Sometimes the biggest threat to your data isn’t the hackers, it’s what happens after the hackers leave. In this episode, we dive into a jaw-dropping case where 15 million patient records were exposed… and then quietly swept under the rug like a mess nobody wanted to deal with. Spoiler alert: ignoring a breach doesn’t make it disappear, it just makes the consequences louder later. If you’ve ever wondered how bad things can get when vendors drop the ball, this one’s a wild ride.
In this episode:
15 Million Record Cover-Up – Ep 554
Today’s Episode is brought to you by:
Kardon
and
HIPAA for MSPs with Security First IT
Subscribe on Apple Podcast. Share us on Social Media. Rate us wherever you find the opportunity.
Great idea! Share Help Me With HIPAA with one person this week!
Learn about offerings from the Kardon Club
and HIPAA for MSPs!
Thanks to our donors. We appreciate your support!
If you would like to donate to the cause you can do that at HelpMeWithHIPAA.com
Like us and leave a review on our Facebook page: www.Facebook.com/HelpMeWithHIPAA
When you see a couple of numbers on the left side of the text below click that and go directly to that part of the audio. Get the best of both worlds from the show notes to the audio and back!
CISA Alert
[01:08]CISA Urges Endpoint Management System Hardening After Cyberattack Against US Organization
To defend against similar malicious cyber activity, CISA urges organizations to harden endpoint management system configurations using the recommendations and resources provided in this alert. CISA is conducting enhanced coordination with federal partners, including the Federal Bureau of Investigation (FBI), to identify additional threats and determine mitigation actions
- Use principles of least privilege when designing administrative roles.
- Enforce phishing-resistant multi-factor authentication (MFA) and privileged access hygiene.
- Configure access policies to require Multi Admin Approval in Microsoft Intune
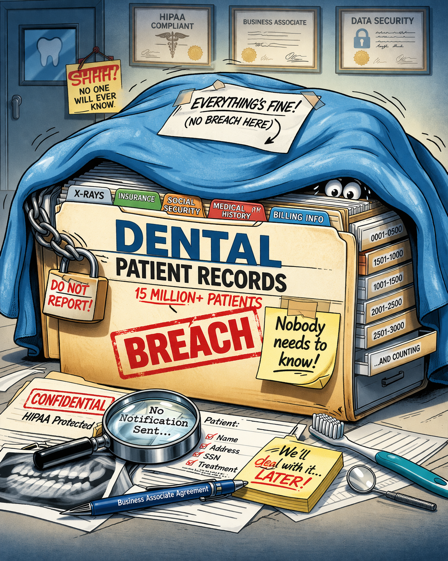
15 Million Record Cover-Up
[02:30] What really happened was…..OCR’s 12th Enforcement Action in OCR’s Risk Analysis Initiative
If a breach happens at a business associate and they don’t tell anyone – did it really happen?
MMG Fusion, LLC OCR Settlement Agreement
- A Maryland software company
- CAP for three years and paid $10,000 to OCR
- 15 million patient records exposed… and no one was told
- Not a hospital or insurer, but a software vendor sitting behind the scenes
- And the breach only comes to light after a complaint to OCR
Who is MMG Fusion
- Marketing and patient communication platform for dental practices
- Business associate handling PHI directly on behalf of covered entities
- Reminder that vendors are often the weakest link in the chain
- December 2020 cyberattack with unauthorized system access
- Data exposed included names, contact info, DOB, and appointment details
- PHI later found posted on the dark web
The “cover-up” angle
- Breach occurred in 2020 but OCR investigation didn’t start until 2023
- Triggered by a complaint, not self-reporting
- Failure to notify covered entities as required under HIPAA
- Translation: your vendor knew… but didn’t tell you
Whistleblower / complaint angle
- OCR explicitly states investigation began after receiving a complaint
- Raises the question:
- internal employee?
- affected provider?
- security researcher?
- Reinforces that regulators are often tipped off, not discovering breaches on their own
“When a breach occurs, business associates must notify affected covered entities without unreasonable delay and within 60 calendar days of discovery,” said OCR Director, Paula M. Stannard. “This timeliness is crucial for a covered entity to meet its own breach notification obligations, such as timely notification to HHS and to individuals. As hacking becomes more ubiquitous, HIPAA Security Rule requirements, such as the need to have an accurate and thorough HIPAA risk analysis, are imperative for strengthening cybersecurity before a breach occurs.”
The classic HIPAA failure: no risk analysis
- OCR found failure to conduct an “accurate and thorough” risk analysis
- This is now a recurring theme in OCR enforcement (Risk Analysis Initiative)
- It’s like skipping a fire inspection and acting surprised when the building burns down
Multiple violations stacked together
- Impermissible disclosure of PHI (15 million individuals)
- No risk analysis
- No breach notification to covered entities
- This is not one mistake… it’s a system-wide failure
The penalty… wait, only $10,000?
- Settlement amount: $10,000
- OCR explicitly considered financial condition of the company
Under the corrective action plan, MMG has committed to take steps to ensure compliance with the HIPAA Rules and protect the security of ePHI, including:
- Conduct an accurate and thorough risk analysis to determine the potential risks and vulnerabilities to the confidentiality, integrity, and availability of its ePHI;
- Develop and implement a risk management plan to address and mitigate security risks and vulnerabilities identified in its risk analysis;
- Develop, maintain, and revise, as necessary, written policies and procedures in accordance with the Privacy and Security Rules;
- Ensure that all workforce members are trained with respect to Privacy and Security Rule policies and procedures; and
- Conduct a breach risk assessment of the December 2020 cyber-attack and, to the extent possible, provide affected covered entities with an accurate notice of the beach incident.
- Your vendors can create your breach liability
- If they don’t tell you about a breach, you still own the regulatory fallout
- Risk analysis is not optional paperwork, it’s the foundation of everything
- And if something goes wrong… someone might tell OCR for you
So what’s the moral of this chaotic compliance tale? You can’t outsource responsibility, you can’t hide a breach forever, and you definitely can’t assume someone else has things “handled.” Whether it’s your vendor, your IT team, or your internal processes, trust without verification is a risky game. And as this case shows, the longer you wait to face the truth, the more expensive—and public—it becomes. Turns out, the cover-up is almost always worse than the breach.
Remember to follow us and share us on your favorite social media site. Rate us on your podcasting apps, we need your help to keep spreading the word. As always, send in your questions and ideas!
HIPAA is not about compliance,
it’s about patient care.TM
Special thanks to our sponsors Security First IT and Kardon.


