If you are a regular listener of the podcast, you know how Donna loves to “HIPAA-geek out” over the National HIPAA Summit each year. This year’s National HIPAA Summit did not disappoint. Today, we discuss a few points made concerning enforcement of HIPAA related cases by three arms of the federal government.
In this episode:
3 HIPAA Enforcement Arms – Ep 348
Today’s Episode is brought to you by:
Kardon
and
HIPAA for MSPs with Security First IT
Subscribe on Apple Podcast. Share us on Social Media. Rate us wherever you find the opportunity.
The Privacy and Security Boot Camp
3.5 day In Person Event
Sep 12, 13, 14 and 15
PriSecBootCamp.com
Great idea! Share Help Me With HIPAA with one person this week!
Learn about offerings from the Kardon Club
and HIPAA for MSPs!
Thanks to our donors. We appreciate your support!
If you would like to donate to the cause you can do that at HelpMeWithHIPAA.com
Like us and leave a review on our Facebook page: www.Facebook.com/HelpMeWithHIPAA
If you see a couple of numbers on the left side you can click that and go directly to that part of the audio. Get the best of both worlds from the show notes to the audio and back!
HIPAA Say What!?!
Our entire podcast today HIPAA Summit News is a HIPAA Say What!?!
405(d) Tip of the Week
[04:43] 405d Prepare React Recover Ransomware One PagerPreparing for, preventing, and recovering from Ransomware attacks is paramount to patient safety.
Follow these industry tested best practices (Prepare, React, Recover) to ensure your organization
is prepared for these attacks and can continue to keep patients safe in the event of an attack.
The one page guide has it grouped nicely so you get a section for before, during and after an attack. You could break these sections up for your teams to review and compare to your current Incident Response Plan. Or…. maybe build an Incident Response Plan from it.
How Enforcement Works
[12:40] Many of the people we talk with that haven’t been listening to our podcast or coming to our training events have minimal understanding of how HIPAA enforcement really works. Several cases reviewed at the National HIPAA Summit, that Donna just attended virtually, reminded us of that point. Today, let’s discuss some of the points made concerning enforcement of HIPAA related cases by all 3 arms that can provide enforcement.Federal Trade Commission (FTC)
A lot of folks have no idea that the FTC and OCR can both bring enforcement actions relating to HIPAA privacy and security violations in a single case. Section 5 of the FTC Act makes it possible for that to happen for two reasons:
Deception
A material representation or omission that is likely to mislead consumers acting reasonably under the circumstances
Unfairness
A practice that causes or is likely to cause substantial injury to consumers that is not outweighed by countervailing benefits to consumers or competition and is not reasonably avoidable by consumers
The FTC attorney covered a few but here are a couple of points they hit on specifically:
- If your privacy policy says you will be doing something and then you don’t that can be considered deception. Like saying you follow privacy standards and then share personal information with Facebook, Google and others. (Ex: Flo Health)
- It isn’t just what you say but also can involve what you fail to say to consumers. If a consumer would be surprised by what you are doing then you should rethink your messaging. (Ex: Practice Fusion)
- If you tell your business clients that your software or services will make them HIPAA compliant with standards you should be sure that is happening. (Ex: Henry Schien) This one we’ve covered before because they said their application met HIPAA standards but it turned out the vendor doing encryption on the back end actually told them they were not compliant with industry standards.
These settlements don’t make as much news because they don’t come out of HHS – we even missed this one! A Nevada-based company. Provides travel emergency services. A settlement with the FTC over allegations the company failed to take reasonable steps to secure sensitive consumer information. They left a whole database of records unsecured on a cloud service.
- Didn’t use reasonable measures to secure personal information, leaving a cloud database with health info unsecured
- Misled consumers about its response to the incident (they first said there was no sensitive info in the database when a security researcher notified them it was out there)
- With “HIPAA Compliance” seal on its website, falsely implied that its privacy policies had been reviewed and met HIPAA security/privacy requirements.
This is the “seal” that was on SkyMed’s website, no longer there now.

So, if you are putting up a HIPAA compliant seal consumers may be taking away from that you are, in fact, covered by HIPAA and that you are, in fact, complying with HIPAA’s requirements. So, if you are a company that is not covered by HIPAA or you are not complying with HIPAA’s requirements then you should think very carefully before deciding to slap up that reassuring seal on your website or other marketing materials.Elisa Jillson, Counsel to the Director, Bureau of Consumer Protection FTC at 2022 National HIPAA Summit
Twice she used the phrase “slap up” when talking about seals and logos on the website! Lawyers do not toss that kind of phrasing around carelessly. (We will get back to paying attention to the way these lawyers phrase things in a minute.) Here is what the settlement specifically said relating to the use of those logos or seals (emphasis added):
A. The extent to which Respondent is a member of, adheres to, complies with, is certified by, is endorsed by, or otherwise participates in any privacy or security program sponsored by a government or any third party, including any self-regulatory or standards setting organization;
B. The extent of any Covered Incident or unauthorized disclosure, misuse, loss, theft, alteration, destruction, or other compromise of Personal Information;
C. The extent of any investigation and the results thereof, whether conducted by Respondent, a governmental agency, or a third party, into any Covered Incident or unauthorized disclosure, misuse, loss, theft, alteration, destruction, or other compromise of Personal Information;
D. The extent to which Respondent collects, maintains, uses, discloses, deletes, or permits or denies access to any Personal Information; and
E. The extent to which Respondent otherwise protects the privacy, security, availability, confidentiality, or integrity of any Personal Information.
The CAP (corrective action plan) in this settlement is very detailed about the requirements for the “Information Security Program” that must be developed and maintained by SkyMed. Oh, and one very important point on this CAP: FTC CAPS run for 20 years.
OCR and DOJ
[35:01] It is sometimes interesting to watch your audience when you do training on HIPAA and point out that you can go to jail for up to 10 years for HIPAA violations. They can actually bring in the DOJ and make a federal case out of it. The HHS OCR is the main enforcement agency but they can choose to refer cases to the DOJ for criminal charges and their investigation can be done in a completely different process than what you see with FTC and OCR jurisdiction.Important note here: Unless there is a settlement, arrest, or one of the rare real CMP (civil money penalty) enforcement actions you will never hear about the thousands of cases that go through this process. It is very rare you get any confirmation or details about the findings other than general numbers unless you are directly involved.
How can you end up at OCRs doorstep?
- Have a data breach:
- 500 or more patients
- Smaller data breaches that grab the attention of enforcement agencies because of the situation or severity. Things like that make the news.
- A complaint is filed directly to HHS
- Patients
- Disgruntled employees
- Competitors
- Anyone
- Selection for a random audit
- Only 2 audit phases ever done
- Very limited number of businesses and none since 2016.
Audits
Random audits are often discussed as an important tool that should be further implemented under HITECH. These audits are the only ones that OCR refers to as an “audit”. When they have done them in the past, they responded with what OCR felt their compliance effort ratings were. In some cases where there were serious issues found, they referred them for a compliance review. We have never heard of one of these making it to a resolution agreement, so far. For this reason, we assume when people say “audits” and “HIPAA” they don’t fully understand how enforcement works.
Breach and complaint processes
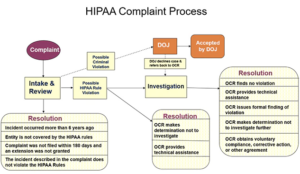
Once you are on the doorstep there are steps that are always taken. OCR has a great chart and discussion of how this works on their website.
First, there is the intake and review process. Some cases never make it past this step. These are the ones that are too old, not covered under HIPAA at all, or actually not a violation of HIPAA in the first place.
If the case could possibly involve a HIPAA violation, they review it a bit further. At this point, they can elect to resolve the case without ever doing a complete investigation. These are ones where they figure out it is a disgruntled employee or they have a discussion with the entity involved and determine not to investigate. Many times we forget the sheer volume of cases that must be reviewed each year. The 2021 annual report hasn’t been released yet, but we know in 2020 and earlier the numbers. HHS OCR 2020 Annual Report to Congress
For 2020 alone they took in over 27k just in complaints. Another 66,509 small breaches were reported. Plus 656 reports of 500 and over data breaches. Based on what we know above, they sorted through those complaints and small breaches to determine if there should be a further review of compliance. Not an investigation (certainly not an audit), but simply looking further at the case because it could signal compliance violations they want to consider further.
Once you see what they are bringing in it gets tougher to know what happens because these things take years plus, as mentioned above, you never learn the outcome for specific cases. When they say they obtained corrective action on a case in 2020 that could have been relating to a case that actually came in during 2018.
There are so very few cases that actually make it to a resolution agreement with a Corrective Action Plan and even fewer with actual Civil Money Penalties that it can become confusing for most people to understand what is actually going on from an enforcement standpoint.
What we can tell you here is that the vast majority of cases coming into OCR are resolved without any big news type enforcement actions. For the most part, they fall under this section of their actions:
Corrective Action Obtained* (investigated):
OCR investigates and provides technical assistance to or requires the covered entity or business associate to make changes regarding HIPAA-related privacy and security policies, procedures, training, or safeguards. In some cases, technical assistance is provided after an investigation without requiring specific corrective action. For example, when the covered entity or business associate has already taken corrective action during the investigation or within the 60-day window prior to notifying OCR of the breach incident.
[48:06] Here is real world example of a technical assistance notice provided to a client:The following links provide comprehensive HIPAA guidance published by HHS/OCR for professional covered entities, such as [CE name]. Please use this resource material to ensure compliance in your facility’s operations. Feel free to share these resources with your workforce.
This is followed by links to all the HIPAA resources published by OCR.
The final note from the HIPAA Summit comes from the first official session by Lisa Pino, the new OCR Director. She just got started in the job and doesn’t really have her hands around everything yet but she did make some interesting points. She covered most of it in a blog post that was released the same day she spoke. Improving the Cybersecurity Posture of Healthcare in 2022 | HHS.gov
Make note of something very important she said both in the blog post and in her speech:
If you haven’t looked at your risk management policies and procedures recently to prevent or mitigate these concerns, now is the time to do so.
So, the real lesson here is enforcement happens in many ways by many entities. Trying to judge too much about any of the numbers of audits and investigations will make your head spin. What you should focus on is staying away from the FTC’s, OCR’s and DOJ’s doorstep, if possible, but being prepared to respond properly if and when you do.
Remember to follow us and share us on your favorite social media site. Rate us on your podcasting apps, we need your help to keep spreading the word. As always, send in your questions and ideas!
HIPAA is not about compliance,
it’s about patient care.TM
Special thanks to our sponsors Security First IT and Kardon.