 Securing your business is not always the easiest thing to do nor the cheapest. Today we will review a Cisco study on small and medium sized businesses and their security best bets. In other words, the things that you can do that will help you to most likely attain success and get you the most bang for your buck.
Securing your business is not always the easiest thing to do nor the cheapest. Today we will review a Cisco study on small and medium sized businesses and their security best bets. In other words, the things that you can do that will help you to most likely attain success and get you the most bang for your buck.
In this episode:
SMB Security Best Bets – Ep 311
Today’s Episode is brought to you by:
Kardon
and
HIPAA for MSPs with Security First IT
Subscribe on Apple Podcast. Share us on Social Media. Rate us wherever you find the opportunity.
The HIPAA Boot Camp
Virtual Edition Aug 17-19, 2021
Great idea! Share Help Me With HIPAA with one person this week!
Thanks to our donors. We appreciate your support!
If you would like to donate to the cause you can do that at HelpMeWithHIPAA.com
Like us and leave a review on our Facebook page: www.Facebook.com/HelpMeWithHIPAA
If you see a couple of numbers on the left side you can click that and go directly to that part of the audio. Get the best of both worlds from the show notes to the audio and back!
HIPAA Say What!?!
We received a listener question about Ep 303 – HIPAA Compliant Apps.
We talked about Zoom in that episode. Just like many other services they have versions that meet HIPAA compliance standards and they will sign a BAA for those. The question was: How do I know if I have one of those or not?
First, do you need a BAA with Zoom? Just because you are a BA or a CE it doesn’t mean that every application you use has to be HIPAA compliant. Only applications that involve PHI have to be HIPAA compliant.
If you think you have the HIPAA version but don’t have a BAA, then you don’t have what you need for HIPAA even if you have the “right” version. Here is a link to the current versions of Zoom as of right now:
To get the version that comes with a BAA, start by selecting “Healthcare” in the “View plans for” dropdown. That will narrow the options to and gives you prompts for the Healthcare version that includes signing a BAA.
New State Privacy Laws
[07:47] Due to the swarm of cyber attacks, there has been a lot of privacy legislation activity within the states. Which makes the argument for the need for a federal privacy law more intense. Several states have recently passed “CCPA-like” privacy laws, including Connecticut, Colorado, New York and Nevada. See the details in the link below.Status Of Proposed CCPA-Like State Privacy Legislation As Of May 24, 2021
So, get ready to learn about state privacy laws. Several of these laws kick in around July.
Connecticut’s new law goes into saying health care information is included, but as far as all of the other requirements, you can meet them by showing that you comply with HIPAA and HITECH. That approach is very interesting because it scoops up everybody that has medical information that HIPAA doesn’t apply to.
If you haven’t looked yet at the states that apply to your business, you should check them out on the JDSUPRA site. Your lawyer could also help you with your state laws, too. Keep in mind that if you have clients or consumers in multiple states, you have to deal with each of those states’ laws.
SMB Security Best Bets
[13:07] Today we are going to look at the security outcomes study published by Cisco in April 2021. This study helps to identify the key factors that can help small and medium sized businesses (SMB) design a successful security plan, even with limited resources.2021 Security Outcomes Study for Small to Midsize Businesses (SMBs)
The study identified the top security success differentiators for SMB compared to large business and enterprises. We are mainly focused on the SMBs, though.
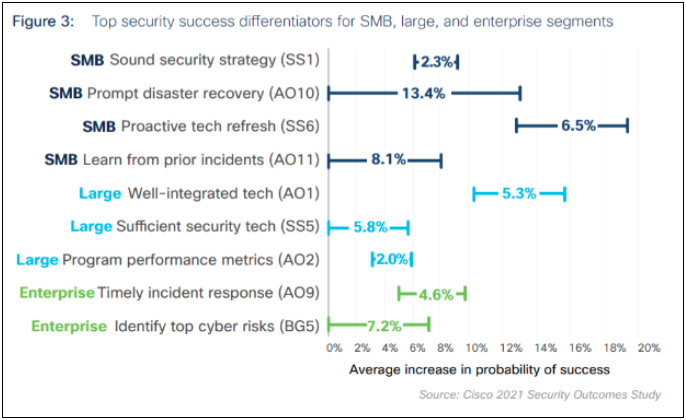
So, the top four differentiators for SMBs are:
- Sound security strategy – this basically means to think it through and have a plan.
- Prompt disaster recovery – the only way you can do this is have a plan and test your plan.
- Proactive tech refresh – don’t wait til computers, servers or other equipment dies; work with IT to create a plan to replace equipment on a regular basis.
- Learn from prior incidents – learn from your mistakes and the mistakes of others. As we’ve mentioned several times, pay attention to the news and specifically the OCR settlements. You can learn a lot from other people’s mistakes and what OCR expects of you.
In the figure above, the starting point for each line marks the average success rate across all study participants. The endpoint of the line indicates how much more impact that factor has on success rates among small businesses.
[22:15] The outcomes that this study talked about where technology and security matters include enabling small business (keeping up to date with business, confidence that systems are secure, everyone is participating, having a culture of security, etc), managing risk and operating efficiently. So, what are the security practices that have the highest probability of success in those areas?Enabling Small Business
Let’s look at enabling the business first. You can see from the chart below that the factors the report identifies to have a fully enabled business managing security include keeping up with the business, gaining executive confidence, obtaining peer buy-in and creating a security culture. Three of those have a statistically significant increase in likelihood just by having the pro-active tech refresh. It’s also worth pointing out that people are more likely to obtain peer buy-in if you have sufficient security staff, manage your vendor security, IT and security work together and they understand security and the business and how it matters.
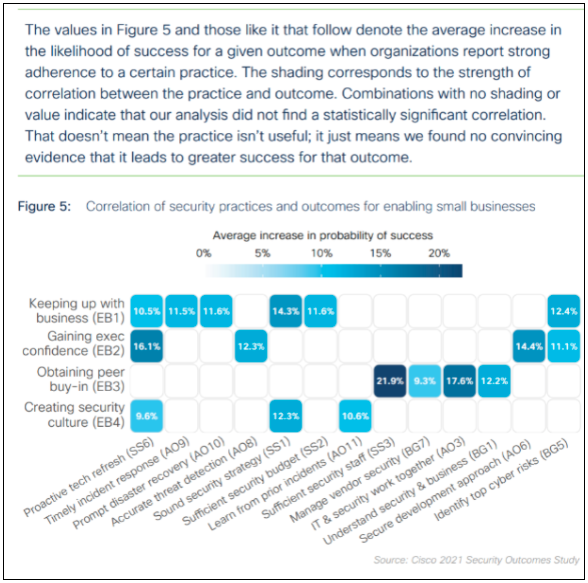
Also notice that the study results separate security from IT. We’ve mentioned before that IT and security should have their own separate line item in your budgets. Buying 15 new computers for the office staff (IT) is not the same as spending money on security or cybersecurity to protect the business and your networks.
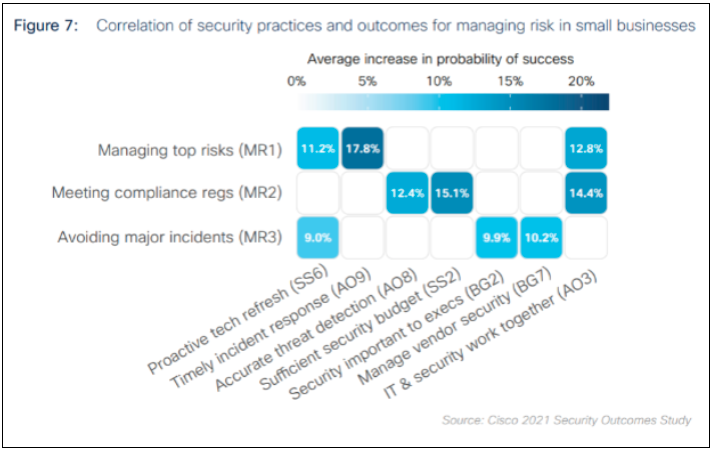
Managing Risk in Small Businesses
[27:48] The Cisco study breaks down managing risks into three categories:- Managing the top risks – Sound familiar? Maybe the top5 threats healthcare should worry about? 405d HICP, maybe?
- Meeting compliance regulations – Remember, security is not compliance and compliance is not security. You have to worry about both.
- Avoiding major incidents – Having ways to detect something happening and mitigate it before it gets out of control. A major incident is just a minor incident that got out of control.
You see in the chart below that again one of the best ways to manage the top risks and avoid major incidents is the proactive tech refresh and make sure IT & security work together. And the number one way across all of these to improve managing risk is timely incident response… meaning it is important to have a written, thorough and practiced incident response plan.
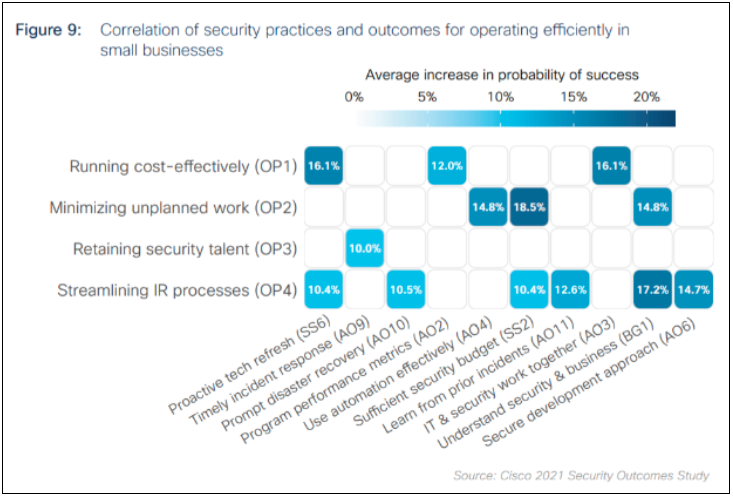
Operating Efficiently in Small Business
[36:52] There are four categories involved for a business to run efficiently, according to this study:- Running cost- effectively
- Minimizing unplanned work
- Retaining security talent
- Streamlining IT processes
The results show to be efficient overall, you need to understand security and business and how they interact. And after that, having a sufficient security budget and then proactive tech refresh make the biggest impact to having an efficient business.
Also, things like having IT and security working together is a key element of making a business run cost effectively. And it’s interesting to note that the only thing that seemed to make a significant statistical difference in the probability of success in retaining security talent was to have a timely incident response. And look at all the factors in the chart to point to factors influencing a streamlined IR process. Wow.
Many people think that their incident response plan is to call IT. That’s wrong. IT is likely to be a part of your incident response plan, but they can do everything you need to recover from a disaster or other incident. IT can certainly help you create a plan, but the should not BE your plan.
This was a very interesting study. Although Cisco compiled the results for this study, they used different companies to do the various surveys and others to do the analytics. It’s a pretty scientific study. So, consider using this report in your planning sessions and presentations to leadership. These kinds of analysis are going to be more important as we move forward.
There are a lot of moving parts to make a business run efficiently and managing risks. Your security practices can have a significant impact on your business. And IT teams don’t always have the expertise that is needed to secure your networks. Understand where the line is between IT support and properly securing your networks from outside threats. You just might need to have some sort of co-managed IT services where you have an IT team and a separate security team. Something to think about.
Remember to follow us and share us on your favorite social media site. Rate us on your podcasting apps, we need your help to keep spreading the word. As always, send in your questions and ideas!
HIPAA is not about compliance,
it’s about patient care.TM
Special thanks to our sponsors Security First IT and Kardon.


