Stannard. “Proactively implementing the HIPAA Security Rule before a breach or an OCR investigation not only is the law but also is a regulated entity’s best opportunity to prevent or mitigate the harmful effects of a successful cyberattack.”
The settlements follow investigations into separate ransomware breaches that collectively affected over 427,000 individuals and involved the exposure of unsecured ePHI.
Under the settlements, the regulated entities have agreed to implement corrective action plans subject to OCR monitoring for two years and paid a total of $1,165,000 to OCR.
Today’s announcement covers settlements with the following regulated entities.
- [11:04] Regional Women’s Health Group, LLC (“RWHG”), doing business as Axia Women’s Health, is a network of women’s health care providers in New Jersey, Pennsylvania, Ohio, Indiana, and Kentucky. The ransomware breach affected 37,989 individuals. The types of ePHI affected by the breach included names, addresses, dates of birth, SSNs, driver’s license numbers, diagnoses or conditions, lab results, and medications. RWHG reported in December 2020 that an unauthorized third-party gained access to its IT network and potentially exfiltrated data from RWHG’s electronic medical record database housing patient ePHI. OCR’s investigation found that RWHG failed to conduct an accurate and thorough risk analysis to determine the potential risks and vulnerabilities to the confidentiality, integrity, and availability of its ePHI. In addition to committing to corrective actions, RWHG paid $320,000 to OCR.
Potential exfiltration. Failed SRA. 2 year CAP
- [12:19] Assured Imaging Affiliated Covered Entities (“Assured Imaging”) is a medical imaging and screening service provider with corporate headquarters in Arizona and California. The ransomware breach affected 244,813 individuals. The types of affected ePHI included patient names, addresses, dates of birth, diagnosis and conditions, lab results, medications, and treatment information. Assured Imaging reported in May 2020 that a server on its network was infected with ransomware. OCR’s investigation determined that Assured Imaging had impermissibly disclosed PHI, failed to conduct an accurate and thorough risk analysis to determine the potential risks and vulnerabilities to the confidentiality, integrity, and availability of its ePHI, and failed to timely notify affected individuals of the breach. In addition to committing to corrective actions, Assured Imaging paid $375,000 to OCR.
Ransomware with exfiltration. Failed to do the SRA and failed to timely notify after the breach. 2 year CAP
“Assured has never conducted a compliant Security Rule risk analysis.”
- [14:34] Consociate, Inc., doing business as Consociate Health (“Consociate”) is a third-party administrator of employee-sponsored benefit programs that provides health plan administration, plan analytics and consulting services to HIPAA covered entities as a business associate. Approximately 136,539 individuals were affected by the ransomware breach. Affected ePHI included names, addresses, dates of birth, driver’s license numbers, SSNs, credit card/bank account numbers, and diagnoses or conditions. Consociate reported in November and December 2021 that some of its information systems had been encrypted in a ransomware attack. Consociate subsequently learned that, after a successful phishing attack in July 2020, the threat actor gained access to a server that held ePHI. OCR’s investigation determined that Consociate had failed to conduct an accurate and thorough risk analysis to determine the potential risks and vulnerabilities to the confidentiality, integrity, and availability of ePHI held by Consociate. In addition to committing to corrective actions, Consociate paid $225,000 to OCR.
Full encryption ransomware attack. No SRA. 2 year CAP
“Consociate subsequently learned that its information systems had been compromised six months earlier following a successful phishing attack, and that the threat actor had since undertaken significant malicious activity against Consociate’s network environment, culminating in the ransomware attack.”
- [17:46] Star Group, L.P. Health Benefits Plan (“SG Health Plan”) is the self-funded employee benefits plan of a Connecticut-based energy provider. About 9,316 individuals were affected by the ransomware breach. Affected ePHI included names, addresses, dates of birth, SSNs, and health insurance information, such as member identification numbers, claims data, and benefit selection information. SG Health Plan reported in October 2021 that an unauthorized actor deployed ransomware on SG Health Plan’s information system and exfiltrated PHI. OCR’s investigation determined that SG Health Plan had impermissibly disclosed PHI and failed to conduct an accurate and thorough risk analysis to determine the potential risks and vulnerabilities to the confidentiality, integrity, and availability of its ePHI. In addition to committing to corrective actions, SG Health Plan paid $245,000 to OCR.
Ransomware attack. No SRA. 2 year CAP
[25:26]PSA – China stops Manus AI acquisition by Meta (facebook)
For those who are using Manus AI, time to break out the SRA documentation and run it through again. Using an AI tool from China… probably not a good idea, especially in healthcare.
Playing both sides
We discussed this one before when they caught them.
Ransomware Negotiator Secretly Worked Both Sides—then Joined the Conspiracy
Guys from FL, GA and TX
FL on just plead guilty will be sentenced in July. Other two sentenced this week:
“He [Martino] is scheduled to be sentenced on July 9 and faces a maximum penalty of 20 years in prison. Martin and Goldberg separately entered guilty pleas to the same charge in December 2025. Martin and Goldberg are scheduled to be sentenced on April 30 and each face a maximum penalty of 20 years in prison.”
“All three men worked in the cybersecurity industry and leveraged their knowledge and skills to commit these crimes. After successfully extorting one victim for approximately $1.2 million in Bitcoin, the men split their share of the ransom three ways and laundered the funds through various means.”
[32:45]VIBE coding is not there to replace AV
How do you deal with “vibecoders”
However I just left a meeting with a small client of ours that wants to drop our EDR and backup because his son is a vibecoder and he has been seeing TikToks on how to vibecode his own AV and other apps. His intention is to completely replace most of our services by the end of 2026. He does however want to be able to call us if there were any other issues like hardware and “stuff that AI cannot replace yet”.
I tried explaining that it is a slippery slope when you decide to step away from products that are tried and true and jump to stuff of which you don’t know if it actually does anything. But in all honestly I do not mind losing this client at all.
I had a really hard time not laughing in his face after his son showed me the TikTok of the guy that “vibecoded” his own AV. “Look it says it scanned all the files on his computer”. He obviously could not answer anything about how or what the AV actually did but “it’s run by AI”…
I explained that if he wants to go this route it’s absolutely up to him but we won’t be along for the journey. He was going to think about it but he ended the meeting with a “I just feel companies like yours need to understand you are already replaced”.
No – just say no to this idea. Please!
At the end of the day, the biggest cybersecurity disasters usually don’t start with elite hackers in dark hoodies — they start with skipped risk analyses, ignored warnings, overconfidence, and somebody saying, “We’ll deal with that later.” This episode is a reminder that AI, automation, and shiny new tech can absolutely help businesses move faster, but speed without guardrails is how you end up careening off the digital cliff while wondering why your backup strategy came from TikTok.
Remember to follow us and share us on your favorite social media site. Rate us on your podcasting apps, we need your help to keep spreading the word. As always, send in your questions and ideas!
HIPAA is not about compliance,
it’s about patient care.TM
Special thanks to our sponsors Security First IT and Kardon.


