 Is it still a lie if it’s only half false? Asking for a biotech company that might’ve taken “fake it till you make it” a bit too literally with their cybersecurity claims. From hard-coded admin credentials to ignoring vulnerabilities like a bad ex’s texts, this episode dives into what happens when convenience beats caution and how a $9.8 million lesson got served with a side of whistleblower justice.
Is it still a lie if it’s only half false? Asking for a biotech company that might’ve taken “fake it till you make it” a bit too literally with their cybersecurity claims. From hard-coded admin credentials to ignoring vulnerabilities like a bad ex’s texts, this episode dives into what happens when convenience beats caution and how a $9.8 million lesson got served with a side of whistleblower justice.
In this episode:
Is a Half Truth a Whole Lie – Ep 530
Today’s Episode is brought to you by:
Kardon
and
HIPAA for MSPs with Security First IT
Subscribe on Apple Podcast. Share us on Social Media. Rate us wherever you find the opportunity.
Great idea! Share Help Me With HIPAA with one person this week!
Learn about offerings from the Kardon Club
and HIPAA for MSPs!
Thanks to our donors. We appreciate your support!
If you would like to donate to the cause you can do that at HelpMeWithHIPAA.com
Like us and leave a review on our Facebook page: www.Facebook.com/HelpMeWithHIPAA
When you see a couple of numbers on the left side of the text below click that and go directly to that part of the audio. Get the best of both worlds from the show notes to the audio and back!
Is a Half Truth a Whole Lie
[03:15]A big-name biotech company, Illumina, just shelled out $9.8 million to settle allegations that they misrepresented the cybersecurity of their genomic sequencing software to federal agencies. This is one of the first times we’re seeing the False Claims Act used to go after a company not for a breach, but simply for failing to meet claimed cybersecurity standards – even if no incident occurred. And there’s a whistleblower at the center of it all.
1. The Case Overview
- Illumina sold DNA sequencing devices with software called Local Run Manager (LRM) and Universal Copy Service (UCS).
- According to the filings: “Illumina has received at least hundreds of millions of dollars in Medicare reimbursement through these various sources.”
- “Confidential patient data is housed on all Illumina products including HIPAA-protected data of Medicare beneficiaries such as their genetic test results.”
- It is important to note that the software involved here is also regulated by the FDA which has more specific requirements than just HIPAA.
- According to the filings: “Illumina has received at least hundreds of millions of dollars in Medicare reimbursement through these various sources.”
- They claimed the software met ISO and NIST cybersecurity standards when it didn’t according to the complaint.
- “Illumina has represented that it “is committed to data security” and has the sophistication, expertise, technology, and resources to comply with its obligations”
2. What the Feds Alleged
- “Illumina has knowingly ignored and minimized cybersecurity vulnerabilities in its products; failed to mitigate or correct known cybersecurity defects in its products, even resisting internal efforts to mitigate or correct the defects; and failed to disclose cybersecurity vulnerabilities to the Government.”
- Illumina put information or systems at risk by:
- knowingly providing deficient cybersecurity products or services
- knowingly misrepresenting their cybersecurity practices or protocols, or
- knowingly violating obligations to monitor and report cybersecurity incidents and breaches.”
- And still claimed their software complied with well-known standards.
3. The Whistleblower Angle
- Erica Lenore filed the original complaint under the FCA’s qui tam (pronounced: “kwee tam” or “kwee tom”) provisions.
- A private individual (called a relator) filing a lawsuit on behalf of the government, usually because they’ve discovered fraud involving taxpayer dollars.
- She’s getting $1.9 million for speaking up.
Erica Lenore was Director for Platform Management.
Illumina has improperly allowed elevated privileges to users running genetic tests on Illumina products that are connected to an open network. These users include everyone – research assistants, third-party vendors, laboratory technicians, scientists, clinical investigators, engineers, and research and development staff – individuals who have no need for access to confidential and HIPAA-protected patient data including genomic test results. Further, this remains a known cybersecurity vulnerability, which Illumina has failed to mitigate or correct.
Illumina hard-coded credentials, allowing users access to confidential patient data, without authentication. By hard coding credentials, Illumina embedded credentials (e.g., usernames and passwords) into its software. “Hard-coded credentials typically create a significant hole that allows an attacker to bypass the authentication that has been configured by the product administrator.”
Illumina ignored the known risks of insider threats despite internal and third-party reports that its products had known cybersecurity vulnerabilities including ones that Illumina itself caused.
Illumina’s knowledge of material cybersecurity failures long predated the launch of its products and fall generally within three overlapping categories:
- Improper granting of elevated privileges to everyday users;
- Hard coding of credentials to bypass authentication; and
- Failures to mitigate insider threats
In the limited instances in which Illumina did address cybersecurity failures, it did so only after complaints from third parties that malicious actors had exploited vulnerabilities in its products. Further, mitigation was incomplete and failed to disclose the scope of the vulnerabilities.
- In Jan 2016, the Univ of Pennsylvania was hit with a ransomware attack and a professor was specifically told NOT to change his log-in information on their system after the attack.
- In Sept 2018, a prof at UC Santa Cruz using another product was victimized by another ransomware attack.
High-level meetings with senior management discussed these problems but no one took any corrective action because they prioritized their time-to-market over security… repeatedly. At an April 20, 2022 meeting they specifically discussed the cybersecurity deficiencies and insufficient safeguards alleged. The Director of Product Security delivered a presentation at that meeting and specifically covered these problems as “SDLC opportunities”
There is even screen shots of the presentation:
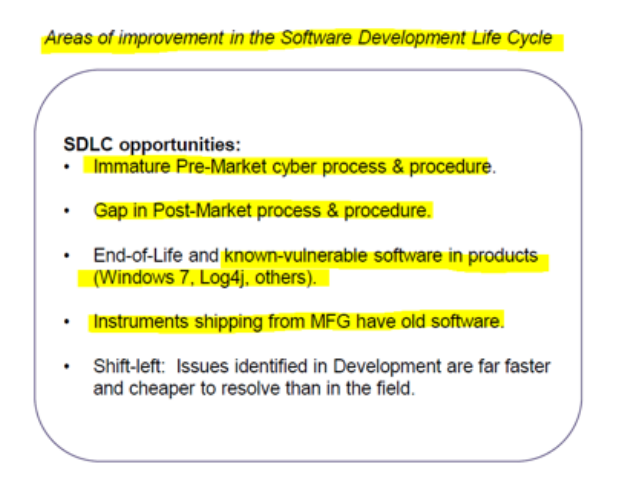
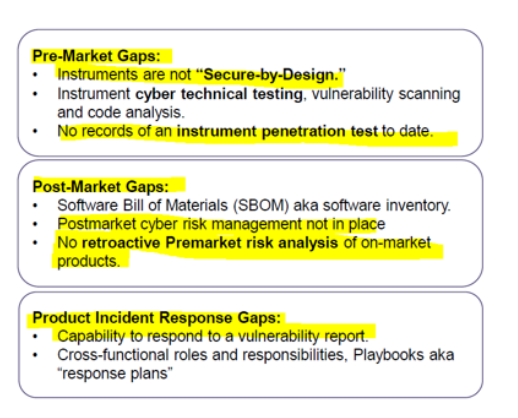
No penetration testing before launching products, no real serious attempts to secure anything. That meeting included a proposal of cybersecurity protections to create a “minimal viable product” which was kicked to the curb also.
These recommendations included cybersecurity risk assessments of products in the pre-market phase such as threat modeling and cyber-technical and penetration testing; and cybersecurity risk assessments of products in the post-market products phase such as vulnerability technical scanning and monitoring and cybersurveillance. However, Illumina has failed to act on these recommendations despite its certifications to the Government to the contrary.
When they did release information about vulnerabilities it was years after knowing about them and included “half-truths” about their status. They even went so far as to completely remove safeguards like access limitations which gave users admin access to everything on the system, not just their software.
Illumina said their systems were secure. They weren’t. They said they followed standards. They didn’t. And they paid nearly ten million dollars because someone inside the company had the courage to say, “This isn’t right.”
Whether you’re building tech, buying it, or just clicking “I agree” on a compliance checklist, remember: a half-truth is a whole lie when the stakes are this high.
And if you’re ignoring cybersecurity because no one’s hacked you yet… well, someone might still come knocking. It just might be the Department of Justice.
Turns out, when your cybersecurity plan is “wing it and hope no one notices,” someone will notice — and they might just walk away $1.9 million richer. From outdated software to admin access for everyone with a pulse, this episode shows how pretending to do the right thing is almost worse than doing nothing at all. So, whether you’re a startup or a tech giant, take note: the cost of cutting corners might not show up on your next invoice, but it could land in your next subpoena.
Remember to follow us and share us on your favorite social media site. Rate us on your podcasting apps, we need your help to keep spreading the word. As always, send in your questions and ideas!
HIPAA is not about compliance,
it’s about patient care.TM
Special thanks to our sponsors Security First IT and Kardon.


