
It is time to review the annual Verizon Data Breach Investigation report. First, we will hit the big notes from their summary. Then, we can add in a few tidbits from the bigger report details. We’ll break down key statistics, discuss emerging threats, and offer insights into what these findings mean for the health sector and HIPAA privacy and security programs.
In this episode:
Verizon DBIR 2024 Review – Ep 459
Today’s Episode is brought to you by:
Kardon
and
HIPAA for MSPs with Security First IT
Subscribe on Apple Podcast. Share us on Social Media. Rate us wherever you find the opportunity.
Great idea! Share Help Me With HIPAA with one person this week!
Learn about offerings from the Kardon Club
and HIPAA for MSPs!
Thanks to our donors. We appreciate your support!
If you would like to donate to the cause you can do that at HelpMeWithHIPAA.com
Like us and leave a review on our Facebook page: www.Facebook.com/HelpMeWithHIPAA
If you see a couple of numbers on the left side you can click that and go directly to that part of the audio. Get the best of both worlds from the show notes to the audio and back!
Thanks to our donors.
HIPAA Briefs
[02:45] Gap analysis vs SRA and risk management plan reviews.A HIPAA gap analysis and a SRA both aim to strengthen an organization’s data protection practices, but they focus on different aspects. A HIPAA gap analysis specifically looks at how well an organization’s policies and procedures align with the requirements of the HIPAA regulations. It identifies areas where the organization falls short of HIPAA’s standards. On the other hand, a security risk analysis is broader. It assesses the overall risks to the security of patient information, considering potential threats and vulnerabilities, and evaluates whether the existing security measures are adequate. This analysis is crucial not just for compliance with HIPAA, but for ensuring the integrity and security of patient data against all sorts of risks.
It’s really important to keep your security risk analysis and risk management plan updated because it’s like a living document that grows and changes with your organization. This documentation acts as a guidebook, showing you how to handle vulnerabilities that pop up, ensuring that you’re always on top of your game. And part of that assessment of where you are and how your program is can be the gap analysis.
Your risk management plan has to be based on the actual SRA, which is evaluating the threats and vulnerabilities and what you need to worry about. Your risk management plan then identifies how you’re going to reduce those risks. That’s your residual risk. A gap analysis shows you how you’re doing on making sure that you’re meeting your compliance obligations. All different things, but the same process.
405(d) Tip of the Week
[12:15]How to Implement Data Classification new poster to explain the concepts.
Doing this step is invaluable in your SRA. Make sure you use this one-pager to address all of your data in the way you should.
Verizon DBIR 2024 Review
[14:57]DBIR Report 2024 – Summary of Findings | Verizon
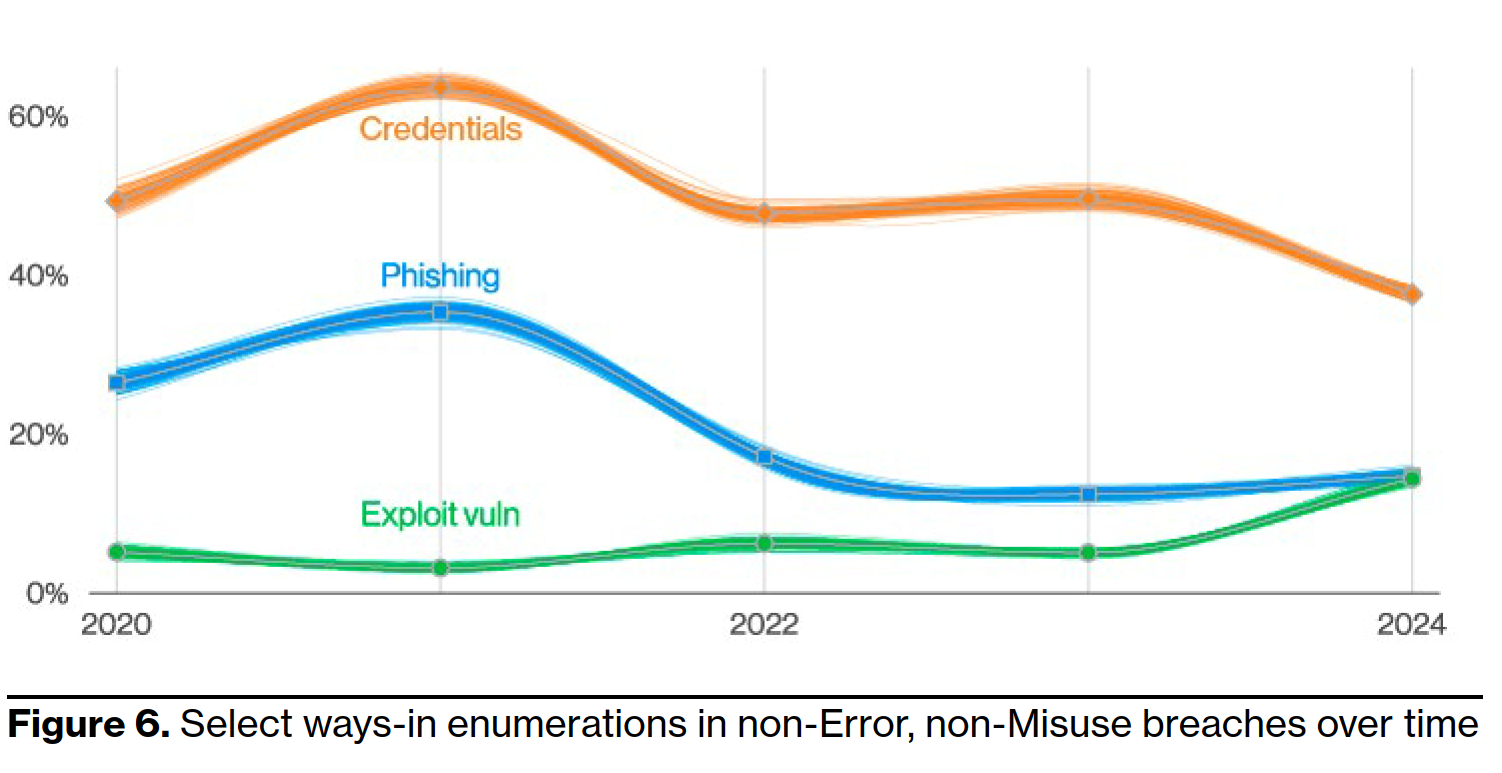
This year’s report looked closely at the ways-in and actions taken to make the data breaches happen. In the ways-in analysis there was a 180% increase year over year exploiting a vulnerability in software. As they point out, that was likely due to the number of attacks that came from the MOVEit vulnerability alone. That one all by itself accounts for thousands of business attacks. In this report they identified 1,567 breach notifications that specifically mentioned MOVEit. It will be interesting to see if it drops precipitously in next year’s report. The most likely way in is stolen credentials followed by phishing. The question remains for me: did the credentials get stolen by a phishing attack first?
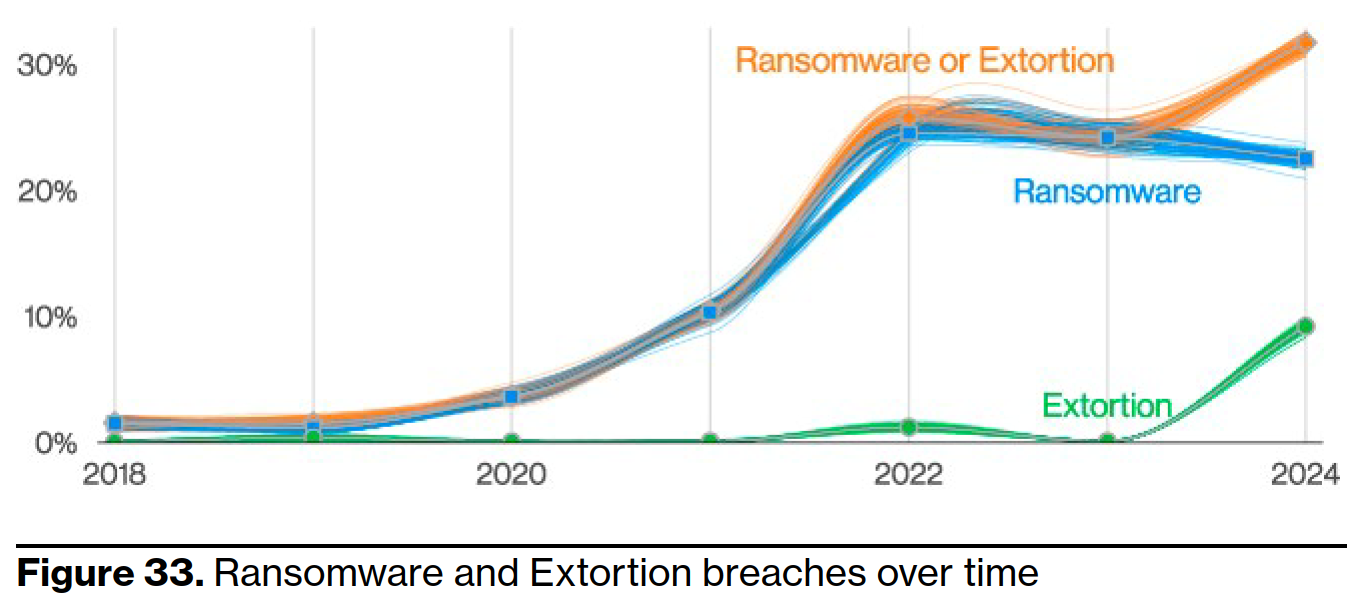
Also, not a shock is the ransomware rules with about one-third of all breaches being ransomware and/or some other form of extortion. It is interesting to note they are breaking that out to see if extortion alone without the traditional encryption of the systems continues to grow. In fact, overall ransomware attacks dropped slightly but extortion-only attacks grew by 9%. Those are the ones I think happen much more often than we know about. If the data is stolen and a ransom is quietly paid without systems being impacted it is a lot easier to keep that one under wraps with a small number of insiders aware of it. Usually, folks who have also signed an NDA.
It’s the people, people.
[29:17]I have always tried to get this message across and am happy to see that some are starting to notice it. Although it is very frustrating for me when they tell me about it like it is amazing new information. Reference episode 20 of this podcast in Sept 2015: HIPAA Security Awareness: It’s The People, People now that I have that one out of my system. It is good to see the team that does this report has made a change in their calculations to make it easier to track malicious Privilege Misuse.
We have revised our calculation of the involvement of the human element to exclude malicious Privilege Misuse in an effort to provide a clearer metric of what security awareness can affect. For this year’s dataset, the human element was a component of 68% of breaches, roughly the same as the previous period described in the 2023 DBIR.
Even with moving that number out of the total humans were a component in 68% of the breaches they reviewed. It did not change the picture. They are also looking at cases that involve a supply chain issue causing breach (15%). Vendors with a major vuln like Progress Software and its MOVEit one may not seem like it goes in the human element to some. But, the human is the one involved in those vulns. At least for now.
Another one that they are now tracking is when a breach involves just human error (28%). Errors caused a significant number of breaches. For all of those folks who are too busy to review your work or too busy to complete a checklist or know how to do it so well you don’t need a checklist, make note. You have a 28% chance of being the one that causes the next data breach.

As they point out so nicely:
End-user (in VERIS parlance, an average employee or contractor of an organization) has grown a lot, more than doubling from 11% to 26%. Those were mostly involved in Misdelivery errors and were part of the same growth in the Miscellaneous Errors pattern we discussed above. All in all, it’s been an upsetting year for all detail-oriented perfectionists out there.
Once they get those credentials they are hitting web-based applications most of the time. The phishing and vulns are next but a separate point on the credentials for desktop sharing software deserves a moment just based on how often we still run into this problem.
Do not use desktop sharing software without MFA turned on. In fact, if you are going to use desktop sharing software, do it behind a VPN rather than a direct connection from the internet. In the report they point out that the VPNs may have some vulnerabilities but nothing compared to the web applications as the opening for the bad guys to get in.
Supply chain is getting noticed
[38:42]They have now broken out a new category for them to track and included data going back to 2021. Their new supply chain interconnection tracking shows a jump from 4% to 16%. What is included here:
For a breach to be a part of the supply chain interconnection metric, it will have taken place because either a business partner was the vector of entry for the breach (like the now fabled heating, ventilating and air-conditioning [HVAC] company entry point in the 2013 Target breach) or if the data compromise happened in a third-party data processor or custodian site (fairly common in the MOVEit cases, for instance). Less frequently found in our dataset, but also included, are physical breaches in a partner company facility or even partner vehicles hijacked to gain entry to an organization’s facilities.
That makes sense but they are expecting to catch some heat because they are also including exploitation of vulns in there. It only makes sense because these data breaches are reported by the software vendor except in maybe a very rare case. I actually think this is the part of the supply chain discussion that should get the most attention:
This metric ultimately represents a failure of community resilience and recognition of how organizations depend on each other. Every time a choice is made on a partner (or software provider) by your organization and it fails you, this metric goes up. We recommend that organizations start looking at ways of making better choices so as to not reward the weakest links in the chain. In a time where disclosure of breaches is becoming mandatory, we might finally have the tools and information to help measure the security effectiveness of our prospective partners.
A whole new world to them is to start tracking the vulnerabilities themselves. The numbers they found show that patching is just not happening fast enough. They found it takes about 55 days to get a patch out for 50% of the critical vulnerabilities published by CISA in their catalog of Known Exploited Vulnerabilities (KEV).
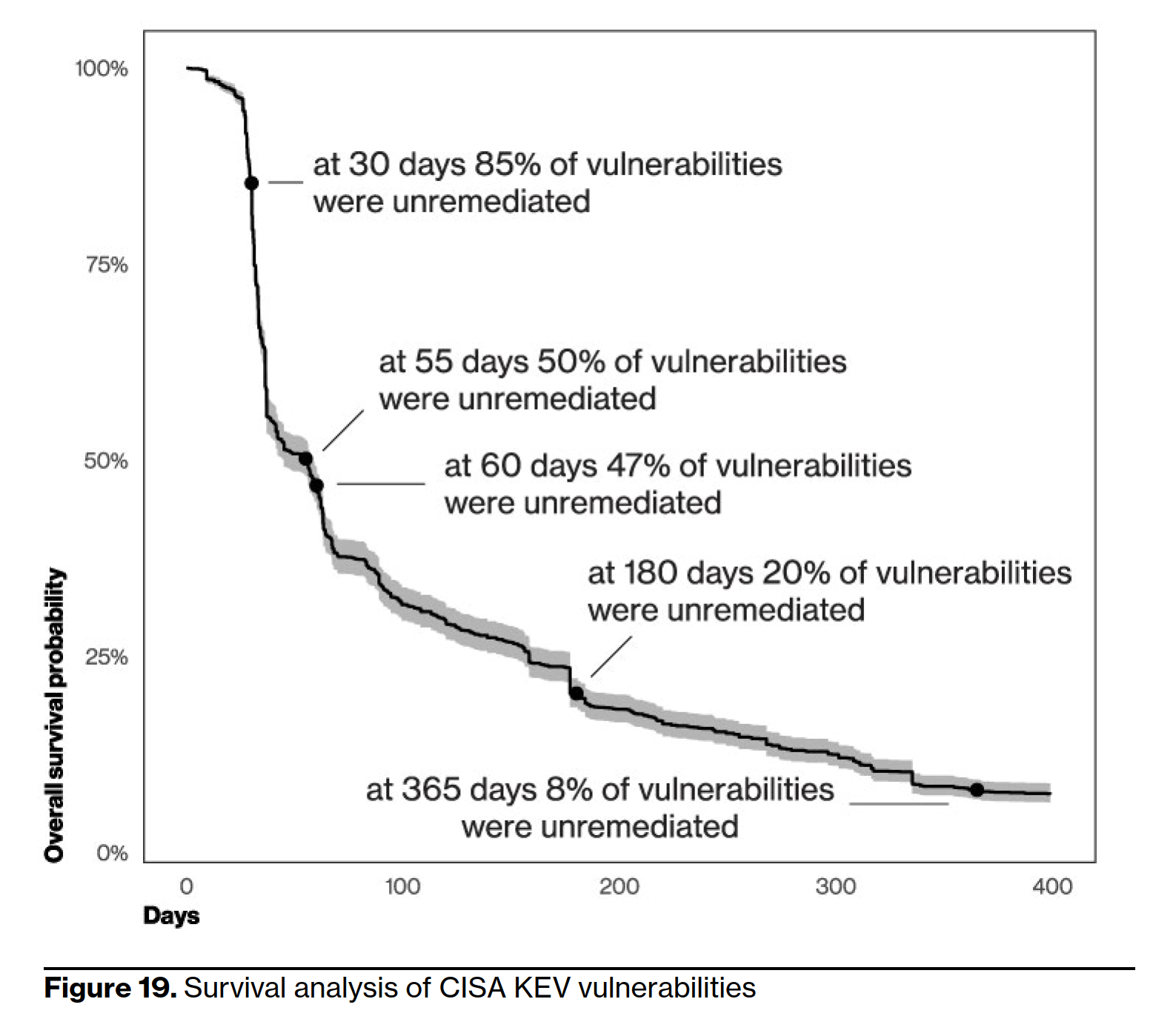
This means we are taking way too long to get these patches out in the wild and the attackers are very well aware of it. Once a zero-day is identified in the high vuln KEV it takes about 5 days for them to start using it. Those must be handled ASAP.
What is most concerning is they point out that this data only shows the companies who are taking care of patching at all. It doesn’t show ones that aren’t getting patched.
Even though this survival analysis chart looks bleak, this is the optimist’s view of the situation. We must remind ourselves that these are companies with resources to at least hire a vulnerability management vendor. That tells us that they care about the risk and are taking measures to address it. The overall reality is much worse, and as more ransomware threat actors adopt zero-day and/or recent vulnerabilities, they will definitely fill the blank space in their notification websites with your organization’s name.
Good news on the AI front
[50:34]The obligatory discussion of AI came in there too. Actually, with some really good news. Well it is good news if you take action now. You can get ahead of the curve.
From our perspective, the threat actors might well be experimenting and trying to come up with GenAI solutions to their problems. There is evidence being published of leveraging such technologies in “learning how to code” activities by known state-sponsored threat actors. But it really doesn’t look like a breakthrough is imminent or that any attack-side optimizations this might bring would even register on the incident response side of things. The only exception here has to do with the clear advancements on deepfake-like technology, which has already created a good deal of reported fraud and misinformation anecdotes.
Healthcare good news and not so good news
[54:44]Some interesting information popped up. One thing is certain – I use the phrase “everything is personal when you are a person” in training often. Yep, it is all about the person and personal data. The top few items of note:
- Insiders deliberately causing breaches have surged back into second place after a steady decline since 2018.
- Personal data has eclipsed Medical data as the preferred target for threat actors.
- System Intrusion breaches remain in the top three attack patterns.
- We have one error that most don’t – Gaffe (people just blurt out stuff where others can hear it causing a data breach)
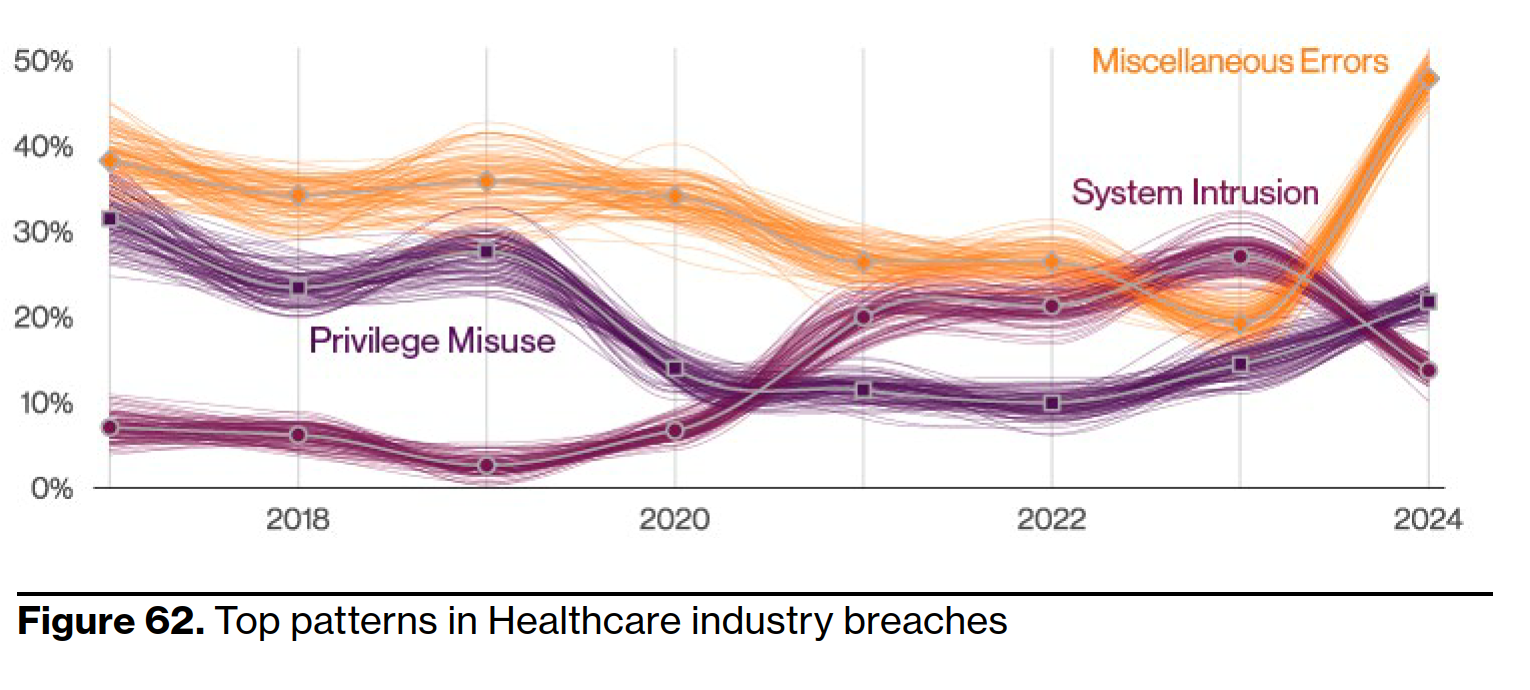
The Error number is the biggest problem and misdelivery is the most common error. Sending information to the wrong person. Again, take a few seconds to double check things when working with PHI, PII or security specific things (configurations and loading software for example).
On the data front that is the best news really. Medical data isn’t the most important. However, we have way more personal data than most other industries plus our personal data never seems to be purged! Again, they add a fun comment though:
There you have it folks! Remember to keep those Risk Assessments thorough, watch out for those pesky human errors, and always strive to improve your security measures.
Remember to follow us and share us on your favorite social media site. Rate us on your podcasting apps, we need your help to keep spreading the word. As always, send in your questions and ideas!
HIPAA is not about compliance,
it’s about patient care.TM
Special thanks to our sponsors Security First IT and Kardon.


