
If you are a regular listener of the podcast, you know how Donna loves to “HIPAA-geek out” over the HIPAA Summit each year. Things are no different this year as the virtual conference stretched 3 full days and another half day. Needless to say Donna got TONS of information to share – so much so we won’t be able to fit it all in this one podcast. So, let’s get to Part 1 of the HIPAA Summit 2021.
In this episode:
HIPAA Summit 2021 News Part 1 – Ep 298
Today’s Episode is brought to you by:
Kardon
and
HIPAA for MSPs with Security First IT
Subscribe on Apple Podcast. Share us on Social Media. Rate us wherever you find the opportunity.
The HIPAA Boot Camp
Virtual Edition Aug 17-19, 2021
Great idea! Share Help Me With HIPAA with one person this week!
Thanks to our donors. We appreciate your support!
If you would like to donate to the cause you can do that at HelpMeWithHIPAA.com
Like us and leave a review on our Facebook page: www.Facebook.com/HelpMeWithHIPAA
If you see a couple of numbers on the left side you can click that and go directly to that part of the audio. Get the best of both worlds from the show notes to the audio and back!
HIPAA Say What!?!
[04:59] One listener question came in just before we recorded last week. Another came in this week.Someone once got in trouble for us mentioning their name when addressing their question. So we will no longer do a “shout out” using someone’s full name and thank them for listening directly, just in case. But thanks for listening and reaching out!
Name: Jennifer
I’ve recently begun listening to your podcasts and find them so helpful. I am a new office manager of less than a year, trying to improve HIPAA compliance program. Would a company like Payspan who we receive payments from be considered a business associate? The insurance company I believe contracts them to provide payment info.
Depending on the services they provide they may be a BA. But, if the insurance company contracts with them they would not be YOUR BA, that would fall to the insurance company. The BAA connects the service provider to a company that hires them to provide a service.
[09:17]
Name: John
Is there a specific HIPAA rule regarding Patched or maybe a fine levied against someone for unpatched computers and window 7? I am dealing with an IT guy insisting that this is not addressed in HIPAA.
We do love this argument – NOT! This is the first time IT experts show us they are not HIPAA experts. Here is a link to a 2014 – yes 2014 – OCR resolution agreement that specifically addresses this.
BULLETIN: HIPAA Settlement Underscores the Vulnerability of Unpatched and Unsupported Software
Anchorage Community Mental Health Services, Inc SETTLEMENT AGREEMENT
Below is the OCR director’s quote from the bulletin that goes with the settlement announcement. As we always like to point out, this tells us the specific points they are trying to make in this case.
“Successful HIPAA compliance requires a common sense approach to assessing and addressing the risks to ePHI on a regular basis,” said OCR Director Jocelyn Samuels. “This includes reviewing systems for unpatched vulnerabilities and unsupported software that can leave patient information susceptible to malware and other risks.”
There are others that mention unsupported software and unpatched vulnerabilities, but this one specifically calls it out. This particular case involved a non-profit organization and OCR took that into consideration. As for the particular mention in HIPAA, well, this is where many people get in this position. No, it does not use the term patches. The legal violations included the normal Risk Analysis and Risk Management vulnerabilities apply, but they point it out specifically. Here is the legal reference in the settlement:
From January 1, 2008, until March 29, 2012, ACMHS failed to implement technical security measures to guard against unauthorized access to e-PHI that is transmitted over an electronic communications network (See 45 C.F.R. § 164.312(e)) by failing to ensure that firewalls were in place with threat identification monitoring of inbound and outbound traffic and that information technology resources were both supported and regularly updated with available patches.
Unless your IT vendors read the settlement agreements or study the legal implications of the technology vs the letter of the law they will not know this reference.
HIPAA Summit 2021 News – Part 1
[24:52] So, let’s begin by pointing out that we will be doing a deep dive into the Stark Law and Anti-Kickback Statute changes, Recognized Security Practices and CISO recommendations in Part 2 of the HIPAA Summit 2021 discussion next week. And that discussion might even turn into a two part conversation itself.Information Blocking
April 5, 2021 is the official applicability date of the information blocking rules. But… it’s a mess, IMHO. Don’t get me wrong, there is value to this. But there is a lot of confusion and lack of understanding around information blocking. Plus, there isn’t even a defined method of enforcing it.
If you are a provider’s office and you are concerned about the April 5th date, here are the important things to know:
- You do not have to provide immediate access to records for all patients. This involves the concern over patients getting access to like lab reports before they’ve talked to their doctor to truly understand what the numbers and diagnostic information means. This should only be turned on if a patient specifically requests it right now. And even then, you have eight exceptions where you might not even let them have immediate access to something like a lab report.
- There’s no enforcement defined for information blocking. There’s no compliance rule required in it. So, it really is just documenting that you’re giving patients access to their records as quickly as possible… which is exactly what the patient’s right of access is all about. So get that tightened up.
- Realize the intent is coming and should be dealt with. In order to do that properly you have to understand the options that your vendors will give you. You may find that you don’t have the option to do some of these things because of what your vendors do and you might not have a way to deal with valid exceptions to this rule.
- The rule doesn’t apply to the technology piece when it comes to releasing information. It’s the actual content of the information that is the issue. The providers have the ultimate control over the content that is released to their patients.
- If you are a vendor, you need to put out a statement explaining what options are available and what you are allowing your clients to do to handle their patients. As a provider you need to contact your vendors and have them educate you on what your options are using their tool concerning information blocking.
- You can’t just say “No, you can’t have your records.” Not unless you can meet one of the exceptions. There is a security exception and a privacy exception. But it must be documented clearly. You can’t just say No. You have to prove No.
If you can try to turn a patient’s right to access their records around in five days or so, then you can say “we are doing all we can to get your records to you as soon as possible, short of our vendors giving us more tools so we can do it quicker.” There are three security exceptions you can use in this case to comply with the rule.
Right of Access Enforcement
[36:38] The Right of Access enforcement will continue. In fact the 17th case came out this week in the midst of the discussions at the HIPAA Summit. The cases involve improper fee being charged, improper access requests by patients, not providing the records that the provider was supposed to or not providing the complete records.CARES Act aligning CFR 42 Part 2 with HIPAA
[37:15] If you are in the business of providing drug abuse, mental health services or the like, there is a separate rule outside of HIPAA that you need to educate yourself on. Part of the CARES Act under COVID relief has aligned itself with HIPAA. So if you are in that world, make sure you read up on and understand those rules.OCR Presentations
[38:14] The OCR presentations included lots of pretty charts and graphs showing trends of breaches. From 2016 to 2018, OCR said they were receiving roughly one breach report per day that affected 500 or more individuals. By 2020 the number of breaches reported per year has almost doubled from that of 2016. And that’s just for the ones we know about.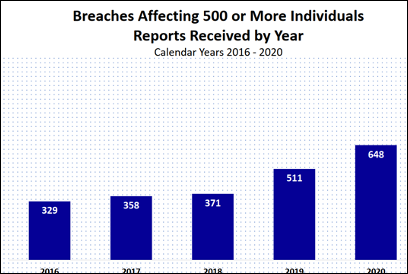
When looking at the period between September 23, 2009 and February 28, 2021of the reported breaches affecting 500 or more individuals, 37% of them were from hacking, 27% from unauthorized access or disclosure and 25% from theft. Theft used to be a much bigger number, but that’s been fixed mostly by encrypting devices. Our motto has always been, “if it moves, encrypt it.”
Now for the breaches reported in 2021, which includes breaches that occurred at the end of 2020, 71% were from hacking and 27% were from unauthorized access or disclosure. Big problem there.
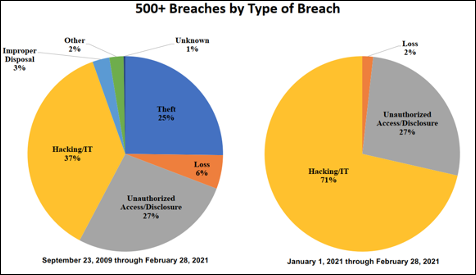
Most of the hacking/IT breaches are from hackers coming into the networks via the network server or email. OCR says it’s from email, phishing attacks, remote access that didn’t have multi-factor authentication and proper security.

When OCR investigates, they look at the state of the HIPAA compliance program. They listed the compliance issues that they see recur most often… shown in the chart below.
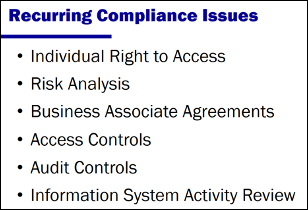
Violations of the individual right of access rule of providing patients with their medical records is a big problem. Not having a proper, thorough and accurate risk analysis continues to be a big issue. Then there’s Business Associate Agreement problems… not having them or having ones that are no longer effective or not up to date. Next is access controls which refers to remote access connections not being addressed properly. Then there’s audit controls where no one’s looking. This can involve improper use of usernames and passwords or multiple users using the same credentials or even bad password hygiene. Last, there’s information activity review where you are supposed to be reviewing everything. Just having the logs isn’t enough. The object is you are supposed to identify what needs to be protected, plan to protect it and then detect when things are attacking you. You can’t do that if you aren’t reviewing the activity logs.
[53:27] OCR published what they consider best practices of things they want you to do. For instance, if you have a reportable breach these are the things OCR will be asking of you when they do their investigation. Read through these… don’t they sound familiar?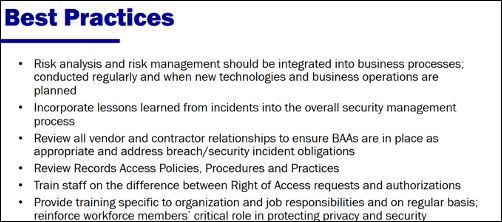
It would behoove everyone to take this list of best practices and make sure you are doing them. It could make a difference in OCR seeing that you are taking your compliance obligations and your job to protect your patients data seriously.
Wow, that was a lot and there’s still more to come in Part 2 (and possibly a Part 3) of the HIPAA Summit 2021 review from Donna. In our next podcast, we will cover what we’ve learned so far from the pandemic and what needs to change due to so many folks working from home. Plus we’ll find out about the Stark Law changes and more about Recognized Security Practices. So join us next week to continue this discussion on the HIPAA Summit 2021.
Remember to follow us and share us on your favorite social media site. Rate us on your podcasting apps, we need your help to keep spreading the word. As always, send in your questions and ideas!
HIPAA is not about compliance,
it’s about patient care.TM
Special thanks to our sponsors Security First IT and Kardon.


