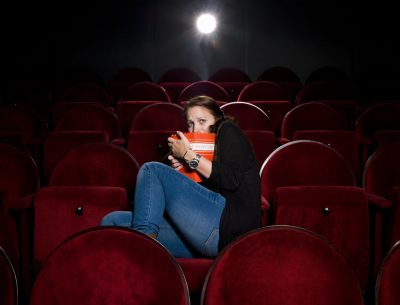
 If you are a fan of horror flicks you know the story. Even if you are not a fan you probably know the line from When A Stranger Calls: “the calls are coming from a phone inside the house”. That stuff happens in the opening. Personally, I have never made it through that part much less through the whole thing. Today we have a whole new horror flick to discuss: cyberattacks coming from inside the network. Maybe we should hold this until Halloween but who knows what will happen then, we need cover this because it is happening now.
If you are a fan of horror flicks you know the story. Even if you are not a fan you probably know the line from When A Stranger Calls: “the calls are coming from a phone inside the house”. That stuff happens in the opening. Personally, I have never made it through that part much less through the whole thing. Today we have a whole new horror flick to discuss: cyberattacks coming from inside the network. Maybe we should hold this until Halloween but who knows what will happen then, we need cover this because it is happening now.
In this episode:
Cyberattacks coming from inside the network – Ep 258
–
The HIPAA Boot Camp
2020 COVID Session Dates
August 18, 19, 20
Online Version!!
For info go to TheHIPAABootCamp.com
[button link=”https://helpmewithhipaa.com/hbc” type=”big” center=”yes” newwindow=”yes”] Registration Form[/button]
Share Help Me With HIPAA with one person this week!
Thanks to our donors. We appreciate your support!
If you would like to donate to the cause you can do that at HelpMeWithHIPAA.com.
Like us and leave a review on our Facebook page: www.Facebook.com/HelpMeWithHIPAA
Before we get started we must share an email we received this week from a regular listener George (can we say his name now – LOL)
RE: https://thecyberwire.com/podcasts/caveat/30/notes
Donna Grindle’s Fan Club is alive and well! Donna answered a question for a listener on The Cyberwire’s Caveat. However, David still is not mentioned. So every time I hear Donna on Caveat, I think of David Sims as the “Silent David” 🙂 Just like what IT and cybersecurity support is like in COVID-19 … always there but never mentioned.
Of course, it could also be like acne…
Cyberattacks coming from inside the network
It may seem odd when we try to explain this but the statistics are showing the cyber criminals continue to evolve and find ways around all of our defenses as quickly as we build them. That is the primary reason we keep urging everyone to take part in protecting information systems regardless of their roles. Sophos published an article recently, The ransomware that attacks you from inside a virtual machine, that points it out yet again. The following excerpt really explains the basics of what is happening.
Running their malware inside a virtual machine allowed them to hide it from the prying eyes of security software on the host.
And because the attackers controlled the host they were easily able to weaken the wall between the host and the guest.
This is very tricky stuff.
The concept of virtual machines sounds simple to those of us that are techie. But we live in a virtual world happily. What it really means in layman’s terms is always hard for us to be sure we get across. Our best shot is that you make one physical computer look like multiple computers on the network. You don’t see what is happening on the “other computer” that is running behind the scenes on your computer. It is like you added a guest room and don’t even know it is there and occupied.
By using this set up the criminals are able to work on your computer in a hidden manner doing whatever they choose without you even noticing unless there are special monitors in place to find them. It is super scary but it also means they are able to attack you directly from within the network. They are there with you watching everything you do.
This stuff is getting worse and they know there is so much going on today the distraction level and the quick deployment of technology is making things very easy for them.
According to the World Economic Forum’s Global Risks Report from January of this year cyber crime is a huge business.
As a side note, the report also mentioned concerns about health systems under new pressures that included this statement:
Progress against pandemics is also being undermined by vaccine hesitancy and drug resistance, making it increasingly difficult to land the final blow against some of humanity’s biggest killers. As existing health risks resurge and new ones emerge, humanity’s past successes in overcoming health challenges are no guarantee of future results.
This report was released Jan 15, 2020.
Back to our topic, the report says cybercrime will be the second most-concerning risk for global commerce over the next decade. It’s also the seventh most-likely risk to occur, and eighth most impactful risk we face in the list. This pandemic has made it clear that we operate a vast amount of our businesses based on the ability to use technology and the internet. The impact on cyber crime’s ability to attack is only just now being felt, I fear. The important point the report made about cybersecurity lags was clear then and probably much more likely now:
using “security-by-design” principles to integrate cybersecurity features into new products is still secondary to getting products quickly out into the market.
Yes, that is something we have discussed repeatedly. We also know that the quick transition from business as usual to business during lockdown opened many doors that we still don’t know about yet.
The clear issue being brought to our attention is that no one is immune from cyber attacks today unless they have no access to the internet or technology.
Cyberattacks on critical infrastructure— rated the fifth top risk in 2020 by our expert network—have become the new normal across sectors such as energy, healthcare, and transportation. Such attacks have even affected entire cities. Public and private sectors alike are at risk of being held hostage. Organized cybercrime entities are joining forces, and their likelihood of detection and prosecution is estimated to be as low as 0.05% in the United States. Cybercrime-as-a-service is also a growing business model, as the increasing sophistication of tools on the Darknet makes malicious services more affordable and easily accessible for anyone.
Have you checked the children
New ways to attack keep coming even though there was a dip in new vulnerabilities logged. The ones listed below are all new issues.
7 New Flaws Affect All Thunderbolt-equipped Computers Sold in the Last 9 Years
Improper Microsoft Patch for Reverse RDP Attacks Leaves 3rd-Party RDP Clients Vulnerable
Netwalker Ransomware Tools Reveal Attacker Tactics …
New Android Flaw Affecting Over 1 Billion Phones Let Attackers Hijack Apps
New Tool Can Jailbreak Any iPhone and iPad Using An Unpatched 0-Day Bug
It’s really coming from inside the house
It is getting seriously bad when the cyber criminals are attacking each other. We heard about this happening before but this is all new levels. Hackers are targeting other hackers by infecting their tools with malware tells us some pretty interesting ways they are stealing from each other.
Criminals build malware tools and post them for other criminals to use. Here is the trick though. The developers include a special back door for themselves in the code. One of the gangs uses the malware to attack and does all the work to get it installed on a network. They start doing whatever they intended to do in the attack. BUT, the original developers are now ALSO able to infiltrate your network without being noticed. Not only do you have to catch one of them but now you have to catch both of them.
Researchers found this going on but no one is exactly sure, so far, what they are up to with this scheme.
It is not the time to relax at all in the security world. The way they are attacking keeps ramping up and getting more sophisticated. We fear that many organizations will have no idea whatsoever about attacks happening until they have been completely taken over. Urge your tech teams to take these threats seriously and not assume that old tools will find these new attacks.
Remember to follow us and share us on your favorite social media site. Rate us on your podcasting apps, we need your help to keep spreading the word. As always, send in your questions and ideas!
HIPAA is not about compliance,
it’s about patient care.TM
Special thanks to our sponsors Security First IT and Kardon.


