
Have you ever heard tech folks refer to a computer problem as an ID10T error? You probably thought it was some highly technical term geeks use. Well, it’s not and today we are going to talk about a couple posts and articles where folks’ are flying their ID10T flag high and proud. And hopefully try to prevent you from making an ID10T error.
In this episode:
Don’t Be An ID10T! – Episode 319
Today’s Episode is brought to you by:
Kardon
and
HIPAA for MSPs with Security First IT
Subscribe on Apple Podcast. Share us on Social Media. Rate us wherever you find the opportunity.
Great idea! Share Help Me With HIPAA with one person this week!
Thanks to our donors. We appreciate your support!
If you would like to donate to the cause you can do that at HelpMeWithHIPAA.com
Like us and leave a review on our Facebook page: www.Facebook.com/HelpMeWithHIPAA
If you see a couple of numbers on the left side you can click that and go directly to that part of the audio. Get the best of both worlds from the show notes to the audio and back!
HIPAA Say What!?!
[05:10] First, we want to share a LinkedIn post by William Price, Cybersecurity Consultant for CyberX Cybersecurity Services, regarding the response he received from a potential client when William asked him about the scope of a potential security assessment:This is just another reminder of why we need to vet our vendors and just don’t take their word for it that they take privacy and security seriously.
Next, we have a Twitter post that shows exactly why everyone needs a clean desk policy and a policy prohibiting staff from taking pictures in the office.
https://twitter.com/rnbwkat/status/1426880359371886592?s=12
Needless to say, I am interested in her write up about the honey pot trap she set up. It’s just another reason why you don’t use check the box security!
Don’t Be An ID10T!
[15:06] Ransomware is STILL a top problem. If you haven’t been discussing plans for dealing with an attack you have your head in the proverbial sand.Cybercrime Group Asking Insiders for Help in Planting Ransomware
Cybercrime Group Asking Insiders for Help in Planting Ransomware This article brings to light how cyber criminals are seeking help from employees to plant a ransomware attack on their employer’s network. It’s no longer an attack from outside your network. It is insiders, trusted employees, people who might have worked for the company for 20 years or more. The criminals are making these “get rich quick” schemes very enticing to folks.
You could have a solid cybersecurity program in your organization, but all it takes is one bad apple. Proof that you have to have the people, the processes, and the technology all working together to cybersecurity to work to have even a chance to keep control.
[25:32] Ransomware is still hitting healthcare practices and hospitals. We talked about the Scripps Health Attack in Privacy Questions Everywhere – Ep 304. Information is still coming out about that attack and we continue to follow that news.But this week, there was another report of a healthcare system under attack. Memorial Health System, with 3000 employees and three hospitals and dozens of outpatient clinics in Ohio and West Virginia, had an attack where ransomware slipped through hundreds of servers and thousands of devices used to treat patients in their facilities.
Ransomware Attack: Doctors and Nurses Locked Out of Tools
Memorial Health System hit by ransomware attack that crippled hospitals
Memorial Health System paid the ransom five days after the attack started but they are still diverting patients. Just because you pay the ransom, it doesn’t mean everything gets back up and running immediately. It takes time for systems to be restored, data that was encrypted to be decrypted.
It is imperative that the organization’s decision makers not look at ransomware as an IT problem. It is a patient safety issue, a risk management issue. People’s safety is tied up in our ability to use systems and technology. Decision makers have to change their thought process and decisions on how to address cybersecurity within the organization.
We know this from all the other cases we have heard over and over how long the down time will be is always underestimated by those in management positions. Scripps health has increased their estimates of costs of their attack to over $100m now. They had coverage for $20m. That amount covered most of what they consider the actual response costs. In its filing, Scripps says the cost breakdown includes lost revenue of $91.6 million and incremental costs incurred to address the cybersecurity incident and recovery at $21.1 million. Plus, they were down for 25 days.
[34:22] There is a new Ipsos survey that examines the impact of cybersecurity in the healthcare industry, Perspectives in Healthcare Security Report, that was specifically addressing medical devices in healthcare and looking at overall IT spending. There were some interesting and scary numbers from the study. Here a few key findings from the study:Cybersecurity investment not a high priority
Dangerous Vulnerabilities Still Not Dealt With
Cyber insurance and compliance are popular options
These figures can be misleading, if you know how some dashboards are populated. If the dashboard is being populated by a constant discovery scan, then it’s going to also include, potentially, the printers and the IoT devices that it finds. But, so many of these dashboards only include the things that have agents loaded on them. There could be devices that were added to your network that there are no agents on or that you cannot load the agent software on.

Inventory knowledge (or as we like to call it, asset management), is a recognized security practice. It’s a part of every cybersecurity framework you’ll find. If you don’t know what you have, there’s no way you can be sure you are protecting it.
[45:24] The second chart we found interesting, or scary, was regarding questions about budgets for compliance. The first was do you have a specific budget for compliance. 19% of hospitals said No, they don’t have a budget for compliance, while 49% said their budget was not adequate enough.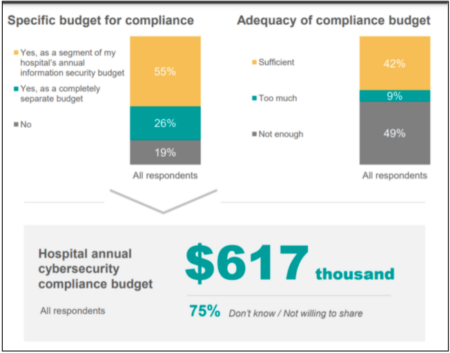
When asked what the hospital’s annual cyber security compliance budget was, they got $617,000. But that’s across all respondents, keeping in mind that 70% of the people said they do not know or they’re not willing to share it. So, even if they are worried about checking the box compliance, but they have no money allocated to actually go check the box. That just looped us all the way back around to where we started this conversation.
Don’t be an ID10T! Take cybersecurity seriously.
Just because you might not be in healthcare, it doesn’t mean that people don’t rely on your services. Your business likely matters to other businesses and your customers. Ransomware does not just affect computers and data. It can affect privacy, safety, wellness, integrity, availability of services, etc for your patients, clients, and customers.
Remember to follow us and share us on your favorite social media site. Rate us on your podcasting apps, we need your help to keep spreading the word. As always, send in your questions and ideas!
HIPAA is not about compliance,
it’s about patient care.TM
Special thanks to our sponsors Security First IT and Kardon.


