
In today’s episode, we talk with Josh Corman, Chief Strategist Cybersecurity and Infrastructure Security Agency (CISA) at the Department of Homeland Security. We will learn about CISA and what information and freely available services they provide to help healthcare businesses and other organizations within the nation’s 16 critical infrastructure sectors from cyber attacks.
In this episode:
CISA Interview – Ep 327
Today’s Episode is brought to you by:
Kardon
and
HIPAA for MSPs with Security First IT
Subscribe on Apple Podcast. Share us on Social Media. Rate us wherever you find the opportunity.
Great idea! Share Help Me With HIPAA with one person this week!
Thanks to our donors. We appreciate your support!
If you would like to donate to the cause you can do that at HelpMeWithHIPAA.com
Like us and leave a review on our Facebook page: www.Facebook.com/HelpMeWithHIPAA
If you see a couple of numbers on the left side you can click that and go directly to that part of the audio. Get the best of both worlds from the show notes to the audio and back!
CISA Interview
Meet Josh Corman
[06:44] Today, we talked with Josh Corman, the Chief Strategist for the CISA Covid task force. CISA is the Cybersecurity and Infrastructure Security Agency under the Department of Homeland Security. As Josh explains it, CISA was…This is not the only hat that Josh wears. He teaches CISA programs for the Carnegie Mellon University Graduate School and serves as a CTO, CISO, CSO type in public and private companies. He served on a Congressional task force for healthcare industry cybersecurity. He is also a founder of IAmTheCavalry.org which is a volunteer group of over a thousand helpful hackers trying to save lives through security research.
And, if that’s not enough, Josh also serves on the 405d task force along with the two of us.
CISA is not a regulator and it’s not law enforcement. It exists to help identify and reduce risk, both cybersecurity and physical security, to our nation’s interest in our critical infrastructure sectors. Their services are taxpayer funded and are FREE to anyone in one of the 16 critical infrastructure sectors. Here are a few links that can give you a better understanding of what CISA does and what they specifically do in healthcare.
Healthcare and Public Health Sector
Critical Infrastructure Partnership Advisory Council
Health Sector Cybersecurity Coordination Center (HC3)
Josh Corman is a catch phrase machine
Josh’s terms and catchphrases are now taking hold at Kardon and elsewhere. You’ll hear these throughout our conversation with him.
- Target rich and cyber poor.
- A call to one is a call to all.
- Left of boom and right of boom (before harm and after harm)
- Incident response exercises to create muscle memory.
- Forming. Storming. Norming. Performing.
- CyHy (Cyber Hygiene)
Resources available
[26:33] Several years ago CISA released a report that included a graphic that lists five uncomfortable truths about the state of cybersecurity.- There is a severe talent shortage of cybersecurity professionals in the healthcare industry. It was estimated, at the time, that 85% of US hospitals lacked a single qualified professional on staff. Many of the medium, small and rural hospital systems had none.
- There was a legacy technology epidemic as it wasn’t uncommon to find Windows XP, for example, machines still running in the clinical environment. At that time, Windows XP was an unsupported end of life operating system and therefore very hard to defend against its vulnerabilities.
- Premature and hyperconnectivity – In the race to tie reimbursement to the ability to receive and transmit electronic health records, companies were in a hurry to take existing medical devices that were never designed or intended to be connected to a computer network and forced them to connect to everything. This led to flat, unsegmented networks that created a greater risk that an attack on insufficiently secured devices could take down an entire network or hospital.
- It’s not just privacy that is affected by a cyber attack, but also patient care. A single flaw on a single device that is exploited can affect patient care.
- A single device that is not secure due to outdated software, technology or connection protocols connected to a network could give a thousand or more chances to be exploited and take a network down and affect patient care. It only takes one, though.
These are just the top 5 uncomfortable truths of many about cybersecurity and this is not a good thing.
- Vulnerability Scanning – A free external perimeter vulnerability scan performed daily of public, static IPs to identify any low hanging fruit available to the world. You will receive weekly vulnerability reports and ad-hoc alerts.
- Web Application Scanning – Assesses publicly-accessible websites for potential bugs and weak configuration and provides recommendations to mitigate any vulnerabilities.
- Phishing Campaign Assessment – An opportunity to assess the potential susceptibility of staff to phishing attacks. It can help measure the effectiveness of your security awareness training.
- Remote Penetration Test – Tests perimeter defenses and security using tactics and techniques that cyber attackers use.
Donna 2 cents: I had clients test out the process to request Cy Hy vulnerability scans and it seems to have gone through fine for the two entities I checked. One was a private practice and the other was a county health agency.
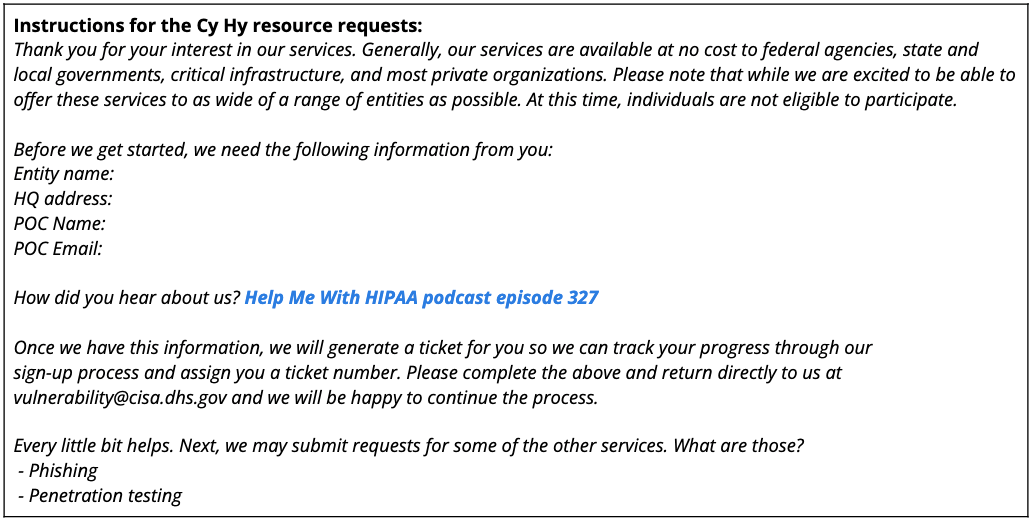
To get started, send an email to vulnerability@cisa.dhs.gov with the subject line “Requesting Cyber Hygiene Services” or follow the instructions below. These instructions are from the response received after sending the email mentioned above:
All kinds of other resources out there… for everyone.
There are a number of other resources available to help keep your organization safe.
Bad Practices – [47:54] CISA has created a catalog of bad practices that are exceptionally risky for organizations, especially those supporting the critical infrastructure sector. The list will continue to grow as with the common, yet dangerous security practices.
Stuff Off Search – [53:33] This is a resource to help you understand what is viewable on the internet and how you can reduce your attack surface.
4 Things You Can Do To Keep Yourself Cyber Safe – [55:18] There are four basic cyber hygiene tasks you can do to protect yourself online.
Ransomware is the big one.
[56:42] Not only does CISA give special attention to the 16 critical infrastructure sectors, but there is also a different way they slice these sectors. They have broken them into the 55 National Critical Functions (NCFs). Providing Medical Care is one of them, hence the title of the Provide Medical Care is in Critical Condition: Analysis and Stakeholder Decision Support to Minimize Further Harm report CISA recently published.CISA has three main focuses for this report:
- As Provide Medical Care is under severe stress and strain, cyber attacks can make it much worse.
- As Provide Medical Care continues to struggle, its impacts are not isolated to citizens in health care. All 55 NCFs are experiencing impacts on their workforce.
- CISA is targeting state, local, tribal and territorial leaders to help them with decision support so that they can measure, track and mitigate risk.
Josh explains very well how stressed our healthcare systems were/are strained by COVID and the impact of cyber attacks just exacerbates the strain and has a negative impact on the 55 NCFs. Some of the points he makes, and that are in the report, are tough to hear/read, but they are important for us to understand in order to come together and work on solutions to minimize the risks and impacts. Listen to this section of the podcast to hear why CISA has renewed their push to engage IT professionals and leadership in hospitals across the nation to help make sure the preventable disruptions are prevented until the end of the pandemic.
[01:14:39] The October 5, 2021 405d Spotlight Webinar for Cybersecurity Awareness Month includes an excellent discussion about the impact of a ransomware attack on Vermont Univ Medical Center during the height of the pandemic. Also, it featured Josh and his Captain America shield. Watch the full recording here. You can also download the slide deck from the talk here. [01:17:05] The number one cyber attack that really brings folks down to their knees is ransomware. Recently, an article was released stating that Mandiant researchers have noticed the FIN12 ransomware gang are aggressively targeting healthcare.FIN12 Ransomware Attackers Target Medical Facilities | Decipher
Ransomware has become an important topic of the federal government. So, CISA has created a single location for ransomware information for the whole federal government, so that there is no competing information or partial information. It’s a site called StopRansomware.gov. It incorporates some of the best information from the FBI, Secret Service, HHS, the different cybersecurity risk management agencies and, of course, CISA themselves to try to make the topic of ransomware clearer. It separates ransomware information in three main focuses:
- What is ransomware?
- Have you been hit by ransomware?
- Avoiding being hit by ransomware.
CISA is also providing more actionable advice on ransomware with its CISA Summit, which happens each week during National Cybersecurity Awareness Month. The weekly (recorded) summits include public talks with world class speakers from inside and outside of government and includes findings from a huge ransomware task force
One way to get attention of stakeholders is this is now a patient care, patient safety, patient life issue.
We now stand on the cusp of really understanding the next wave of how to reduce loss of life and provide better patient care in the future.Josh Corman, CISA
Our conversation with Josh just reiterates our Help Me With HIPAA tagline: HIPAA is not about compliance, it’s about patient care. We appreciate Josh spending some much time talking with us today and educating us all on all the things CISA and their partners are doing to help defend us against cyber threats. It is reiterating that cybersecurity is no longer only an IT issue.
Remember to follow us and share us on your favorite social media site. Rate us on your podcasting apps, we need your help to keep spreading the word. As always, send in your questions and ideas!
HIPAA is not about compliance,
it’s about patient care.TM
Special thanks to our sponsors Security First IT and Kardon.


