
The Department of Labor (DOL) Employee Benefits Security Administration (EBSA) issued its very first cybersecurity guidance in April 2021and they sound remarkably like all the things that we recommend doing under HIPAA, HICP and the NIST cybersecurity framework. Let’s check it out!
In this episode:
DOL Cybersecurity Guidance – Ep 310
Today’s Episode is brought to you by:
Kardon
and
HIPAA for MSPs with Security First IT
Subscribe on Apple Podcast. Share us on Social Media. Rate us wherever you find the opportunity.
The HIPAA Boot Camp
Virtual Edition Aug 17-19, 2021
Great idea! Share Help Me With HIPAA with one person this week!
Thanks to our donors. We appreciate your support!
If you would like to donate to the cause you can do that at HelpMeWithHIPAA.com
Like us and leave a review on our Facebook page: www.Facebook.com/HelpMeWithHIPAA
If you see a couple of numbers on the left side you can click that and go directly to that part of the audio. Get the best of both worlds from the show notes to the audio and back!
HIPAA Say What!?!
[03:28] So, we ran across this post on Twitter by a guy who created a graphic chart giving the differences between HIPAA and HIPPA. Here is a link to the Twitter post and a snapshot of the chart he created.https://twitter.com/davidkfry/status/1402715723437199360?s=12
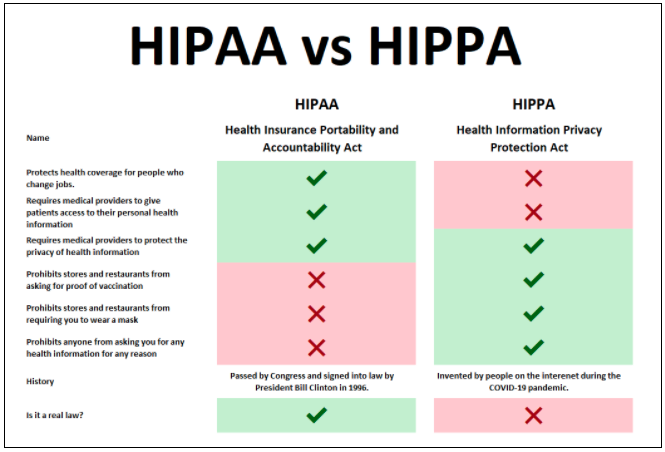
There are some great comments on this post from people and then there are posts from folks who clearly missed the point or didn’t read the entire chart. The list of things in the HIPAA column are correct, of course. But the important thing is what’s included in the last two items:
HIPAA was passed by Congress and signed into law by President Bill Clinton in 1996. HIPAA is a real law.
HIPPA was invented by people on the Internet during the COVID-19 pandemic. And it is NOT a real law.
[09:27] Here’s yet another story of a HIPAA failure out of Georgia. Medical records for hundreds of patients were found dumped along the side of a road in South Fulton County. Apparently, Hope Medical, who has a facility in Stone Mountain, GA, had a fire in their office in 2018 and they moved some of their paper medical records to a storage facility. Fast forward to 2021 and it appears that they were three months behind on their storage unit payment. Then when the money was available to pay the bill, the storage facility basically said that because they were a couple days late paying their bill, they sold off the storage unit.
Hundreds of peoples’ medical records found tossed along South Fulton County road
The people that purchased the unit have zero responsibility to protect its contents. The storage facility is not a BA because when you purchase a storage unit, you have your own private lock. So, the storage facility doesn’t have a key to the unit and the job they do does not require them to access the units.
So, if you have a storage unit full of medical records, you might want to go make sure they are still there and that you pay your bills on time.
DOL Cybersecurity Guidance
[18:05] The Department of Labor (DOL) Employee Benefits Security Administration (EBSA) issued its very first cybersecurity guidance in April and I was very interested to see what it included. I definitely want to know if they are making extra efforts to protect retirement plans!The main document included three very good links that should be used for any business:
- Tips For Hiring a Service Provider With Strong Cybersecurity Practices
- Cybersecurity Program Best Practices
- Online Security Tips
Let’s review these three documents.
Tips For Hiring a Service Provider With Strong Cybersecurity Practices
[21:47] First, it says to not just hire a vendor to do some work. You need to hire a vendor with strong cybersecurity practices. Here are a few of the tips included in this guidance:- Ask about the service provider’s information security standards, practices and policies, and audit results, and compare them to the industry standards adopted by other financial institutions. It points out that you should “look for service providers that follow a recognized standard for information security and use an outside (third party) auditor to reduce your do rate review and validate cybersecurity.” Vendors should be able to tell you that they are following some cybersecurity framework, whether it be NIST CSF, 405d HICP, CIS20 or some other framework.
- Ask the service provider how it validates its practices, and what levels of security standards it has met and implemented. Be careful here that you are asking the right questions. With any kind of compliance standard, there is a defined scope. A company may say they are PCI compliant, but that likely only refers to the computers that process credit card transactions, not the entire network. Also, keep in mind that an assessment of your organization is a snapshot of a moment in time. Everything might look good today, but tomorrow could be a totally different story.
- [32:02] Evaluate the service provider’s track record in the industry, including public information regarding information security incidents, other litigation, and legal proceedings related to vendor’s services. Just because you are working with a vendor with tons of clients across the country, doesn’t mean they are properly protecting your data or using defined security practices.
- Ask whether the service provider has experienced past security breaches, what happened, and how the service provider responded.
- Find out if the service provider has any insurance policies that would cover losses caused by cybersecurity and identity theft breaches (including breaches caused by internal threats, such as misconduct by the service provider’s own employees or contractors, and breaches caused by external threats, such as a third party hijacking a plan participants’ account). Make sure they have coverage, but also that they have enough coverage for the number of clients they have. You don’t want to be battling with all of their clients for that money if something happens.
- When you contract with a service provider, make sure that the contract requires ongoing compliance with cybersecurity and information security standards – and beware contract provisions that limit the service provider’s responsibility for IT security breaches. This speaks to the moment in time problem. Make sure that it requires ongoing compliance with cybersecurity standards. Read the fine print. Just because a lot of practices or other companies use a particular vendor doesn’t mean they necessarily have it all covered.
They also suggest including these terms in the contract that would enhance cybersecurity protections:
- Information Security Reporting – requiring a third party audit to determine compliance
- Clear Provisions on the Use and Sharing of Information and Confidentiality – this typically is included in the BAA in healthcare
- Notification of Cybersecurity Breaches – included in the BAA
- Compliance with Records Retention and Destruction, Privacy and Information Security Laws – included in the BAA
- Insurance – we recommend that it is included in the BAA
Now, you’ve got to dedicate some type of resource to doing this too. This is not easy work. You’ve got to know what you’re looking for. And it’s time consuming. You should go through this every time you need to hire a service provider.
Cybersecurity Program Best Practices
[38:22] The DOL EBSA laid out their cybersecurity best practices for their service providers. They include:- Have a formal, well documented cybersecurity program.
- Conduct prudent annual risk assessments.
- Have a reliable annual third party audit of security controls.
- Clearly define and assign information security roles and responsibilities.
- Have strong access control procedures.
- Ensure that any assets or data stored in a cloud or managed by a third party service provider are subject to appropriate security reviews and independent security assessments.
- Conduct periodic cybersecurity awareness training.
- Implement and manage a secure system development life cycle (SDLC) program.
- Have an effective business resiliency program addressing business continuity, disaster recovery, and incident response.
- Encrypt sensitive data, stored and in transit.
- Implement strong technical controls in accordance with best security practices.
- Appropriately respond to any past cybersecurity incidents.
Do these sound familiar? They should. We’ve talked about every one of these items in previous podcasts, many more than once. Having a formal, well documented cybersecurity program that includes specific policies and procedures (which they include in this guidance) should be part of your formal cybersecurity program. These are all typical policies and procedures you should have under HIPAA too.
Conduct prudent annual risk assessments. Hello! HIPAA! Although they say “annual risk assessment,” they do explain that IT threats are constantly changing and a risk assessment should be done as things change. And of course, you should have a risk management plan to go with your assessment.
All of the items in this list are a part of HIPAA and cybersecurity frameworks. We have covered these topics several times in podcasts over the years. Well, except for #8. If you are developing any in-house applications using any tools, even scripting in Excel or macros, you should have a secure system development life cycle (SDLC) program.
Cybersecurity Program Best Practices
[01:01:19] This is a quick two page that lists ways to help prevent fraud and secure your online presence. They include:- Register, Set Up And Routinely Monitor Your Online Account
- Use Strong And Unique Passwords
- Use Multi-factor Authentication
- Keep Personal Contact Information Current
- Close Or Delete Unused Accounts
- Be Wary Of Free Wi-fi
- Beware Of Phishing Attacks
- Use Antivirus Software And Keep Apps And Software Current
- Know How To Report Identity Theft And Cybersecurity Incidents
These are great tips for businesses and individuals alike. Everyone should consider implementing these ways to help prevent cyber attacks. Like David said… you can’t spell cybersecurity without U!
The DOL’s cybersecurity guidance includes recommendations we’ve mentioned many times in our HIPAA and cybersecurity frameworks discussions. It’s important, not only in the healthcare industry, but within all industries to have a formal cybersecurity program. But having one is just half the battle. It should be well documented so that you can prove it. Because more and more, being able to prove it is key.
Remember to follow us and share us on your favorite social media site. Rate us on your podcasting apps, we need your help to keep spreading the word. As always, send in your questions and ideas!


