
There are many challenges that come with preparing for and responding to a ransomware attack. Ransomware gangs are constantly changing their tactics in order to get to your organization’s data. Therefore, as the ransomware landscape continues to evolve, so too must the preparations and responses of businesses.
In this episode:
Consider 3 Ransomware Stories – Ep 323
Today’s Episode is brought to you by:
Kardon
and
HIPAA for MSPs with Security First IT
Subscribe on Apple Podcast. Share us on Social Media. Rate us wherever you find the opportunity.
Great idea! Share Help Me With HIPAA with one person this week!
Thanks to our donors. We appreciate your support!
If you would like to donate to the cause you can do that at HelpMeWithHIPAA.com
Like us and leave a review on our Facebook page: www.Facebook.com/HelpMeWithHIPAA
If you see a couple of numbers on the left side you can click that and go directly to that part of the audio. Get the best of both worlds from the show notes to the audio and back!
HIPAA Say What!?!
[02:51] Have we mentioned that OCR is still behind an enforcement initiative to make sure patients have access to their medical records in a complete and timely fashion for very little, if any, costs?They just announced the 20th action in this initiative. 20 cases for one specific problem is a lot when you understand they set a record for the number of cases announced last year. The whole year was a record.
Children’s Hospital & Medical Center (CHMC) in Omaha, NE has agreed to take corrective actions and pay $80,000.
Consider 3 Ransomware Stories
#1 They’re back.
[08:24] The REvil team is back after going dark. They have supposedly been restored and back in the game. The decryption keys from the Kaseya attack are out in the wild now. If you were hit in that specific attack, you can try to get your old stuff back using those keys. That is great news. The gang claims one of their team members “fat-fingered” the key which is how it got out. In other words, someone made a mistake on the keyboard that released the encryption keys on the Internet.#2 Know thy enemy and know thyself.
[13:19] In another recent article, Ransomware gang’s script shows exactly the files they’re after, we now have a list of the files hackers go after when they run those automated processes once they break into your network.Another article discusses what the gangs consider their perfect victim:
This is the perfect ransomware victim, according to cybercriminals
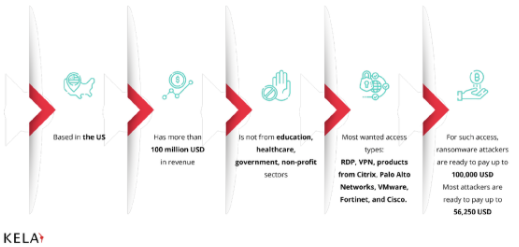
We may know the perfect victim, but that doesn’t mean we won’t see only those victims. The “not in sectors list” isn’t making a big difference when it comes to healthcare if only 50% of the gangs are avoiding it. Just check the news. The best thing you can do is prepare and attempt to prevent or mitigate damage. Do not assume you will be ok.
The best way to be prepared and protected is to learn everything you can about how this stuff works and what you should do if you are attacked. That is called having an incident response plan in place. Everything you should do is also included as requirements under HIPAA. If you do more than “check the box” you will be ready.
[21:45] CISA published a very helpful ransomware response specific guide, CISA MS-ISAC Ransomware Guide, that came out this time last year. However, it will make sense in a second that we do need to make sure you know. This guide includes ransomware prevention best practices and a ransomware response checklist. Good information. Worth the read.We tell you that so we can tell you this. (Nod to Ron White intended.) This past week CISA also shared a new article with information produced by the New Zealand government to help their citizens understand ransomware and be prepared to respond. The charts in that guide are very good. They are some of the best diagrams explaining how these attacks work and where you can attempt to stop them or limit their scope.
Protecting from ransomware – NZ CERT publication with excellent explainer charts.
9 Takeaways: LockBit 2.0 Ransomware Rep ‘Tells All’ – 3 of the 9 takeaways are things that we regularly talk about:
- Expect more supply chain attacks
- Criminals prefer public silence
- Attacks are now more automated
Ransomware gang threatens to wipe decryption key if negotiator hired
Is Grief’s Threat to Wipe Decryption Key Believable?
#3 That’s Gonna Leave A Mark.
[38:44] An Arizona based family medicine practice, Desert Wells Family Medicine, was hit by ransomware that also hit their backups. Not sure what got them here but they say all of their data was corrupted. Does that mean they paid and couldn’t decrypt? We may never know. What we do know is that they lost all their patient’s medical records. This letter to their patients is clearly one that you can tell how much it hurt them to write it when you read it.AZ Ransomware Attack Leads to Unrecoverable EHRs, Data Loss
The opening paragraph of the letter says right up front they have been down for weeks:
So, here’s something to keep in mind… if you called this practice up a month or two before this happened and asked these questions, what do you think they would have said?
- Do you think you are susceptible to a ransomware attack?
- Do you think you can restore from backup even if you are hit by an attack?
- How long do you think you would be down if you were hit by an attack before you are back up and running?
We can guess the answers they would have given us a month ago and now know the answer to all but one of those questions now. The last question is how long will it take to get back to some level of normal? They have no idea at this point.
We do need to remember that this practice is clearly the victim of the attack. However, their patient’s are the ones who will suffer the consequences of the attack with them. I hope for their patient’s sake that they were able to answer those questions the way we know they should have been answered then.
If you feel comfortable that you have it under control, remember that almost every person who ends up in these situations thought the same thing right up until the minute they realized they had been attacked.
Ransomware response plans are a must for any organization, but put a lot of effort into prevention first. Knowing yourself, knowing the ransomware gangs’ tactics and making the right investments are key to preventing a ransomware attack. In other words, as we’ve said many times, this is the time to do a risk analysis and a risk management plan.
Remember to follow us and share us on your favorite social media site. Rate us on your podcasting apps, we need your help to keep spreading the word. As always, send in your questions and ideas!
HIPAA is not about compliance,
it’s about patient care.TM
Special thanks to our sponsors Security First IT and Kardon.


