We follow a lot of the Ponemon studies. They help us see changes and trends and make better recommendations to our clients. We are going to cover their annual cost of an insider breach study. This global study covers insider incidents and provides five signs your organization is at risk.
We follow a lot of the Ponemon studies. They help us see changes and trends and make better recommendations to our clients. We are going to cover their annual cost of an insider breach study. This global study covers insider incidents and provides five signs your organization is at risk.
In this episode:
5 Signs Your Org Is At Risk – Ep 374
Today’s Episode is brought to you by:
Kardon
and
HIPAA for MSPs with Security First IT
Subscribe on Apple Podcast. Share us on Social Media. Rate us wherever you find the opportunity.
The Privacy and Security Boot Camp
3.5 day In Person Event
Mar 12, 13, 14 and 15, 2023
PriSecBootCamp.com
Great idea! Share Help Me With HIPAA with one person this week!
Learn about offerings from the Kardon Club
and HIPAA for MSPs!
Thanks to our donors. We appreciate your support!
If you would like to donate to the cause you can do that at HelpMeWithHIPAA.com
Like us and leave a review on our Facebook page: www.Facebook.com/HelpMeWithHIPAA
If you see a couple of numbers on the left side you can click that and go directly to that part of the audio. Get the best of both worlds from the show notes to the audio and back!
HIPAA Say What!?!
[03:16] Scenario: A patient sends an email to someone at the medical office asking a question about their treatment. Do we need to get authorization to reply to their email?First, there is a FAQ on the HHS site (created in 2008) on this topic:
570-Does HIPAA permit health care providers to use e-mail to discuss with their patients | HHS.gov
I can see the confusion in this scenario, though. Here is my answer: If the patient is initiating the conversation via email, the very first part of the conversation, I say you need to get confirmation that they understand that email is not secure. You don’t have to get confirmation in writing. My suggestion is to make a script so that you know what was said. Write it down and make sure everybody knows to read this anytime they receive a verbal request for PHI to be sent via unsecured email. Then make sure you document that you read the script to them in their chart.
If a request like this is received from the patient via email, you can just simply reply by sending the script you created and a message asking them to confirm their email address is correct and that they understand that this is not considered secure email.
And, I also recommend you explain that if they want to stop you from sending this kind of information via unsecured email, then they need to let you know. So, now you’ve got everything you need and should document it on the patient’s account and attach the email consent.
We don’t want to impede the patient’s ability to get their information if they don’t care about security.
405(d) Tip of the Week
[08:05] This month’s HHS 405(d) Spotlight webinar is on the legal implications of a cyber attack. It is important for everyone to understand what that means. The webinar is an hour long, by now it is a recorded webinar that you can implement into your security training program. The webinar contains several points, so you can break it up and train your team in weekly five minute discussions or emails or whatever training method works best in your organization.Go to 405d.hhs.gov to sign up for the notifications as to when 405(d) is having their spotlight webinars. They always have great information in them and sometimes they are even funny.
5 Signs Your Org is at Risk?
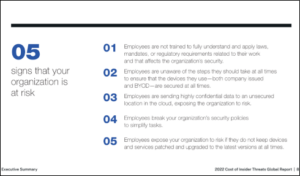
[10:16] We follow a lot of the Ponemon studies. They have a solid methodology behind their studies and they do an annual study on a lot of things that help us see changes and trends and help us to make better recommendations to our clients. One of the many that we follow is the cost of an insider breach. Occasionally, they do studies that specifically target the healthcare industry. But this one is the broader global evaluation and that’s important because that’s where you’re going to see the trends.2022 Ponemon Cost of Insider Threats Global Report | Proofpoint US
The info for this study was gathered over a two-month period (Aug/Sep 2021). The data included responses from 278 separate organizations in total of 1,004 interviews were conducted with IT and IT security practitioners in these organizations. This included information on 6,803 insider incidents the organizations experienced.
Insiders Are A Risky Necessity
[12:56] Remember the insider threats come in lots of different sizes and shapes. The report included cases where a careless or negligent insider (employees and contractors) were responsible for an incident as well as malicious insiders and those finally the cases of credential theft. The theft part is tough because the attack is technically done by an outsider, but without the insiders creds it would never have happened.The first information we need to all note from this study is that the most prevalent of the three included types are those involving careless or negligent insiders – 56% of all incidents. Next is the criminal insider at 26%. At first glance, these two are the ones we should make every effort to prevent from occuring or limit the blast radius of one when it occurs.
By looking into the credential theft issue (18%) when added to the negligent incidents you cover 74% of the incidents. More importantly you aren’t dealing with internal criminals which is very hard to even think about for many organizations.
Based on the findings, we also see that we are not making progress to prevent them from occurring. Last year the study found it took 77 days to contain one of these incidents and that now went up to 85 days. In fact, only 12% were contained in 30 days or less. The number of days went up because there are still 34% that take longer than 90 days to contain them. Keep these numbers in mind when you are evaluating your detection methods and especially in your incident response planning.
[18:43] Not surprising the two factors that turn out to be the most expensive in one of these incidents are the impact of business disruption due to diminished employee productivity (23 percent of total cost) and technology, which includes the amortized value and licensing for software and hardware that are deployed in response to insider-related incidents (21 percent).These numbers look bad enough and then add the point that the overall costs continue to climb. We know big numbers in the headline like $22.68M attributed to the costs when the organization has more than 75K employees. Working with that huge number just puts the conversation beyond many businesses. The other number is much more concerning. These incidents with companies with less than 500 employees average annual costs due to insider issues of $8.13M. Just assume it will cost you way more money than anyone wants to talk about when these things go awry.
[25:45] Email is still a big issue in these cases. Email is one of those things we can’t get rid of but it sure does make life complicated. Check out two of interview response notes they featured:Most sensitive data is in employees’ email. Sixty-five percent of respondents say email is where employees store their organizations’ most sensitive data such as personally identifiable information (PII), intellectual property (IP) and other critical business information.
Malicious insiders use corporate email to steal sensitive data. Seventy-four percent of respondents say malicious insiders emailed sensitive data to outside parties followed by scanning for open ports and vulnerabilities (62 percent of respondents) and accessing sensitive data not associated with the role or function (60 percent of respondents).
The report is loaded with some other great information so we encourage you to take the time to review it yourself if you think it may be helpful to you. For example, tidbits like the number one business driver behind the insider threat management program: 57% – Past incidents at your peers’ or at your organization.
[35:01] To close out this part of the discussion lets review the reports graphic showing the 5 signs they identified as indicators that your organization is at risk.- Workforce training – Lack of training is a problem. Don’t just train on the HIPAA basics. All staff need to have security awareness training.
- Device security – This goes back to training. Staff need to understand the security safeguards in place on devices as well as how to protect and secure them themselves.
- Shadow IT – Many times staff upload documents to free Dropbox accounts or their free personal Google accounts or something in order to work from home on them. Basically, they figure out a way to get around your security safeguards to do what they want to do. It exposes PHI or other sensitive online insecurely.
- Security policies ignored – This comes back to shadow IT. If you tell someone they can’t do something and walk off, watch out. They will likely try to do it anyway. Find out what it is that they are trying to accomplish and figure out whether there is a way to help them accomplish that task in a secure manner.
- Patch Management – Can you confirm your IT staff is patching everything? Most likely they are not. You need to work with IT and find out what they are doing regarding patch management of EVERYTHING! You might be shocked to find out what is and what is not being patched.
Insider threats can come from careless or negligent employees or contractors, criminal or malicious insiders and/or credential thieves. If you have given them access to your data or systems, they are an insider. So, understanding the risks insider threats pose to your organization and how to mitigate them is key.
Remember to follow us and share us on your favorite social media site. Rate us on your podcasting apps, we need your help to keep spreading the word. As always, send in your questions and ideas!
HIPAA is not about compliance,
it’s about patient care.TM
Special thanks to our sponsors Security First IT and Kardon.