Turns out, “they got hit, they just didn’t tell you” isn’t just a snarky title—it’s a terrifying reality. The Black Fog report basically says, “Hey, the cybersecurity iceberg is way bigger below the surface.” From undisclosed data heists to the rapid rise of ransomware attacks, this is your reminder that you don’t want to be the next plot twist in a cyber thriller. Oh, and yeah… shadow AI is watching too. Sleep tight!
In this episode:
They Got Hit. They Just Didn’t Tell You. – Ep 506
Today’s Episode is brought to you by:
Kardon
and
HIPAA for MSPs with Security First IT
Subscribe on Apple Podcast. Share us on Social Media. Rate us wherever you find the opportunity.
Great idea! Share Help Me With HIPAA with one person this week!
Learn about offerings from the Kardon Club
and HIPAA for MSPs!
Thanks to our donors. We appreciate your support!
If you would like to donate to the cause you can do that at HelpMeWithHIPAA.com
Like us and leave a review on our Facebook page: www.Facebook.com/HelpMeWithHIPAA
When you see a couple of numbers on the left side of the text below click that and go directly to that part of the audio. Get the best of both worlds from the show notes to the audio and back!
Another SRA Settlement
[04:59]NERAD PACS breach March 2020 settlement in 2025 for $350k and a 2 year CAP.
HHS OCR Agreement Northeast Radiology, P.C. and CMP Violation
OCR announced the 6th enforcement action on SRAs in a settlement with Northeast Radiology, P.C. (NERAD), they provide clinical services at medical imaging centers in New York and Connecticut,
“A HIPAA risk analysis is essential to identifying where electronic protected health information is stored, and the security measures in place to protect it,” said OCRActing Director Anthony Archeval. “A failure to conduct a risk analysis often foreshadows a future HIPAA breach.”
Picture Archiving and Communication System (PACS) servers are for storing, retrieving, managing, and accessing radiology images. They are also notorious for security issues. NERAD filed a breach notification report in March 2020. They discovered that between April 2019 and January 2020, unauthorized individuals had accessed radiology images stored on NERAD’s PACS server. That required notifying 298,532 patients of the breach.
They Got Hit. They Just Didn’t Tell You
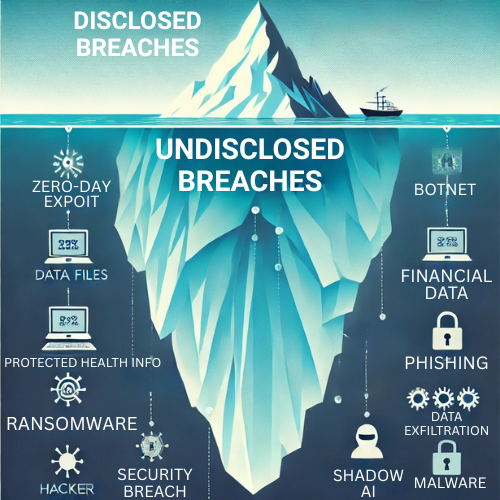
[13:37]The Q1 2025 State of Ransomware Report from BlackFog covers the usual stats you’d expect—who got hit, which industries are suffering, and which ransomware gangs are making the most noise. But what really grabbed our attention (and why we’re talking about it) is what isn’t usually talked about: the attacks that never got officially reported. This report dives into the dark web to track undisclosed ransomware incidents, offering a rare look at the true scale of the problem. That’s the kind of data you don’t see in most cybersecurity reports—and it’s exactly why we think this one deserves a closer look.
What makes this report stand out isn’t just the numbers—it’s how BlackFog got them. To track ransomware activity, they didn’t just rely on public breach notifications. They also went deep into the dark web, monitoring leak sites run by ransomware gangs to catch incidents that never made the news.
But here’s the kicker: even among the 278 publicly disclosed ransomware attacks, 64 of them hadn’t shown up on the dark web yet. That tells us something big—what gets posted by attackers is far from a complete picture. So if we’re seeing over 2,100 undisclosed attacks based on dark web data alone, the real number of unreported incidents might be even higher.
If a breach happens and it’s not reported and doesn’t show up in a ransom blog… did it even happen? If a tree falls in the woods….
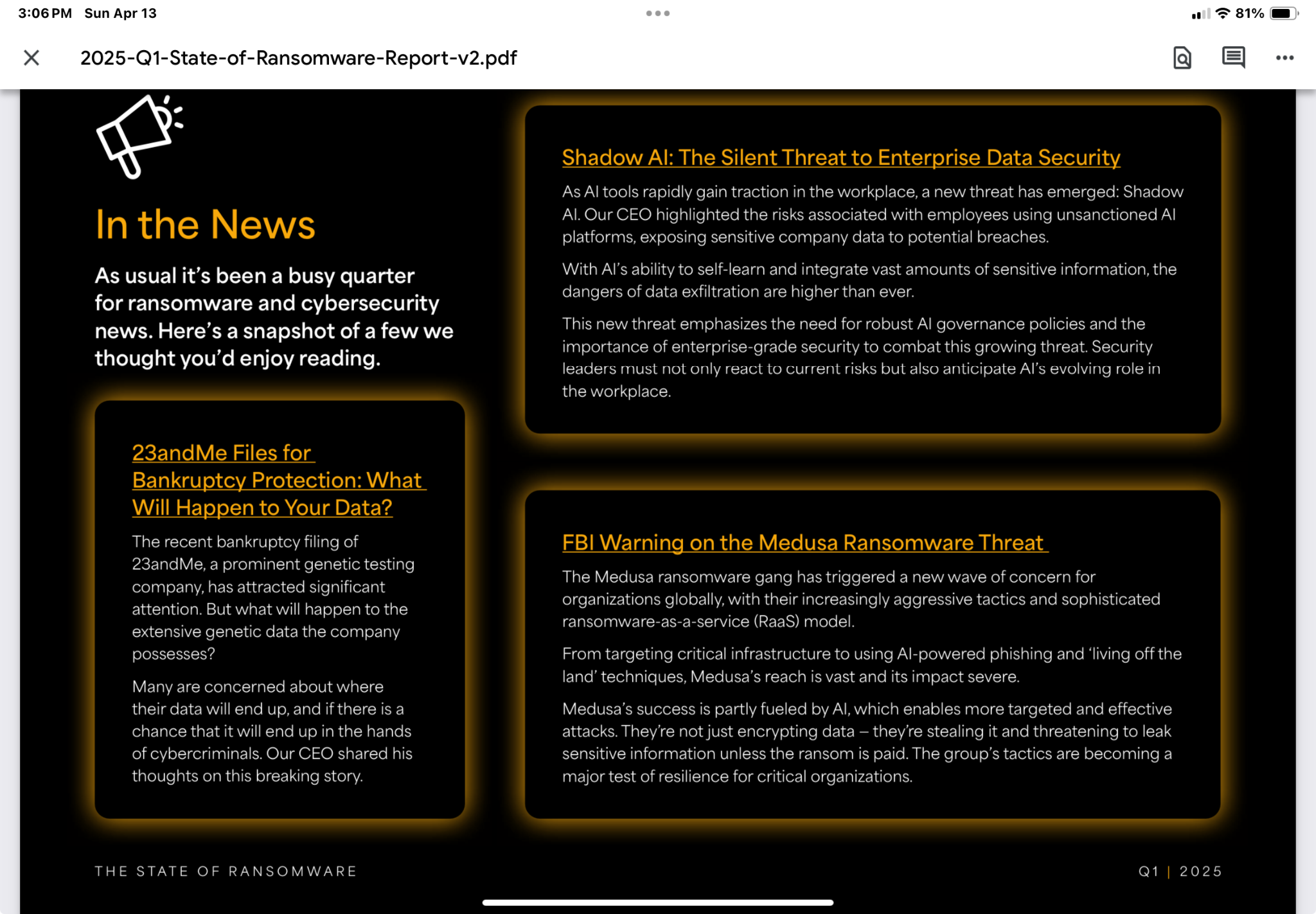
[19:27]Buried in the report—but definitely worth dragging into the daylight—is a warning about Shadow AI. No, it’s not a new Marvel villain, it’s your employees secretly using AI tools that the company hasn’t approved. BlackFog calls it a silent threat, and they’re not wrong. There’s a potential security risk, as sensitive company data like patient records and your business information or trade secrets might be shared with external AI platforms. Then, who knows where it will be going next. We already covered the report recently that said this is definitely happening AND no one is being trained on AI.
One quick word of warning before you get too excited by the charts in this report: the graphs showing disclosed vs. undisclosed ransomware attacks may look like a clean side-by-side—but the scales aren’t even in the same ballpark. The chart for disclosed attacks tops out at 60, while the one for undisclosed goes up to 500. So, while healthcare looks like a major target on the disclosed side and barely a blip on the undisclosed one, the actual number of undisclosed healthcare attacks is more than double the disclosed count.
It’s a good reminder: sometimes graphs don’t lie, but they sure can mislead. Always check the y-axis before jumping to conclusions. Healthcare looks huge on the disclosed side but much smaller on the undisclosed side. BUT… when you realize that the small bar on the undisclosed side is well over 100 probably close to 150. That’s double the number disclosed!
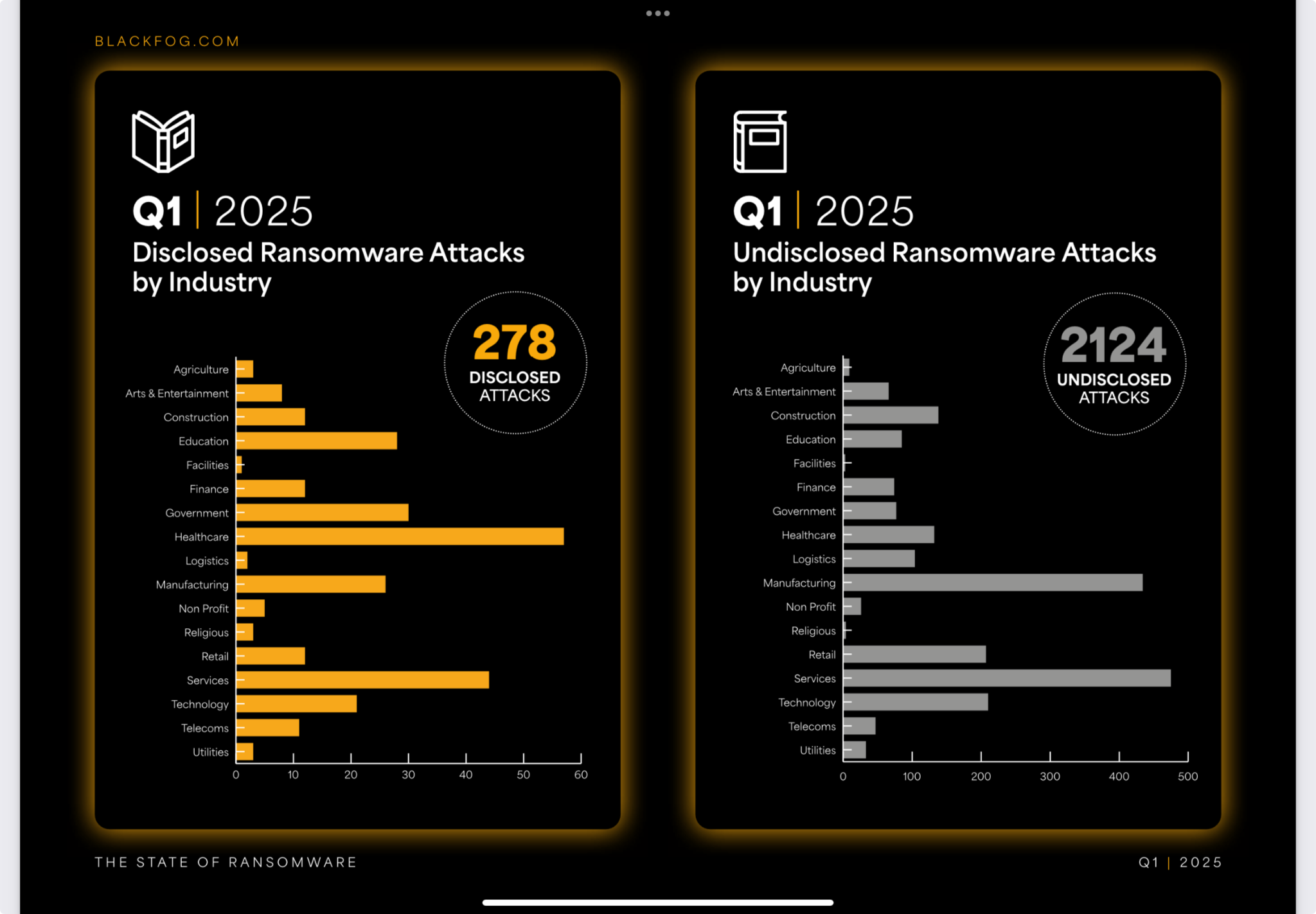
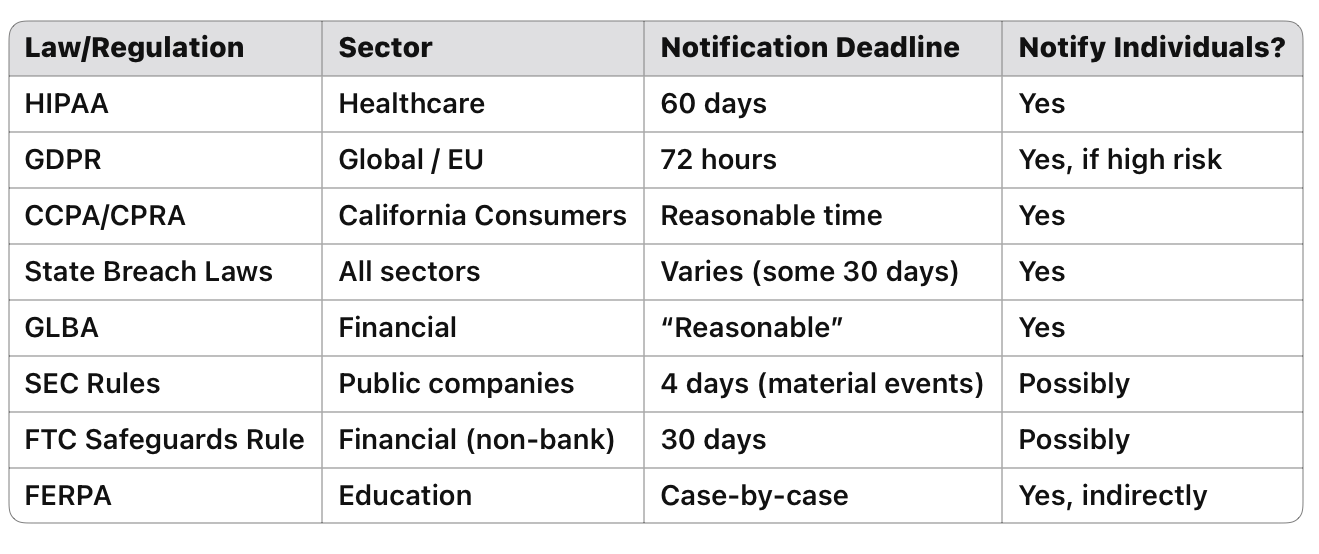
Yes, these numbers are global. But, there are very few places in the world where you could have a data breach in healthcare and not be required to disclose it under some law or regulation. It really shines a light on what we have discussed many times, all healthcare data breaches are not being disclosed.

To wrap it up, the final chart in the report confirms what many of us suspected: the United States is ransomware’s favorite punching bag, leading the pack in both disclosed and undisclosed attacks. Whether companies admit it or not, they got hit. And when it comes to who’s walking away with the data, China takes the gold medal in exfiltration by far. So even if you’re lucky enough to recover your systems, your data may already be halfway around the world, starring in someone else’s cyber espionage campaign. It’s a stark reminder that in 2025, the real story isn’t just about who got hit—it’s about who didn’t tell you.
After peeling back the digital curtain on the Black Fog report, one thing’s clear: the cyber boogeymen are real, and they’re not waiting for an invitation. Whether it’s shadow AI tiptoeing through your data or a breach that nobody bothered to mention, it’s all happening—quietly, stealthily, and way too often. So, let’s put “ignorance is bliss” on the shelf next to floppy disks and dial-up modems. Knowledge is power, friends. Use it.
Remember to follow us and share us on your favorite social media site. Rate us on your podcasting apps, we need your help to keep spreading the word. As always, send in your questions and ideas!
HIPAA is not about compliance,
it’s about patient care.TM
Special thanks to our sponsors Security First IT and Kardon.



