It’s a story straight out of a blockbuster movie – an elite team of FBI agents infiltrating an underground network to thwart an international crime syndicate, saving over $130 million in ransom demands. Using their expert skills, the FBI agents were able to infiltrate the Hive network without detection and shut them down… at least for now.
In this episode:
Inside Hive – Ep 393
Today’s Episode is brought to you by:
Kardon
and
HIPAA for MSPs with Security First IT
Subscribe on Apple Podcast. Share us on Social Media. Rate us wherever you find the opportunity.
The Privacy and Security Boot Camp
3.5 day In Person Event
Mar 12, 13, 14 and 15, 2023
PriSecBootCamp.com
Great idea! Share Help Me With HIPAA with one person this week!
Learn about offerings from the Kardon Club
and HIPAA for MSPs!
Thanks to our donors. We appreciate your support!
If you would like to donate to the cause you can do that at HelpMeWithHIPAA.com
Like us and leave a review on our Facebook page: www.Facebook.com/HelpMeWithHIPAA
If you see a couple of numbers on the left side you can click that and go directly to that part of the audio. Get the best of both worlds from the show notes to the audio and back!
Thanks to our donors.
HIPAA Say What!?!
[05:19] Listener question!From Mary:
Love your Podcast! I am working on an audit of data within the environment for HIPAA data. I noticed that this company in PA has the FMLA forms for employees in a secure but not HIPAA secure drive. I am in a discussion with HR. I believe this contains HIPAA data and needs to be at the top security level and logging turned on for access. Thoughts?
It depends.
Inside the Hive Takedown
[13:08] U.S. Department of Justice Disrupts Hive Ransomware Variant | OPAThe big splash news:
FBI Covertly Infiltrated Hive Network, Thwarting Over $130 Million in Ransom Demands
The Justice Department announced today its months-long disruption campaign against the Hive ransomware group that has targeted more than 1,500 victims in over 80 countries around the world, including hospitals, school districts, financial firms, and critical infrastructure.
Since late July 2022, the FBI has penetrated Hive’s computer networks, captured its decryption keys, and offered them to victims worldwide, preventing victims from having to pay $130 million in ransom demanded. Since infiltrating Hive’s network in July 2022, the FBI has provided over 300 decryption keys to Hive victims who were under attack. In addition, the FBI distributed over 1,000 additional decryption keys to previous Hive victims. Finally, the department announced today that, in coordination with German law enforcement (the German Federal Criminal Police and Reutlingen Police Headquarters-CID Esslingen) and the Netherlands National High Tech Crime Unit, it has seized control of the servers and websites that Hive uses to communicate with its members, disrupting Hive’s ability to attack and extort victims.
They infiltrated the networks and hacked the bad guys for a pleasant change in the fight against cyber criminals.
Pretty sneaky plan to break into the network and as they were attacking victims the DOJ and their international partners would get the decryption key and secretly give it to the victims, so they didn’t have to pay. They stopped 300 victims from having to pay $130m in demands. Plus, gave out keys to over 1,000 previous victims.
The story is a very nice one to share for a change.
What’s in the details?
[17:44] Warrant AffidavitThe real juicy stuff is in the details – as always. The unsealed documents include the affidavit of the FBI Special Agent involved in the infiltration of the criminal enterprise. There are 24 pages in the complete document, but the best part starts around page 11.
The following statements were part of that section that we found interesting.
How about a “technology company in New Jersey”
The operation also confirmed that the operation was consistently hitting victims.
If you really want to get into some of the nerdy details it does explain a bit about how they hide their servers on Tor Infrastructure. What is important to note is the number of servers they had operational to manage their RaaS operations.

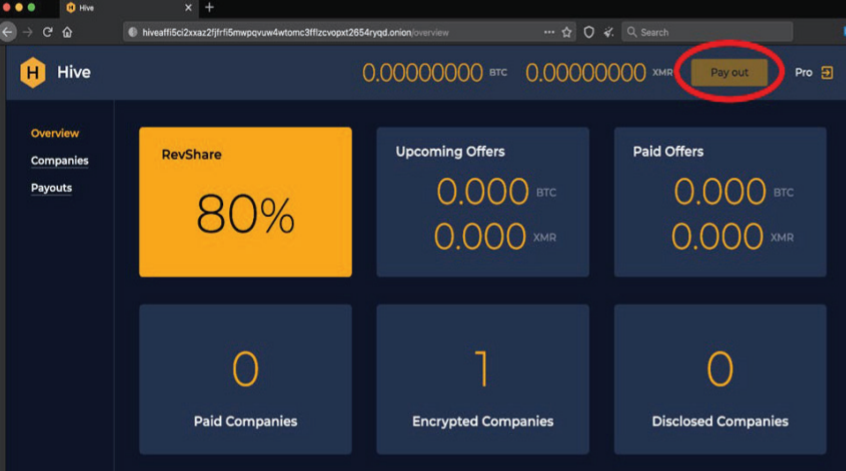
It was really nice that they had a screenshot of the Login page to show how deeply they were in there. The affiliate dashboard does make it clear they are a full service RaaS operation.
So they have the “Sales Department” for victims to access. Affiliate panels for their partners in crime. The Admin for Hive administrators and then the very public Leak Site.
They were able to seize all the current servers and even found that they leased servers for the network with a US hosting provider. There were a couple of dedicated servers and one VPS in a LA data center. There were other dedicated servers located in the Netherlands as well. Turns out they were redundant servers.
Once they got to the victim database they spent 6 months trying to get keys to victims as soon as possible. They say something within hours of the attack.
But, the real catch in the trap was information about their communications with others, malware file hashes and 250 affiliates along with the victim info.
How did they get in?
[30:14] According CISA’s previous alerts on HIVE they knew that part fairly well:This team has been at it a while. HHS HC3 published a brief on them in Oct 2021
Will they be out of production for long? Probably not but this is a good start.
Some good news for a change. It’s great that the FBI was able to shut down the Hive network. The bad news is that they have redundancy, so they likely won’t be out of production for long. Bottom line… PriSec isn’t going away. It’s going to get harder and more important to keep up with all of the threats in the cyber world and to secure our networks against attacks.
Remember to follow us and share us on your favorite social media site. Rate us on your podcasting apps, we need your help to keep spreading the word. As always, send in your questions and ideas!
HIPAA is not about compliance,
it’s about patient care.TM
Special thanks to our sponsors Security First IT and Kardon.